Why choose us?
We provide a range of services to a huge variety of organisations. So, whether that’s helping you on your security maturity journey, becoming or staying compliant, testing the robustness of your systems and infrastructure, or responding to an incident, we’ve got you covered.
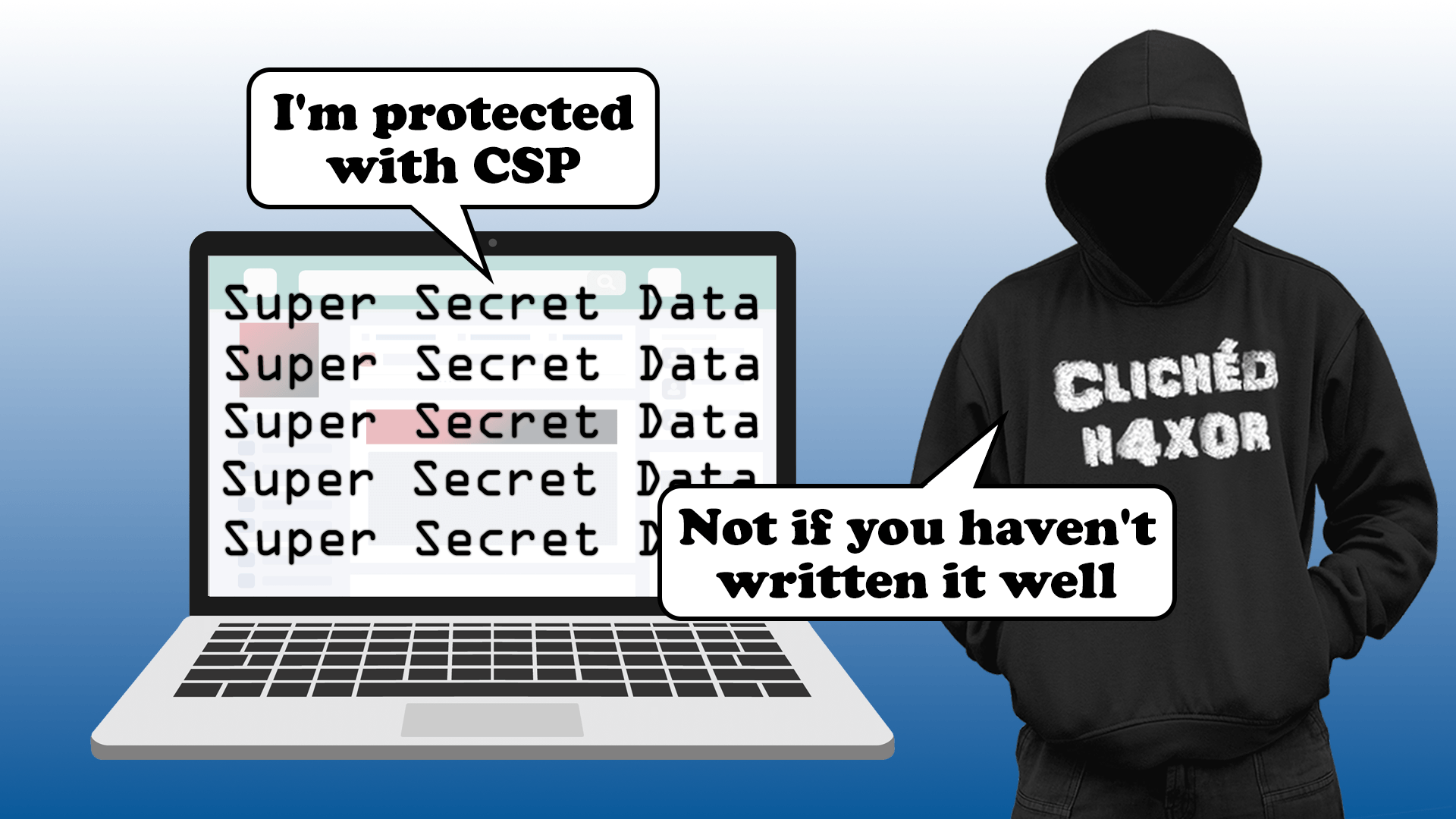
The PTP security blog
Here we share our research, insights, experience, knowledge, and opinions. No paywall. No subscription. It’s all free.
- DFIR
Sil3ncer Deployed – RCE, Porn Diversion, and Ransomware on an SFTP-only Server
7 Min Read
Jul 11, 2025
- Automotive Security
How we turned a real car into a Mario Kart controller by intercepting CAN data
9 Min Read
Jun 26, 2025
Events and Speaking
We regularly speak at events, sharing our latest research, insights, and expertise.
Whether you need expert cybersecurity advice or want to learn more about our services, we’re here to help. Contact us and we’ll connect you with the right person.
UK Office
Pen Test Partners LLP, Unit 2, Verney Junction Business Park, Buckingham, MK18 2LB, UK
US Office
Pen Test Partners Inc, 222 Broadway 22nd Floor, Suite 2525, New York, NY 10038, US