TL;DR
- What Capability Development (Cap Dev) is in this context
- The big Cap Dev benefits for red teaming
- Operations and Development, sharing and improving
- Improvements to TTPs, hardware, and developing strategies
- Benefits of using a DevSecOps model for offensive security
The essence of Cap Dev
Cap Dev in this context is all about continual red team improvement and innovation. It covers the development of new tools, as well as tactics, techniques, and procedures (TTPs) to enhance offensive capabilities. A bit like Q in James Bond, always developing new gadgets and technologies.
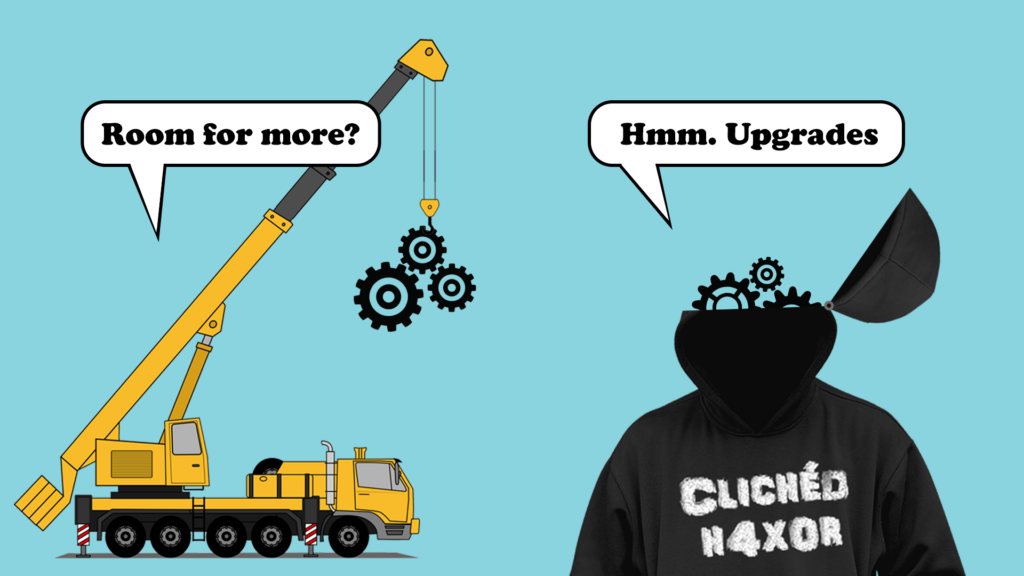
Operations and Development. Apart but together
A proficient red team is often split in two, Operations AND Development where each has a distinct and collaborative mandate. The Operations function is the vanguard, engaging in simulated campaigns against organisations, and the Development function is all about innovation, creating new tools and TTPs to improve processes and keep the red team’s arsenal cutting-edge.
This structure mirrors a typical DevSecOps cycle where development, security, and operations are merged in a continuous improvement feedback loop.
How this works
A systematic approach is needed to incorporate this dual-track model in a red team:
- Assessment and planning: Evaluate the current capabilities, identify gaps, and delineate the roles in the Operations and Development functions.
- Continuous training and research: Foster a learning culture that encourages team members to stay updated with the latest in offensive security.
- Cross-pollination: Allow members to oscillate between operations and development roles to gain a well-rounded perspective and spur innovation.
- Regular retrospectives: Conduct reviews after campaigns to glean insights and inform new capability development.
Cap Dev vs App Dev
Understanding the differences between Application Development (App Dev) and Cap Dev is important. App Dev is centred on creating software applications. Cap Dev is broader, covering the development of new TTPs, including hardware and developing offensive security strategies.
Drawing parallels with the military is helpful here. The evolution of the F35 fighter jet is like Cap Dev. Once the weapons platform is built there are always further developments in weaponry and situational awareness technologies, to continually improve performance during its lifetime.
A dedicated dual-track Cap Dev function continually gives a red team the tools to deal with changing security landscapes. Moreover, the cross-functional stints can enrich capability developers with operational insights, driving the creation of capable tools.
Real world examples: Defeating EDRs
One of the standout triumphs of our continuous Cap Dev is overcoming Endpoint Detection and Response (EDR) systems. EDRs are adept at identifying and thwarting malicious patterns but our Cap Dev equips us to create TTPs to navigate the most sophisticated systems.
Cap Dev enables us to create new and better malicious payloads. Informed by the latest EDR technology we can craft payloads to evade detection and fulfil their adversarial objectives. By using operational feedback and emerging defensive technologies we can work to stay a step ahead.
This iterative advancement mirrors the strategies employed by adversaries across the spectrum of sophistication. Novice attackers might rely on widely available exploit kits and hacking tools, while more adept adversaries may customise these tools or develop their own to bypass common EDR configurations.
On the far end of the spectrum, highly sophisticated threat actors invest heavily in research and development to create advanced malware and exploitation techniques that can circumvent even the most cutting-edge EDR solutions. Through our Cap Dev initiative, we emulate this spectrum of adversarial sophistication, continually honing our red team’s ability to test our defences against an evolving array of threats.
The intertwining of operations and development under the Cap Dev banner not only underscores our commitment to mimicking realistic threat scenarios but also illuminates the path towards elevating the security posture in the face of modern cyber threats.
By relentlessly pursuing a deeper understanding and mastery over the mechanics of EDR evasion as well as other defensive tooling, we instil a proactive and anticipatory ethos in our red team operations, fundamentally augmenting our readiness and response mechanisms against real-world cyber adversaries.
Security and control of capabilities
As we forge new offensive capabilities, it’s paramount to establish stringent controls to prevent misuse. Additionally, our practice of releasing certain tools to the public domain post a defined period, along with collaborating with existing external open source tool development encapsulates our commitment to bolstering collective security acumen and resilience.
Conclusion
The mantra of continuous Cap Dev is indispensable for red teams. As we navigate through an era of relentless cyber threats, fostering a culture of incessant innovation and learning is guiding us towards robust cybersecurity paradigms.