A large number of security researchers have taken exception to the ‘unhackable’ claims made by Bitfi and John McAfee about the security of their hardware cryptocurrency wallet.
The $100K bounty offered appears to be something of sham, given it covers a very, very specific scenario. Bitfi states that “our security is absolute”.
So, here’s the first vulnerability in the Bitfi
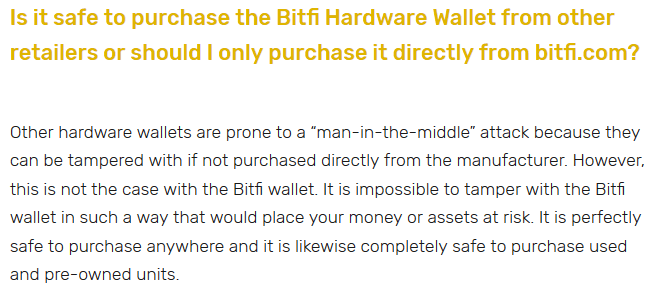
In the Bitfi FAQ, it is stated that retail supply chain vulnerabilities are not an issue:

It is impossible to tamper with the Bitfi wallet in such a way that would place your money or assets at risk

So, we bought some Bitfi wallets and started looking at the validity of the above claim, among many different test cases that we’re still investigating.
The Bitfi is a stripped down Mediatek MT6580. It’s an Android phone, minus some components!
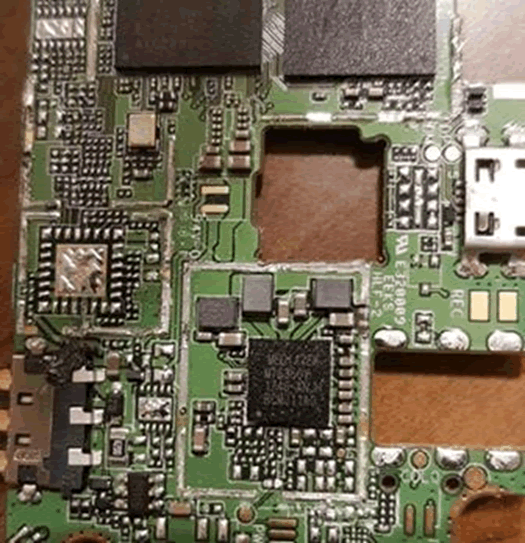
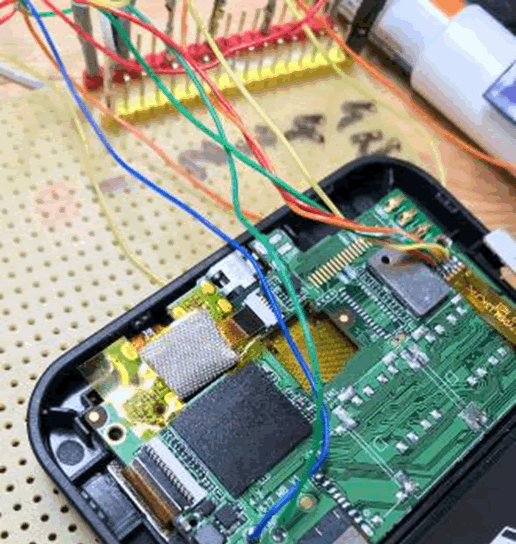
Here’s the inside of the case. Note the large battery size. We’ll come back to this.

