I don’t know about you, but to me it seems that every week we are seeing another vulnerability that not only grants significant access to the vulnerable system but also more widely internally.
This last week we have seen the latest round of Microsoft Exchange vulnerabilities. The April 2021 update fixed 4 responsibly disclosed vulnerabilities. It was so severe that the US CERT CISA issued an update to its emergency directive for all Federal agencies to patch their services within 3 days. This just ONE month after they issued the first emergency Exchange directive for the now infamous HAFNIUM Exchange attack.
One week later they are again issuing an alert to patch Pulse Connect Secure after a CVSS 10 critical remote code execution vulnerability was discovered being actively exploited in the wild.
Before those three there was the SolarWinds attack, which the US Government indicate was performed by a nation state and carried out to attack US Government services.
That’s three (four if you count the updated Exchange one) emergency directives in the first 4 months of 2021. To put it in perspective, they only released 4 in all of 2020, just 2 in 2019 and 2018 and only one in 2017.
Along with those the CISA have alerted to there are other vulnerabilities involving infrastructure, including two affecting SonicWall firewall appliance. The first of which was fixed in February and was being actively exploited according to the Japanese CERT. The second affects the SonicWall email security product, allowing an unauthenticated attacker to create an admin account and then login with that admin account. Again these are being exploited publicly.
Our very own Vangelis found an IDOR in the SonicWall cloud service last year that could let him trivially compromise ~500k customers.
These are huge vulnerabilities, affecting many services and providing significant access to the affected services and networks. Are we entering the age of the ‘Super Vulnerability’?
Certainly, there have been other super vulnerabilities before that had massive impact, many with high levels of access, for example, EternalBlue, the Windows 7 vulnerability that was used in the NHS crippling Wannacry ransomware attack, however, commonly these affect the end user computing environment.
One historic infrastructure level vulnerability is of course Heartbleed, although we still occasionally see this now, it’s very rare and the exploit was much more of an information disclosure issue than a trivial RCE. The more recent crop of super vulnerabilities seem to focus much more on infrastructure and most are coming accompanied with working reliable exploit code. The idea being break once, run everywhere.
Threat actors
Its understandable that these systems are targeted, one attack can leverage huge amounts of data and access. That’s very useful to certain threat actors.
This leads on to the threat actors involved in carrying this out. Looking at the information available for the four vulnerabilities CISA mention, starting with SolarWinds:
The US Government directly attribute this to hacker groups connected with the Russian Government, even going as far as imposing sanctions.
With last month’s Exchange vulnerability Microsoft suggested it was carried out by HAFNIUM, which they think is a state sponsored Chinese based hacking group.
This months Exchange vulnerability was disclosed to Microsoft by the US National Security Agency, although its not known if it was actively exploited by the NSA prior to disclosure. However, they have a history of creating attacks from remotely exploitable code – EternalBlue was a leaked NSA developed exploit.
Then the Pulse Connect Secure attack has been used by attackers who Mandiant suggest are a Chinese state sponsored hacking group called UNC2630.
The common theme here is state sponsored hacking groups.
But I’m not a target
You may be sat there thinking well I’m not a target of nation states so its much less of a risk to me. This is a mistake.
We are now seeing that the March Exchange vulnerabilities are being exploited by crypto miners. So after all the data has been stolen and the more sophisticated attackers have had the most use out of the services, its time for the miners to exploit the resources.
More and more we are seeing network infrastructure being targeted, whilst phishing and credential stuffing sit firmly at the top of the list of attack techniques, more and more of our breach investigations involve infrastructure attacks.
Recently, a client contacted us because a piece of network hardware had been compromised, using valid credentials found through an unpatched (though not 0-day) flaw the attackers managed to gain access through a VPN, fortunately the MFA in place prevented the access to the network. It could have been much much worse.
What can I do?
Fixing these issues is easy in principal, through patching.
