Good passwords are strong, even if they’ve been stolen in (most) breaches
Since my post about trivial cracking of passwords based on concatenating dictionary words in the style of XKCD’s correcthorsebatterystaple courted considerable feedback, some controversy and bad math, here’s a follow up and clarification.
First, one point that wasn’t made clear in either the XKCD piece or explicitly clear in mine. I was talking about the theft of password hashes from a breach. There’s a very big difference between online and offline cracking of passwords. Rough explanation:
Online cracking: attempting to guess the password by entering in to an online interface, such as a web application. This is usually very slow in brute force terms; internet and application latency will slow you down to the point where even a simple dictionary attack will take a while. Lockouts, time outs, CAPTCHAs and more will make the attack tough. Decent monitoring by the web site owner should block such actions too.
In this case, correcthorsebatterystaple looks like quite a good password, assuming you aren’t actually using that exact password, as it’s in most of the basic wordlists now!
All of the above can be worked around, and there are many cases where you can successfully compromise accounts, but these tend to be the exception unless the passwords are really simple or re-used. That said, we recently investigated a card data breach where a public RDP interface was brute forced slowly over a 2.5 year period!
There’s a nice explanation of the thought process that gave rise to the original XKCD piece here too.
Offline cracking: this is where you have the password hash. It’s been stolen in a breach, either by you or by someone who has shared the hashes for others to crack.
So no amount of protective monitoring by the web site owner is going to help now. You have the hashes locally, you get cracking using various tools with huge GPU power at your disposal. There are plenty of approaches, but here’s one that works for me:
- First a dictionary or common wordlist attack, ideally customised to the expected language and keyboard codepage of most of the site users
- Limited success? Try wordlists from other breaches
- Next, a concatenated version of the dictionary attack, adding multiple dictionary words to each other, to pick up the ‘correcthorsebatterystaple’ type of password. There are fewer combinations of concatenated words than are possible with mangling, hence start here first
- Then, the dictionary attack but with some mangling, adding uppercase, lowercase, numbers and non-alpha characters
- Some would argue that mangling comes before concatenation, but for me it depends on the password complexity requirements of the web app that the hashes have come from. If complexity is enforced, go with mangling, as concatenation is unlikely to be used.
- Finally, a brute force attack, potentially taking advantage of predictable language patterns; ‘o’ is often followed by ‘u’ for example
That’s why I don’t like pure concatenation of words to create passwords.
Should you change your password after a breach?
So, what about all this advice to change passwords after a big breach. At first it seems pretty obvious – your password is compromised, so change it.
Except: it’s rare for the plain text password to be stolen. Unless the web site developers were really nuts, the password will have been one-way hashed and (hopefully) salted.
Hashes of strong passwords are very difficult to crack. Even with the most powerful GPU cracking tools and hardware available, a complex, long password will take a very long time to break.
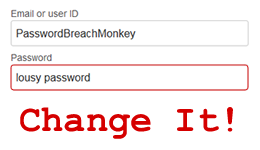
So should the advice from eBay have been ‘change your password if it was weak’
Arguably, if you had a strong password for which the hash was exposed in a breach, should you be bothering to change it? Controversial, I know – I very much welcome feedback on this point.
Or is there more to the eBay breach? Did they leak plain text passwords, which is why they’ve advised everyone to change them?
Three times in as many weeks the advice from mainstream media has been to change your password in response to (yet another) breach. It can’t continue like this, so set a strong password and stick with it for a bit.
$corre$cthor$sebat$terys$taple$ plus some numbers appended and prepended would make for a pretty good password. Concatenation, mangling and non-alpha characters.
Or maybe, to quote Jay Abbott @JabawokJayUK:
“correcthorsebatterystapleboltedduetopendinggluefactoryvisit”













