The FBI has just released it’s annual Internet Crime Report for 2019, it makes for some really interesting (and depressing) reading. The mainstream media focused on the headline figure of $3.5Bn in losses in 2019, but what caught my eye is the Business Email Compromise (BEC) or CEO Fraud stats.
I usually include these in my security awareness training and noticed that this year they have gone up yet again. In 2017 they amounted to $675m, they doubled in 2018 to £1.2Bn, then last year they increased again to £1.7Bn. This is a staggering figure, but what is interesting is this $500m increase is from an increase of just 3700 reports. That’s an average of $136,000 per report!
Changing face of BEC
Statistics are one thing, but the target of the fraud is also changing. The majority of these instances were where companies were targeted through a finance team requesting money be sent out. However, this year saw an increase in attacks against HR and Payroll to divert employee salaries. Simply, the attacker contacts your HR team and pretend to be the employee and state they have changed banks and want their salary paid in to a different account. HR make the change and come payday the salary is paid to the fraudster.
On the face of it this attack is not going to net much revenue when targeting James in customer services, but when you consider the net monthly salary of corporate C level staff, this can net a significant sum.
Commonly we are seeing attackers use multiple tools to convince staff the request is genuine. Although it’s called Business Email Compromise, these days with large organisations the victim receiving the email won’t know the voice of the supposed sender and so attackers will phone your staff and state “I just sent you an email, can you process it…”. This will add more weight to the attack and make it much more likely to succeed.
Invoice Fraud
Invoice fraud is something commonly bundled in to the BEC bucket, though it tends to hurt individuals much more than large businesses, though not all. In a recent case, a customer who had some plumbing work completed, sent a significant sum of money to the wrong bank account. This was in relation to an invoice they had received for the completed project.
After investigating, it transpires the plumber’s email service had been compromised, the attackers searched the sent items and found the plumber had recently sent an email with the correct invoice details on it for work completed and then changed the bank details and resent the invoice to the customer. They then set up email rules to prevent emails back from the customer from being seen by the plumber. The customer paid the invoice and both parties were out of pocket.
This plumber had a relatively weak password on their email and didn’t use two factor authentication…
This technique is commonly used in larger attacks, if an attacker can gain internal access to corporate email they can send internal emails to staff which will appear much more genuine and are highly likely to be actioned.
So how do you protect against BEC
There are many ways to prevent this attack, but in my view top of the pile is education. This attack looks to exploit peoples willingness to help without validating, so training staff to validate before helping is fundamental. Staff need to know what the attacks look like and how to handle them should they receive any.
Often this training will only focus on the finance teams, but as we have seen, your HR and payroll teams are just a vulnerable. So include them. Remember your HR teams are naturally going to receive a lot more external email and so ensuring they are equipped to spot this type of attack is crucial.
In addition, the attackers want staff to bypass existing processes. So there are two things to do here. Firstly, make sure you have processes that require validation prior to sending money externally, and secondly, empower staff to say no, not without validation, even if it looks like it is the boss asking. This is true of suppliers who want to change bank accounts. Your process should be to validate the change with existing contacts.
You can include multiple layers of authorisation when spending money, this will make the attack harder to perform as attackers will need to convince multiple people.
When handling phone calls, teach your staff to remain firm, but courteous, stick to the process and treat calls that look to solicit information or support an unexpected email as suspicious until fully verified.
Enforce strong passwords on your systems by getting your staff password managers, then enforce two factor authentication (2FA). Whilst 2FA won’t help staff who are unwittingly committing the fraud, it will make it much harder for attackers to compromise internal email systems.
Email SPAM technology is not really going to help here. These emails tend to look realistic and appear as genuine emails – your spam control is unlikely to detect them. That said, commonly attackers will use a domain that looks similar to your own domain. A simple technical control is to turn on any domain similarity controls you may have in your spam filters. These will detect if the email domain being used is similar to your own, if it is the email should get redirected to quarantine. Though this would need testing first to ensure it doesn’t trap genuine emails.
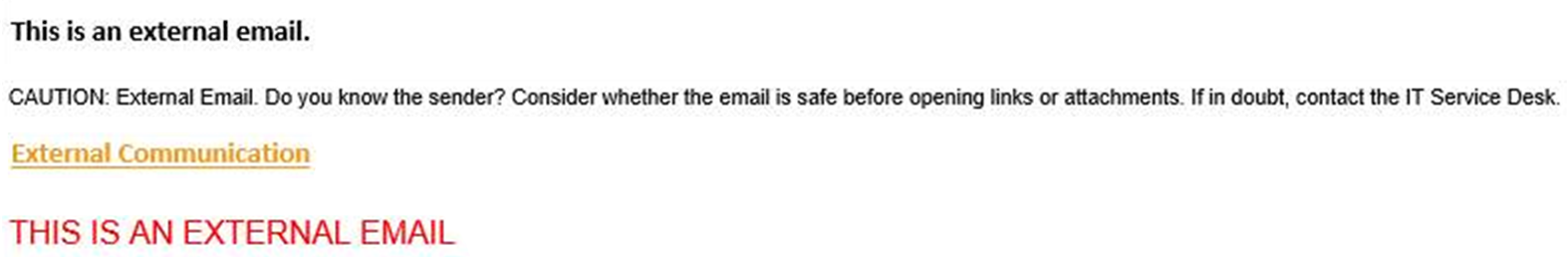
Another really simple control is to alert your staff if the email has come from an external location. This is an easy rule to turn on at your gateway which puts an alert message at the start of the email body. For example:
Sophisticated?
We constantly hear when companies have been breached that “the attack was sophisticated”, or it was an APT, but BEC really isn’t. A lot of attacks use nothing more than a webmail service like Gmail and Hotmail and a bit of imagination tied in with some basic open source intelligence. This is not a sophisticated attack, but neither is the defending against it. Some basic steps are all that’s needed to prevent it.
If you’d like to improve your staff’s awareness of good security controls I’d be happy to come help. You can get hold of me on Twitter @_tonygee_.