There was a conversation internally about virtualization. This led me to looking at hypervisors. One of which is the Linux Kernel Virtual Machine (KVM).
This is hosted here https://www.linux-kvm.org/
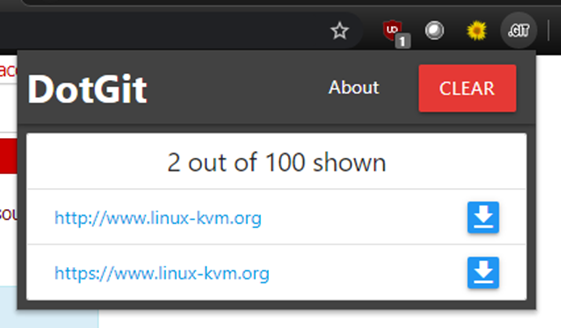
So off I go to their site, and one of my chrome plugins fires up with the following:
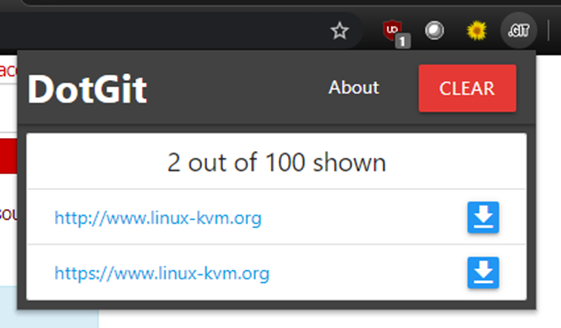
This chrome plugin checks sites for the presence of a /.git/ folder in the root of sites that you visit.
This plugin has a lot of false positives, but I clicked the download link regardless, and low an behold it grabbed a bunch of files which describe how git is being used and points to the git repository that holds the code.
So now that we know that there is a /.git/ entry, let’s check it out (pun intended):
First, I mirrored the /.git/ folder contents:
╭─joe@warrior ~/kvm-git ╰─$ wget https://www.linux-kvm.org/.git --mirror -I .git
Then I checked out the git repository using that information:
╭─joe@warrior ~/kvm-git ╰─$ git clone www.linux-kvm.org/.git
Now, what do we have?
╭─joe@warrior ~/kvm-git/kvm
╰─$ ls -la
total 1224
drwxrwxr-x 20 joe joe 4096 Apr 7 17:11 .
drwxrwxr-x 4 joe joe 4096 Apr 7 17:28 ..
drwxrwxr-x 5 joe joe 4096 Apr 7 17:11 [redacted]
-rw-rw-r-- 1 joe joe 4425 Apr 7 17:11 [redacted]
-rw-rw-r-- 1 joe joe 967 Apr 7 17:11 [redacted]
-rw-rw-r-- 1 joe joe 101634 Apr 7 17:11 [redacted]
drwxrwxr-x 2 joe joe 4096 Apr 7 17:11 [redacted]
-rw-rw-r-- 1 joe joe 2421 Apr 7 17:11 [redacted]
-rw-rw-r-- 1 joe joe 70139 Apr 7 17:11 [redacted]
-rw-rw-r-- 1 joe joe 19419 Apr 7 17:11 [redacted]
-rw-rw-r-- 1 joe joe 4148 Apr 7 17:11 [redacted]
-rw-rw-r-- 1 joe joe 7757 Apr 7 17:11 LocalSettings.php
drwxrwxr-x 17 joe joe 12288 Apr 7 17:11 [redacted]
drwxrwxr-x 3 joe joe 4096 Apr 7 17:11 [redacted]
-rw-rw-r-- 1 joe joe 4 Apr 7 17:11 [redacted]
[etc]
Oops. That’s 300MB of stuff that I really shouldn’t have.
I did a little digging and the LocalSettings.php file highlighted above contained a lot of sensitive information.
This had lots of nice info in, including the MediaWiki secret key and upgrade key (which could be used to compromise the site):
$wgSecretKey = "48[***********REDACTED****************]e2"; $wgUpgradeKey = "ee[redacted]94";
Details of the back-end MySQL database:
Database settings $wgDBtype = "mysql"; $wgDBserver = "[redacted]:3306"; $wgDBname = "[redacted]"; $wgDBuser = "[redacted]"; $wgDBpassword = "[redacted]";
And the password for the email address of the contact at Red Hat.
Yup, full access to an @redhat.com email address.
#SMTP settings for Mailgun $wgSMTP = array( 'host' => 'ssl://smtp. [redacted].com', 'IDHost' => '[redacted].com', 'port' => 465, 'username' => '[redacted]@redhat.com', 'password' => '[redacted]', 'auth' => true );
I did not check to see if the password was current, as this would be overstepping the line. Everything done at this point was achieved through downloading publicly available data.
Being a security consultant and not a hacker, I immediately emailed the contact who replied and fixed the issue all within a 30-minute period:
![]()
Thank you Joe, I really appreciate the detailed explanation.
I understand what the problem is, the .git folder should not be uploaded.
I will fix my scripts and delete the folder from the server.
Thanks again
![]()
So what have we learned?
Git is a version control system, and stores a lot of info about the project in a hidden /.git/ folder.
If you upload the entire directory to somewhere publicly accessible and include this folder than you are disclosing a wealth of information.
This is nothing new. Here’s a post from Threatpost talking about the issue in 2018, but it goes back way further than that: https://threatpost.com/open-git-directories-leave-390k-websites-vulnerable/137299/
So check your sites for the /.git/ folder.
If it exists remove it and ensure that any passwords that are listed are changed.
If you are vulnerable it is also recommended that an investigation is carried out to ensure you haven’t been compromised already. Grepping your log files for /.git/ would be a good start.