Like most people, pilots want to expedite things and generally make their work easier. A common conception about aviation is that it’s a leading industry with technology at its forefront. While this is generally true some of the systems in use today are rather dated (to put it mildly). A great example is the method that pilots use in poor visibility to “find” the runway; their Instrument Landing System (ILS), a technology invented in 1929.
ILS history
The ILS is used on aircraft to help pilots navigating to the runway on approach / landing in both a horizontal and the vertical sense. Whilst there have many improvements to ILS technology since its conception, the fact remains that the ILS was invented in the 1920s and became approved and adopted by ICAO in 1949. To this very day, it remains the most accurate method available to commercial pilots when it comes to navigating to the runway.
Other systems? Not so good
Whilst ILS systems have been updated and are still reliable and effective, the same cannot be said for everything when it comes to aviation. Take ‘Notices To Airmen’ (NOTAMs) for example. These are notices filed with aviation authorities to alert pilots of any hazards or changes along a flight route or at a location which could affect the safety of the flight – the number of notices for any given flight can often be several hundred if not thousands.
Reviewing every single NOTAM is important because any one could contain information which is may affect the safety of that particular flight. They are often not provided in an organised manner but instead in a disorganised list which is not sorted in priority.
The following video highlights the risks of missing a NOTAM. In the video, a Gulfstream V lands at Asuncion Airport, narrowly missing the roof of a construction truck on the runway by a few feet. The NOTAM highlighting that workmen may be on the runway wouldn’t necessarily be the first in the list, in fact it may be the very last NOTAM or alternatively hidden somewhere in the middle of the list.
Impacts of cost cutting
A commonly held view amongst pilots is that cost cutting measures in airlines have resulted in inadequate time given to pilots to brief prior to the flight, especially when they have in the region of 40 pages of NOTAMs to review. In 2017 an Air Canada A320 nearly landed on a taxiway (and narrowly missed 4 aircraft waiting for departure) at San Francisco airport.
A contributing factor to the incident was deemed to be the ineffective presentation of NOTAMs, in this case 27 pages of them for San Francisco airport alone. After the incident, the National Transportation Safety Board (NTSB) Chairman Robert Sumwalt said NOTAMs are often written in a language “only computer programmers would understand”.
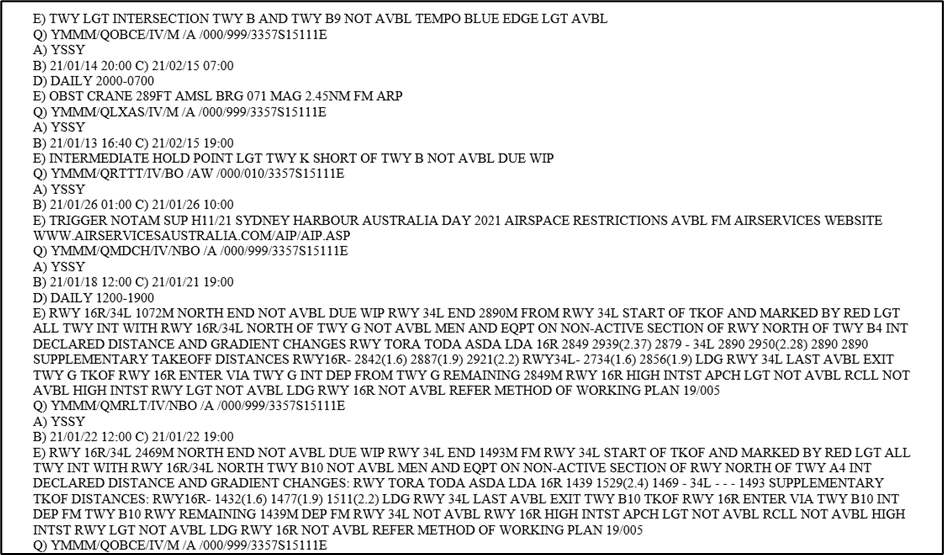
Sydney Airport NOTAMs – half of one page (there are 5 pages in total)
With the cost-cutting measures that many airlines have implemented, it is now not uncommon for some airlines to provide less than 10 minutes of “briefing” time for pilots at their reporting time – and in some airlines pilots are expected to self-brief in their own time prior to reporting for work.
How do pilots cope?
