TL;DR
Yes, apply the update from Microsoft.
The new MS08-067?
CVE-2020-1472 is an elevation of privilege vulnerability in a cryptographic authentication scheme used by the Netlogon service and was discovered (and named Zerologon) by Tom Tervoort at Secura. It does not require authentication. It can be used by an attacker to remotely compromise a domain controller, the result being domain admin access. That pretty much as bad as it gets, naturally it is rated critical by Microsoft.
The vulnerability was patched in August 2020 in the first of a 2 part update, the first mitigates, the second (coming in 2021) fully closes it.
What’s affected?
All flavours of Microsoft Windows Server, including server core. Though the impact is predominantly going to affect your domain controllers.
Some versions of Linux are also vulnerable, SUSE, Red Hat
Is it a risk for me?
Commonly when Microsoft release a critical update the Infosec community make a big deal out of the vulnerability, rightly so in some cases, but in others often there is not actual public exploit code available. Now that doesn’t mean there isn’t code available in private groups and that those risks shouldn’t be taken seriously, but the absence of exploit code does make the bar of exploit that little bit higher. Unlike some cases, in Zerologon’s case there are currently 31 repositories on Github which purport to reference the vulnerability:
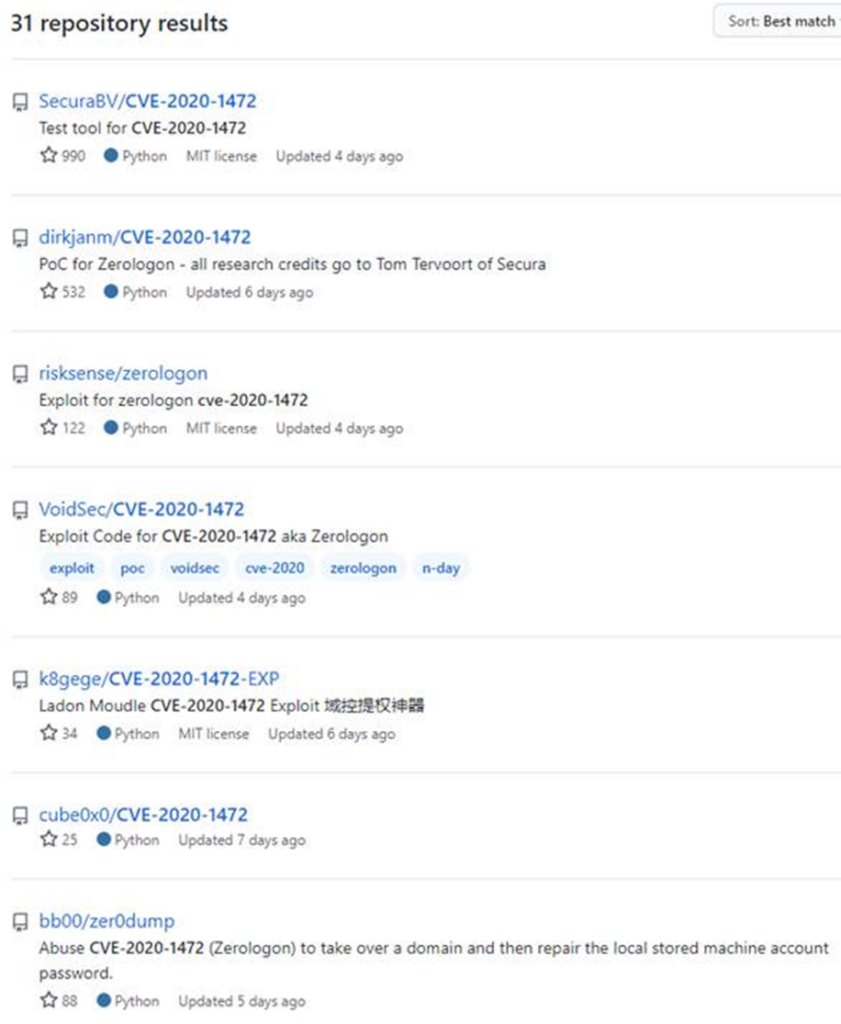
These range from a basic detection type script through to full takeover of a domain. Whilst we cannot confirm the authenticity of all of these, some are known to function as expected, they should be taken seriously.
As exploits develop they are getting more advanced, the early attacks would render the domain controller the exploit was run on unusable, this is now getting refined to allow the attacker to recover the domain controller. The code is even being added to the popular Mimikatz exploitation tool.
There is a risk that disgruntled internal staff will exploit this, right now there are no known PowerShell versions of this exploit and so short of an internal staff member using their own laptop it’s unlikely that they will have the toolset to exploit it…however, this will change.
The threat is real. This is becoming a ‘point and click’ type exploit.
What mitigating factors are there?
In order to exploit the vulnerability the attacker does need to be on the local area network, however, does not need credentials. This does mean an attacker needs to be inside your network boundary, but this could be achieved in many ways, most obviously through a phishing attach, but that may not be necessary… Have you got wired network points in public meeting rooms? How secure is your wireless?
A read only domain controller is also likely affected, but it is unclear in what way. Read only domain controllers may increase the risk to your organisation as commonly these are placed outside the trust boundaries.
The exploit currently breaks the domain controller it is exploited on and so it is unlikely that responsible security consultants will execute the exploit, however, unknown threat actors are likely to. This is also likely to be improved as time goes on.
Then…well… there is the patch obviously.
Once you have applied the patch you can enable some registry keys that will enable DC enforcement, this will deny vulnerable Netlogon connections unless the account is allowed. Note, this will become the default in early 2021 as Microsoft will release a second update to implement this.
Detecting the exploit
There are a handful of rules you can add to your security monitoring server (thank you Corelight for these links).
Event ID 4742 is worth monitoring, that will show changes to a computer account which is what Zerologon is doing. Though sadly this will likely only show you have already been compromised
There are a number of other detection options in this blog from Lares. Though sadly, like the above, this will likely only show you have already been compromised
Conclusion
So in short, yes you should worry, this will be exploited for many years to come, we are still seeing MS08-067 in use, the exploits will get more reliable. The risk is very much real and the impact is as severe as it gets for an enterprise domain.
This is currently a changing threat, more and more researchers are looking at this and finding novel ways to exploit it.
Get patching!