When data roaming was still expensive across Europe and cellular data service was patchy, I used Navtex extensively whilst sailing in the Mediterranean.
Every four hours, one could get a useful marine weather forecast. Was there a fun days sailing ahead, or was a dash for port and gin & tonic in a quayside taverna more appropriate?
It’s less well used now for inshore waters & recreational sailing – mobile data often allows gathering of much more information more frequently than Navtex.
However, it is still extremely useful for offshore operations and mobile blackspots as it has a range of 250-400nm.
Many ECDIS have serial inputs that can take a direct feed from the Navtex receiver. Ships crews generally trust Navtex – why would it lie?
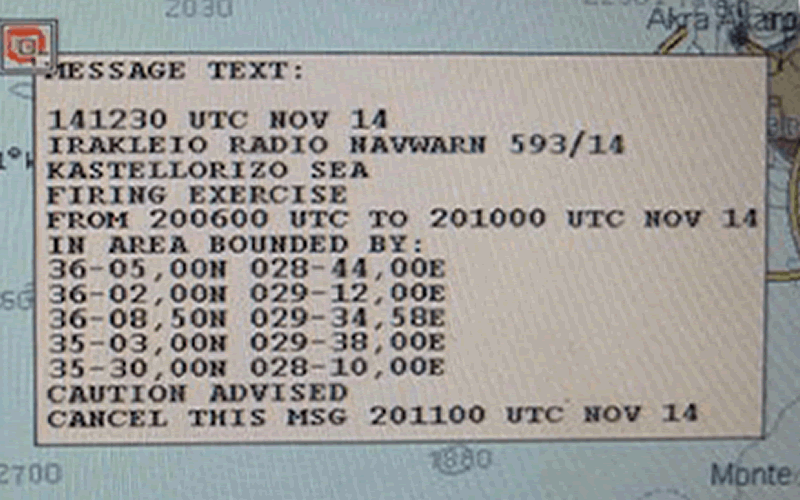
Here’s an example of a ‘missile firing exercise’ Navtex message automatically charted by an ECDIS. You wouldn’t want to miss that message!
Hacking Navtex
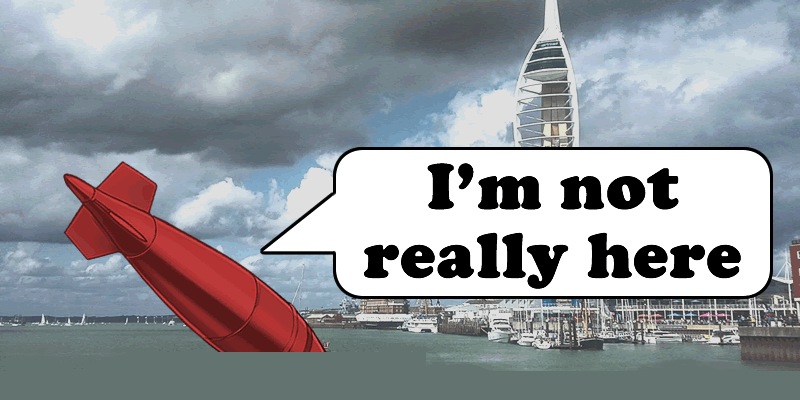
Portsmouth Harbour was closed following discovery of an unexploded wartime bomb. What would it take to either create a rogue incident or, more insidiously, cancel a legitimate one?
Navtex messages comply with the NMEA 0183 standard. This is going to be easy:
Here’s an example, genuine message from the www.admiralty.co.uk service:
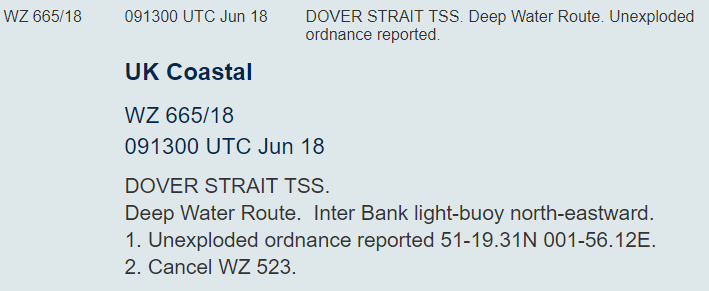
It’s been modified from the original data to be more human-readable. Source messages look like this:
- $CRNRX,007,001,00,TD02,1,135600,27,06,2001,241,3,A,==========================*09
- $CRNRX,007,002,00,,,,,,,,,,========^0D^0AISSUED ON SATURDAY 06 JANUARY 2001.*29
- $CRNRX,007,003,00,,,,,,,,,,^0D^0AINSHORE WATERS FORECAST TO 12 MILES^0D^0AOFF*0D
- $CRNRX,007,004,00,,,,,,,,,,SHORE FROM 1700 UTC TO 0500 UTC.^0D^0A^0D^0ANORT*70
- $CRNRX,007,005,00,,,,,,,,,,H FORELAND TO SELSEY BILL.^0D^0A12 HOURS FOREC*16
- $CRNRX,007,006,00,,,,,,,,,,AST:^0D^0A^0ASHOWERY WINDS, STRONGEST IN NORTH.^0D*15
- $CRNRX,007,007,00,,,,,,,,,,^0A^0A*79
The syntax is as follows:
$CRNRX <number of lines in message>,<message identifier (B1B2B3B4)>,<line number>, <frequency>, <day of month>,<month>,<year>,<time in UTC>,<error rate> then a 2 byte XOR checksum
Preceded by ZCZC and terminated with NNNN
The Message Identifier is made up of
- B1: transmitter identity
- B2: subject indicator
- B3&B4: serial number of the subject indicator
On the RF side, it’s based on SITOR-B, probably more familiar to radio hams as AMTOR-B.