Printed on a screen ribbon cable:
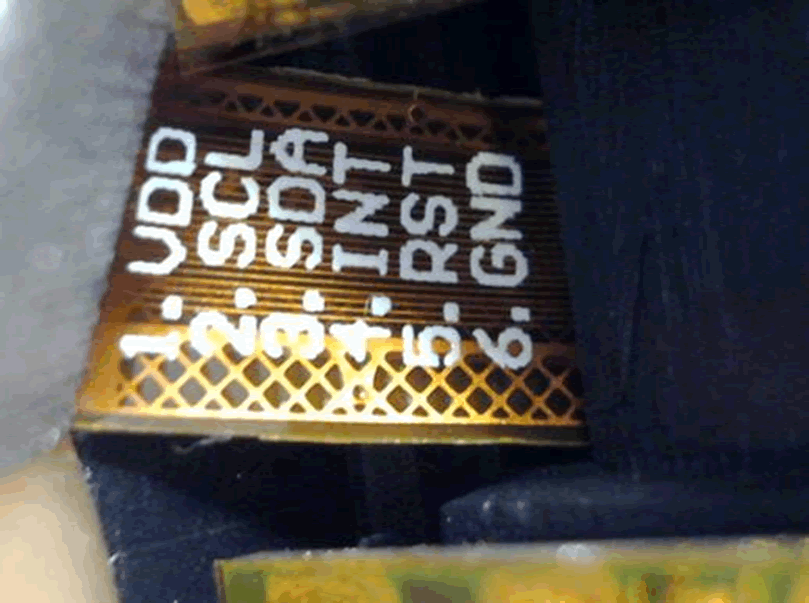
Oh dear. Inputs from the screen digitizer use the I2C protocol, easily intercepted. All you need is a logic analyser to capture the finger movements on the screen and therefore the wallet passphrase as it is entered on to the screen.
This could be mitigated by randomising the layout of the keys on the screen, but Bitfi haven’t done this.
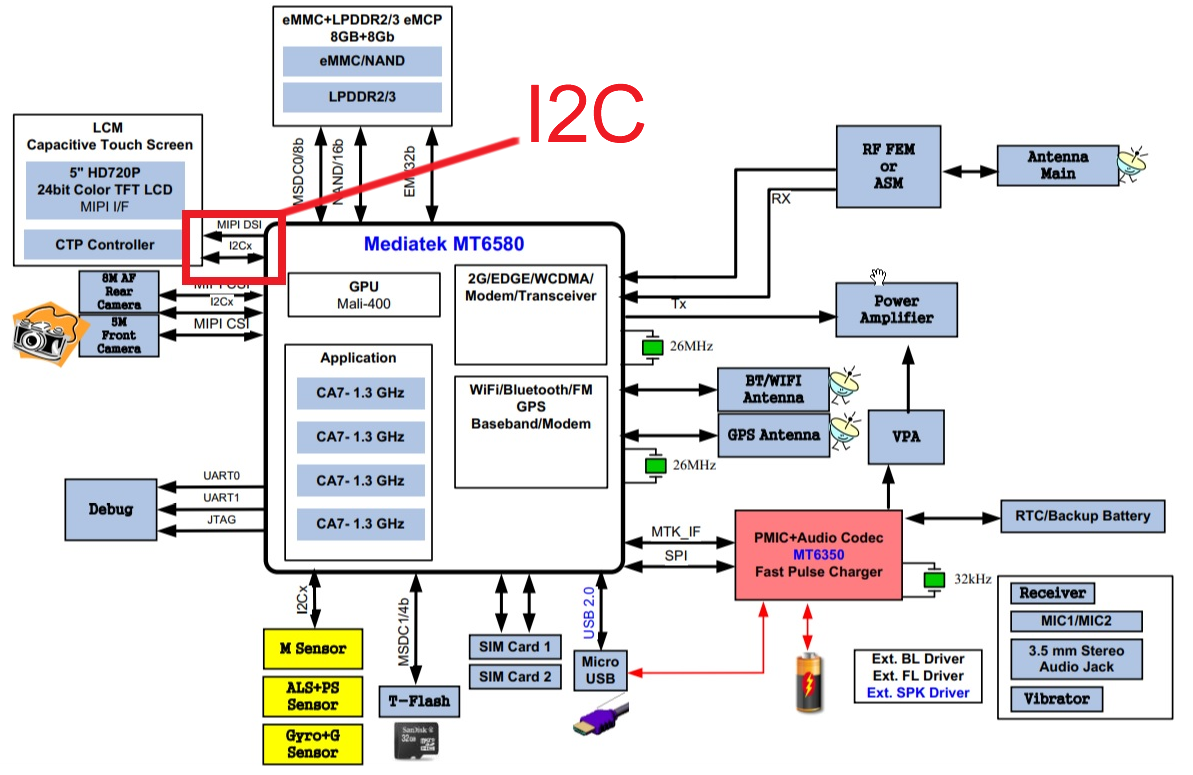
Comms from the screen use the I2C protocol, easily intercepted unless Bitfi have added some kind of encryption to the I2C, which we have never seen before. All you need is a logic analyser to capture the finger movements on the screen and therefore the wallet passphrase as it is entered on to the screen. There’s a great paper on the subject available here (link opens PDF).
