There’s a Cross-Site Request Forgery issue (CSRF) in D-link 932L IP web cams, which means an attacker could potentially get a victim to start emailing or FTPing all their images to a server of the attacker’s choosing.
The problem arises because there is no CSRF token in the web interface, and hence an attacker can create a web page which mimics the POST request that the web interface uses to set/change the email server that images are delivered to.
In Firefox it’s very tempting for the user to ask the browser to remember the basic authentication details, and hence these are sent automatically by the browser when the fake request is being sent.
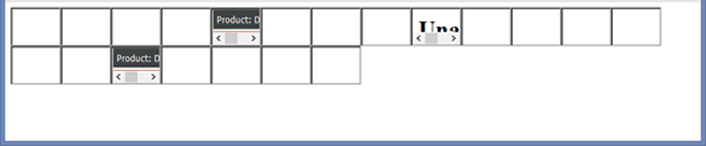
This exploit gets the local IP of the Firefox web browser and tries to CSRF adjacent addresses, to make the cameras send email to an arbitrary server.
I’ve provided the code to do this below; some of it is borrowed from random people on the Internet, so thanks very much for that to “mido” on stack overflow. (See http://stackoverflow.com/questions/391979/how-to-get-clients-ip-address-using-javascript-only ) This isn’t anything like production quality and was only hacked together to prove the point.
See also part 1 and part 2 of this series.
dlink.html:
https://github.com/pentestpartners/bits-for-blog/blob/master/dlink.html
And here’s the file that is invoked as and IFRAME, and sets the SMTP server.
Iframe-dlink.html:
https://github.com/pentestpartners/bits-for-blog/blob/master/iframe-dlink.html
If we now visit the first page in Firefox, that’s 192.168.1.124 and .135 getting zapped – as we’ve asked Firefox to remember the basic authentication credentials.
It’s looked up the set of IP addresses, and chosen 192.168.1.0/24 as a likely home address range, and then – for time reasons – has sprayed the CSRF over 192.168.1.120-140 only. We could easily do the whole /24, but it would take significantly longer.
If you want to be stealthy, you could make the IFRAMEs transparent or similar.
And now here’s the mail flowing in to the mail server we specified in the CSRF file:
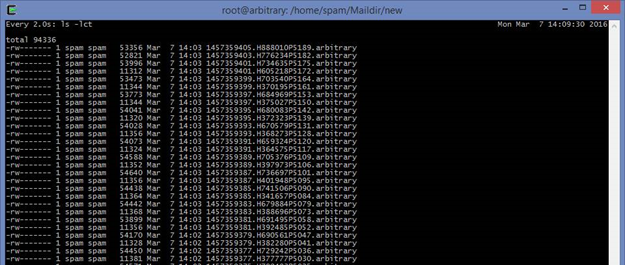
So we get incoming email every two seconds that looks like this:
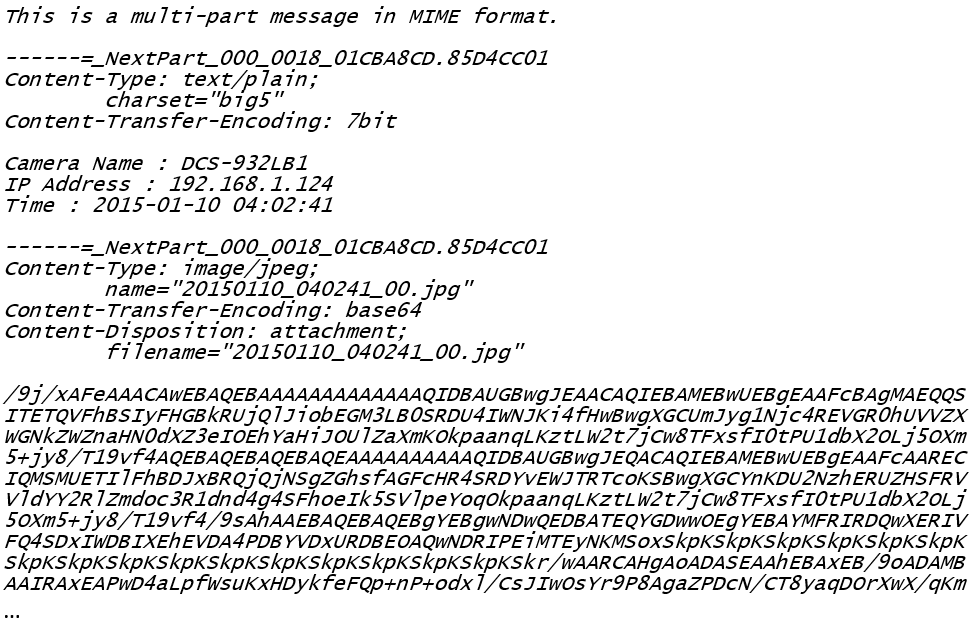
And if we open the attachment, we can see the image.

Action – there is now updated firmware out and you should upgrade
http://support.dlink.com/ProductInfo.aspx?m=DCS-932L
Thanks to the D-link security team for responding helpfully to the bug report, and getting new firmware issued to fix the problem.
UPDATE:
D-Link have also updated the DCS-5020L. This camera has more functionality but was also vulnerable to the same CSRF issue.