But that can be really hard when dealing with services that are critical to the business such as Exchange. It needs planning. When we applied the patch for the March Exchange vulnerabilities it caused 2 days’ worth of email access problems.
Our awesome IT people worked day and night to resolve it. It can be hard, but the patches need to be applied. The time between patch and exploit is getting much, much shorter, no longer is 30 days acceptable for critical patches.
Cyber Essentials requires 14 days, but as highlighted above, the US Government mandated 3 days for one Exchange issue. They even went as far as directly attacking compromised US corporate servers and removing the malware and backdoors created – though not actually patching the servers.
Many security professionals are now suggesting that running your own Exchange server is too high risk. Can you deploy patches on day zero? Do you have extensive monitoring? Exchange Online will commonly be heavily monitored with millions of data from other clients helping feed the intelligence platform. Patches get applied instantly.
It could be time to consider if Exchange Online is better suited for your business, although this needs careful planning and consideration, we have helped many clients navigate the numerous pitfalls while managing a secure migration. If you are already using Office 365, it’s worth auditing your existing set up before migrating over to make sure you aren’t going to expose your data.
Other controls
There are other compensating controls you can apply too, for some of the vulnerabilities above, using MFA will help mitigate the threat, but this is not a silver bullet. Password quality is also important. If you have weak easily guessable or previously breached passwords attackers only need the MFA token, some careful SMSishing or targeted social engineering can often get staff to leak these.
It’s worth noting that migrating to Office 365 doesn’t suddenly fix your issues either and its potentially easier for attackers to build information about you. You can easily discover if someone is using Office 365 and to what degree with this URL. Edit the “randomemail” with an random email of the domain you want to investigate:
A domain not on Office 365
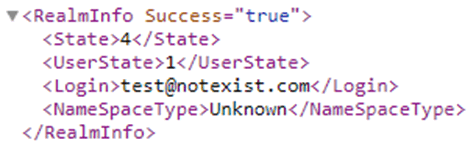
A domain using Office 365, but not federated and so likely not using Exchange Online or Azure AD
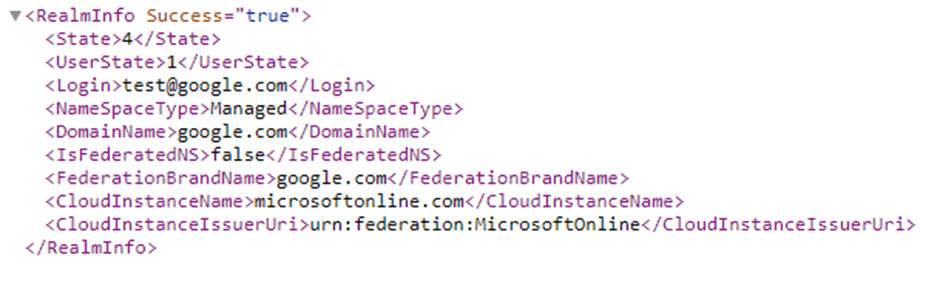
A domain fully federated and likely using Exchange Online and Azure AD
Much more information can be obtained by knowing what you are presenting to the internet. Many IT departments have no idea what they are leaking. They think they know what is publicly available until someone comes along and compromised it – Talk Talk is a great example here. So perform some OSINT on yourself, understand your company’s Operations Security (OPSEC).
What are you giving away?
I’ve lost count of the number of times I have found systems when doing OPSEC assessments for clients that they had no idea existed, nor how seemingly innocuous issues could be chained together and exploited by attackers. I’m going to write more on this in the future so keep an eye out for those posts.
Is 2021 the year of the super vulnerability?
The super vulnerability is here to stay that much is understood and I think it’s clear we will see more and more of these this year.
IT teams will have to get better at patching and monitoring of their networks, what worked well over the last few years will need improving. That may mean moving to a service you don’t need to manage patching and monitoring of such as Exchange Online. Doing that securely is critical, but also knowing what you are leaking and how it can be abused is equally critical.