The attack
There is no significant tamper protection on the device case. One of ours is in pieces and still works fine. A retailer or anyone else in the supply chain or previous owner of a device could easily replace the battery with a smaller version.
Using the space created and a little effort at miniaturising on to something like an STM32, additional hardware could be added that would capture the creds over I2C. A 3G or perhaps Bluetooth module could then be included to pass the stolen creds back to the attacker.
Battery life could be quite limited, but that’s not the point: Bitfi claim that their device can’t be hacked, so we’ve shown it could be hacked.
Anyone with physical access to the wallet could carry out a similar attack, though it would take a little time to do.
So yes Bitfi, it does matter where you buy the device from, and the integrity of the delivery chain is also important
Other attacks
Our main goal is to root the device. Once that’s done, it should be possible to recover the wallet keys from memory.
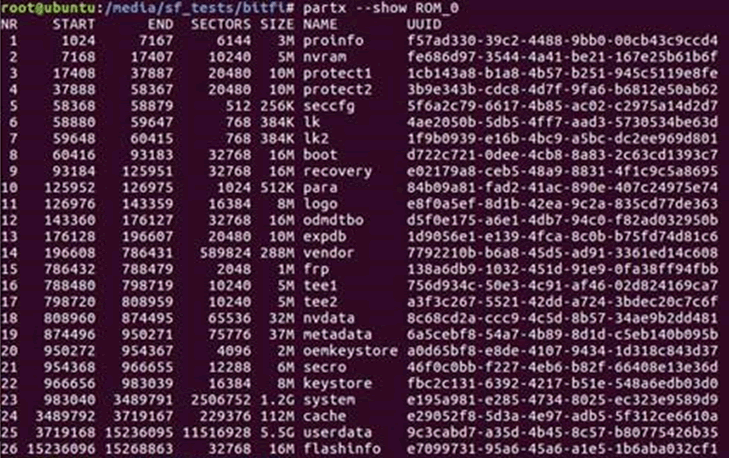
We’ve already got the file system from it:
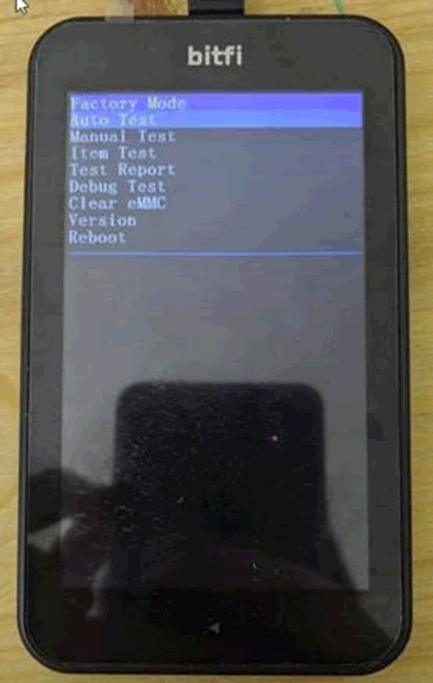
And got access to the factory test menu. It’s running abdb but we can’t connect or authorise access currently:
At the moment the main sticking point is figuring out how to get round the Mediatek file system encryption.
The attack surface is significant though. Lots more to come, we’re looking forward to the root dance!