News out of the University of Texas at Austin yesterday reveals a frighteningly easy lock screen bypass on the latest version of Android (Lollipop). This version of Android is currently installed on about 20% of devices globally according to Google’s latest figures, so although this bug isn’t a massive showstopper for the current install base, it’s still pretty bad.
The bypass is specific to devices that use a password as a lock mechanism, so if you have a PIN or pattern to unlock your phone you should be unaffected. Of course, people who use passwords or passphrases to lock their phone are usually doing so because they have something on there they really want to protect.
We have been able to confirm this vulnerability ourselves on version 5.1.1, and we managed to bypass the lock screen, even with our fat fingers.
The steps to bypass the lock screen are as follows:
- Open the emergency dialler
- Type some characters into the dialler, about 10 should do it
- Double tap the characters to ‘select’ them, and select ‘copy’
- Tap once in the dialler and select ‘paste’
- Rinse and repeat steps 3 and 4 until you can’t double tap select it anymore, which will double the size of the sting each time
- Go back to the lock screen, then swipe left to open the camera
- Swipe the notification drawer down from the top of the screen, then tap settings
- Long tap into the password prompt that appears, and select ‘paste’. Repeat this until as many times as you can
This will eventually cause the User Interface to crash and the buttons at the bottom of the screen will disappear. This will also open the camera app as full screen. Wait for the camera to crash, and you will be sent to the home screen. You’re now operating the phone as if you had entered the password.
Essentially the excessive characters are causing the KeyGuard service to crash, whilst the rest of the services are still running.
Waiting for camera to crash:
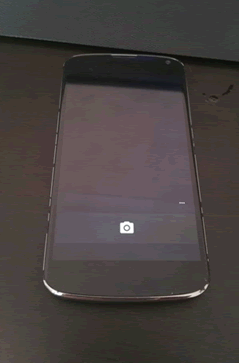
Camera crashes, phone enters standby, press power button, login bypassed:
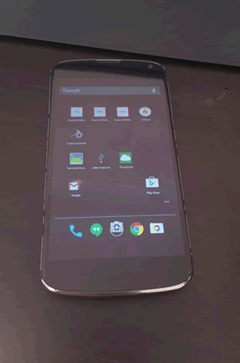
As this vulnerability affects only the latest version of Android, chances are good that the majority of phones that are vulnerable are the Google Nexus range, so they should be patched by Google fairly promptly. You can check the version of Android you are running by selecting the ‘About Phone’ option from the settings menu.
If you are affected by this vulnerability then you should ensure that you make sure that you keep control of your device, as this bypass is quick and easy to exploit should someone get hold of your phone.
Our findings
It’s important to mention that this only works on 5.1.1 of “pure” Android – other vendors’ versions of Android may rework KeyGuard so that this technique may or may not work on it.
We’ve proven definitively that it does not work on a Samsung S5 running Android 5.1.1.
Similarly other versions of Lollipop may have more or less success. For example we can’t get it to work on 5.0.1 on a Nexus 4.














