Before I get going it needs to be said that this post is not about bashing GoPro. It just so happens that the issue I found was prompted by looking at the GoPro software update process.
The issues I found are common in LOADS of other pieces of software as well. Anyway, here goes…
(There’s a corresponding video here as well BTW)
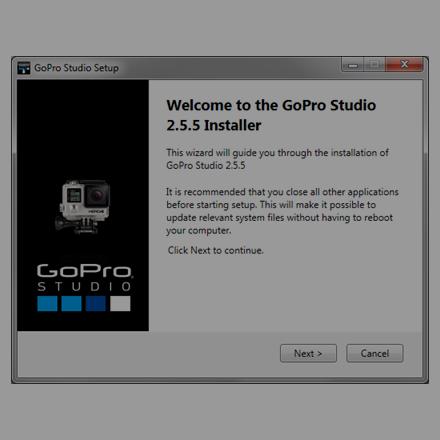
After switching on my laptop the other day, I had the following pop-up on my desktop:

Now being a responsible techie that likes to keep my software up to date for security reasons, I was all up for installing the new update. However as we’ve been playing with GoPros a bit lately I decided to assess the update process.
What’s the deal here?
So first question: How does GoPro Studio know there’s a newer version available?
Well, the software makes the following PLAINTEXT request over HTTP:
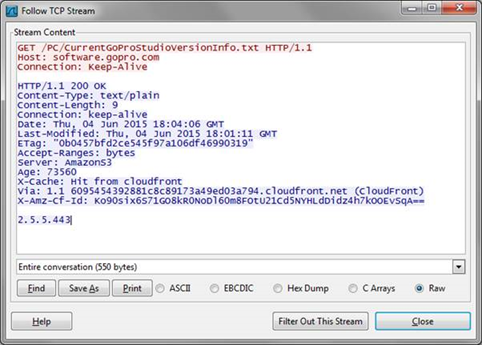
Great, with a bit of DNS fudgery we could serve a response to this request with a higher version number making the software think there is an update.
So now the software knows there’s a new version out there it presents the user with the option to upgrade using the following dialogue:
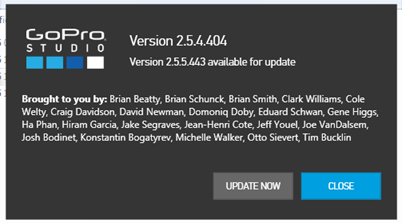
Selecting ‘update now’ simply opens your default browser and navigates to the following URL (in this example):
http://software.gopro.com/PC/GoProStudioPC-2.5.5.443.exe
Note the HTTP again.
As we can see, the executable is served over the internet in plain text:
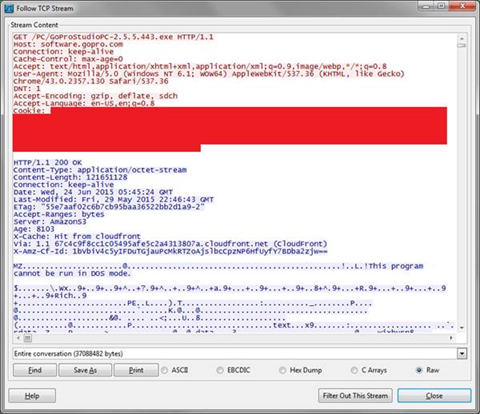
So we could just as easily send over a Meterpreter shell or some other nasty surprise to our victim.
The user would be presented with the following dialogue before updating:
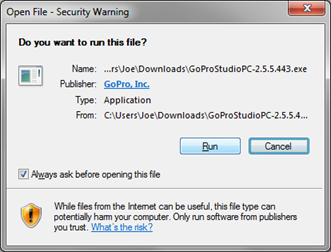
But honestly, how many people click the publisher link and verify their installs? Almost anyone would click ‘run’ in this situation.
And voila, the update runs:

It’s fairly easy to add malicious code into pre-existing binaries and therefore we could abuse this to introduce backdoors to the victim whilst also letting them update their GoPro Studio software at the same time.
Now this isn’t new. In fact there’s a framework for exploiting these types of issues called EvilGrade:
https://github.com/infobyte/evilgrade
This makes it trivial to intercept requests for software updates and to serve up malicious updates.
What can be done?
Well, all updates should really happen over encrypted channels like HTTPS. This will help prevent attackers from intercepting these updates.
In summary, we spend a lot of time pushing people to update software to the latest version for security reasons, but this is a gentle reminder that the update mechanisms themselves need to be secure.