So how can pilots cope with often over 100 pages of briefing and flight planning material when they are often given less than 10 minutes (or no time) to do so? The answer: tools. Considering the number of briefing pages that pilots have to review prior to flight can range into the hundreds, having applications which enable pilots to review items more efficiently or display information it in a clearer format can help to reduce the time taken to review the items.
Tools can create weaknesses
Two considerations are:
- Can a hacker get their own applications onto a pilots EFB?
- Once they have their own applications on pilots EFBs, what could they do?
It wouldn’t take long for someone with little knowledge / experience in the aviation industry to quickly learn what sorts of tools and applications pilots are likely to install – there are forums full of pilots discussing 3rd party applications they have installed which make their day to day lives as pilots easier.
Anyone with a little software development knowledge could create their own “Useful Pilot Tool” application. However, device integrity and security software / features (e.g. MDM / sandboxing) would in most cases prevent malicious software from exposing data or allowing malicious software from performing illegal tasks. They cannot however account for all possibilities.
Remote access to EFBs
With the security layers present to prevent malware being uploaded, it is therefore likely going to be a difficult task for a hacker to upload something which would instantly cause EFBs to fail. But what remote methods could they use in attempts to gain access to data on an EFB?
- Create publicly available software available in the app store which is designed to function as described – with no malware, but with the ultimate aim of causing an outage of EFBs (or performing other illegal tasks e.g. data harvesting) once a large number of pilots have installed their “Useful Pilot Tool”. (Note “sharing permissions” in paragraph below)
- Take over a publicly available EFB application supply chain e.g. stealing someone’s Github credentials, or submit a malicious pull request
- Hack applications that are already established and installed on either some or many pilots EFBs (again, a useful pilot tool application would be a likely target)
- Sideload applications onto EFBs therefore bypassing the official application store policies by creating useful applications pilots are likely to want when flying (and therefore likely to install on their EFBs)
- Remote access trojans. These could be sent via Email to the pilot (it is common for pilots to have their personal email on portable EFBs) or a cleverly crafted SMS URL link (many EFBs have both Wi-Fi compatibility and a sim card installed for 3G / 4G)
- Jailbreak the EFB – difficult to do and would probably (hopefully!) be highlighted by MDM, but how much data / damage could be done prior to the EFB device being disconnected from networks?
The task of getting an application of their own onto an EFB is simple. There are a wide variety of tools available on app stores which would are useful to pilots including decoding of weather / runway state reports to tools which display information in a clearer format. We know pilots can be drawn to the use of tools so an application which requires sharing permissions with an EFB application could potentially have consequences. At that point you have an application installed on an EFB, AND you have sharing permissions with an EFB application.
You may wonder why a pilot would enable sharing permissions with a 3rd party application – quite simply because they are expecting to share it. The pilot’s expectation would be to provide the data to the “useful pilot tool” and for the tool to output the data in a different format. It could be as simple as copying and pasting of flight plan information, passenger lists, weight and balance / performance calculators, or weather information.
How to manage tool use
There is plenty of evidence online to suggest this is already happening though luckily none of the applications which do require sharing permissions have been developed by malicious threat actors (that we know of). It does however highlight that a combination of factors are leading some pilots to download tools which could compromise the integrity of an EFB. Four things come to mind which would help to resolve this:
- Configure MDM to prevent it from happening
- Improve security awareness training for EFB users on the potential vulnerabilities to EFBs
- Change of policy to prevent the installation of 3rd party apps on portable EFBs
- Fix the root cause… inadequate or insufficient (official) tools for the modern age, inadequate time prescribed for tasks, inadequate / inappropriate presentation of information to pilots
Security hygiene for EFBs
A final consideration regarding the “human factor” is the likelihood of pilots inadvertently opening links to malicious websites – something which should not be overlooked. Airlines often allow pilots to use EFBs as their own personal devices. Email access, messaging applications and cellular messaging are all common on portable EFBs (as well as internet browsing). As with any message / email, care should be taken prior to opening links.
The purpose of many malicious URL links is to download malware onto the target device – in this instance, the device is an EFB. Pilots inadvertently opening malicious emails / messages remains a possibility and it raises the question of whether email / messaging applications should be available on EFBs. It also raises the question of whether better endpoint protection / sandboxing should be used when it comes to EFBs.
Help
To help airlines deploy EFBs securely we’ve written this no nonsense guide: Deploying EFBs securely