From what I’ve seen and read the Pwn Pad looks like a nice bit of kit, but as it costs $1,095 / £654 I thought I’d have a go at making my own, or something very similar, for a lot less.
This project was undertaken as we had nice little test lined up which required a covert device to perform some wireless work. Yes, I could have bought one, but where’s the fun in that?!
For those who don’t know, the device is a pen testing platform that’ll fit into a (big) pocket. It uses the Google Nexus 7 tablet and is primarily for wireless but will happily handle other tasks.
It uses a mixture of a custom kernel and the Kali Linux distribution, aka the pentesters’ Swiss army knife, in order to get the wireless side of things working. The important thing is that this combination allows the use of monitor mode, meaning that I can monitor the wireless activity through a usb wireless card. The test required us to snarf wireless probe requests from other mobile devices so this made the platform pretty much ideal.
While the build was fun it wasn’t without snags, this was a scratch build so it meant gathering ideas and components and testing them – 4 days’ worth of trial and error in all. It required rooting the device, seeking out the right kernel and Pwn Pad version of Kali (so drivers for the external wireless card were supported), and discovering that not all components are created equal.
The big takeaway is that you’re going to need some time, a supported usb wireless card and a keyboard for your Nexus 7 or this little project will be zero fun.
Here’s what you need:
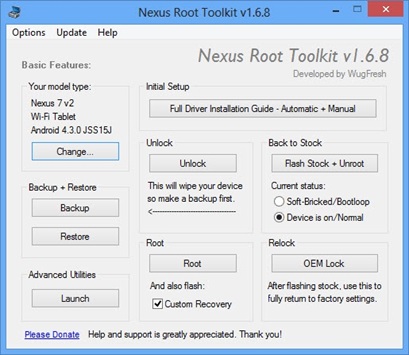
Nexus 7 with Nexus root toolkit:
http://www.wugfresh.com/nrt/
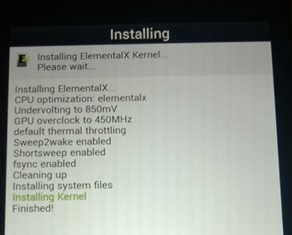
Custom Kernel with RTL8187 drivers built in:
http://w11.zetaboards.com/Pwnie_Express/topic/9102405/7/
Kali, Pwn Pad version:
http://w11.zetaboards.com/Pwnie_Express/topic/9369003/1/
Alfa USB wireless network adapter (awus036h):
http://www.amazon.com/Alfa-AWUS036H-802-11b-Wireless-network/dp/B002WCEWU8
OTG cable (on the go):
http://www.amazon.com/CNE16187-Micro-USB-OTG-Adapter/dp/B005QX7KYU
…and here’s how to do it:
1. Root your Nexus 7
Doing this gives you ‘su’ root access. Then install TWRP (team win recovery), this allows flashing of Kali zip via recovery.
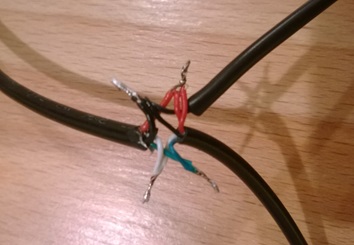
2. USB Wireless
I read that the Nexus originally couldn’t power the wifi card over usb so I needed to power it with a usb ‘y’ cable. this meant splicing in a separate power line into the usb. This was simply done, black and red cables are for power, the green and white are data.
I later noticed this was not the case and the quality (thickness) of the USB cable had a part to play, a thicker rubberised USB cable didn’t require power splicing in and the wifi card worked flawlessly.
3. Monitor Mode Fun
Once all the testing and installation was complete we had a working ‘pocket hackbox’. Monitor mode was working on the external USB wifi card and we had the Aircrack-ng suite of tools at our disposal.
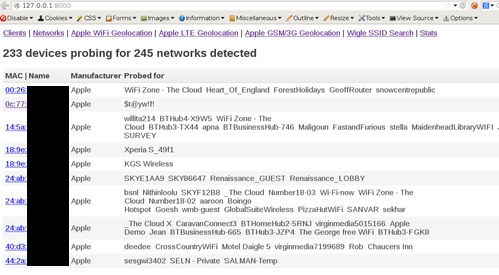
4. Client Probes & iSniff-GPS
An excellent project named iSniff-GPS by Hubert Seiwert is available on GitHub, https://github.com/hubert3/iSniff-GPS, this is basically a toolset for collecting wireless device probe requests and visualising the location data exposed by this data.
A good write up of the project can be found here: http://9to5mac.com/2013/01/01/isniff-gps-tool-reveals-locations-of-ios-users-prompts-privacy-concerns-for-apples-location-services/
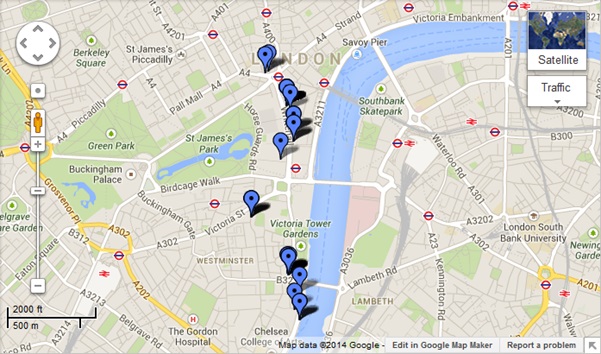
An example of this software and the data collection is shown below:
A lookup can then be made on each of the SSIDs probed for against the Wigle.net database and if previously mapped then the location of the previously visited Wifi access points disclosed.
Next steps…
I’m currently building some modules to plug into this so that GPS location is logged at the time of first seeing the device, hence we can roughly plot probing devices on the map, then mapping each of the probe requests with a Wigle ‘hit’ on a secondary map, this will allow us to view devices at a location and then view the access points that they have associated to… can you say ‘privacy’?
The following image is a work in progress and a starting point using Google Maps and kml to map this data passively collected:
I was looking for a project to do with the Raspberry PI, this could well be it; The Raspberry Spi!
Be warned
I found that micro USB port on the Nexus is flaky, its not the best connected part of the device. Be careful with it or the internal soldering will give and you’ll need a new device. The same goes for those OTG cables, so best to buy a few.