So it really wouldn’t take much to send out rogue Navtex messages to cause confusion to shipping.
However, what I don’t like would be the potential to CANCEL a Navtex warning. Unexploded ordnance? What message?
There’s also the potential to send out a pirate alert. Pirates in Pompey anyone? The $CRALR alarm message can be used, setting a B2 code of ‘D’.
One BIG Problem
To transmit a signal that has the potential to have the same range as a genuine Navtex signal, the antenna would need to be something like 100ft tall at least and the RF engineering required to generate large amounts of RF power at a wavelengths of around 600m is far from easy.
However, if you were close to the vessel then an RF attack becomes more achievable…
One could use a shorter antenna of say 10 m, but you would need a LOT of power – tens of kW – to get a decent range.
Even a directional antenna would need to be pretty big.
I understand this is the transmitter for Navtex for the South of England. It’s at Niton on the Isle of Wight, identified in messages as ‘E’ or ‘I’:
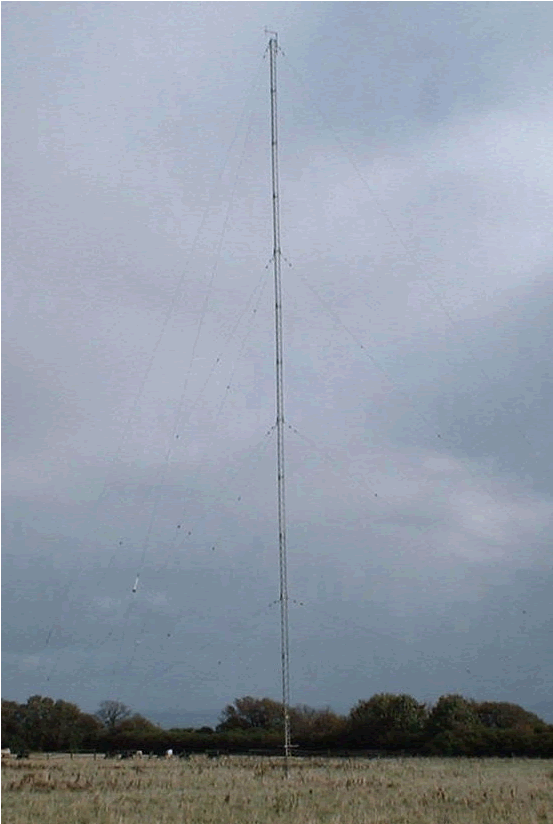
But that partly misses the point: those tampering with Navtex would probably only be interested in affecting a small coastal area such as a port. Broadcasting over a small area will take much less power and far smaller equipment; anyone with a little short wave radio expertise would be able to do this.
There’s little to stop one sending a rogue Navtex just after the legitimate message, giving a 4 hour window before it was updated. Would the crew be alert enough to spot it?
Recommendations
Navtex messages can be verified in numerous ways:
- Online Navtex services are available – it would be trivial to check on a mobile phone when in range of land, or via a vessel satcom terminal
- Check over VHF with the coastguard or other relevant authority
- Sat-C Navtex broadcasts are also available
However, that only deals with checking if a received message is valid. It doesn’t cover a valid message being ‘expired’ (e.g. the ![]() part of the message), though that will be harder to ‘hack’ for any significant period of time as the legitimate messages will generally have a higher strength signal and re-overwrite the rogue messages over time.
part of the message), though that will be harder to ‘hack’ for any significant period of time as the legitimate messages will generally have a higher strength signal and re-overwrite the rogue messages over time.
Auto-population of the chart on an ECDIS with Navtex data is relatively rare currently, but it’s likely to become more common, primarily to avoid manual data entry mistakes in plotting Navtex alert areas when inputting coordinates. Is that message on the ECDIS real or fake, or is an important message completely missing?