You’ll probably know by now that I have a particular interest in the security of IoT coffee machines and tea kettles. Sometimes security is so poor that we have to laugh. Such simple security issues.
Now, when I’m feeling lazy and possibly a bit hung over, I really can’t be bothered to make coffee by hand. My preference is the stovetop Moka pot, but everyone has different preferences (and no stove in the office!).
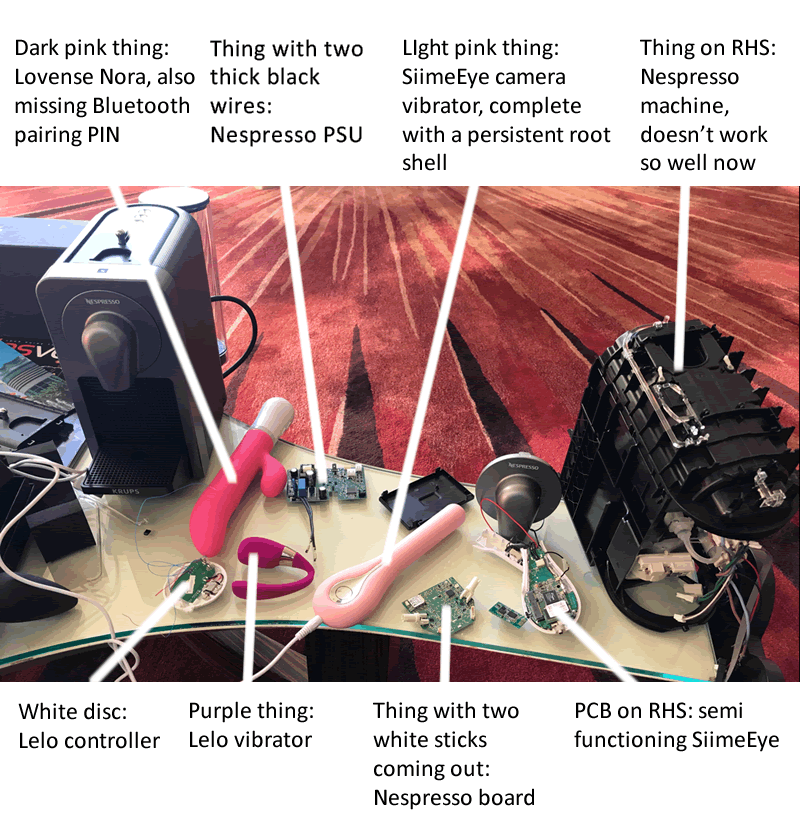
So, we have various coffee machines in the PTP office. Some still work, others have been reverse engineered with extreme prejudice.
Nespresso Prodigio

This was my first Nespresso Prodigio. We were reverse engineering it in Vegas at Defcon 25, and working on some other things at the same time:
It comes with a mobile app that communicates over Bluetooth. Connect to the coffee machine and one can have it make coffee remotely.
Brilliant!
Except for one minor problem: one has to GO TO THE COFFEE MACHINE FIRST to put a capsule in it.
I’m lazy and hung over. What chance I remembered to put a capsule in it last night, put a cup under the spout and fill the reservoir up with water?
Truly pointless IoT…
It doesn’t end there though. There is no connection security for Bluetooth. Just like My Friend Cayla, there is no Bluetooth PIN, no connection trigger, no nothing.
So long as a device isn’t currently connected to the coffee machine, ANY PHONE CAN CONNECT TO IT and have it make coffee. Any malicious hot drink hacker in Bluetooth range can trigger your coffee maker. One doesn’t even need to reverse engineer the app – just download your own copy from the AppStore or Play Store.
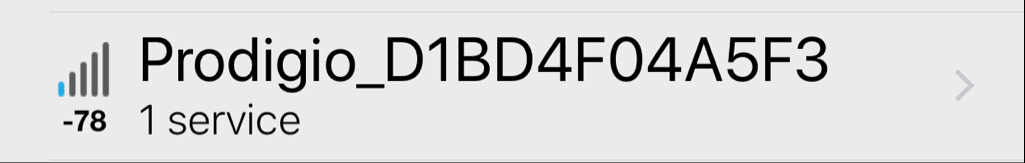
It’s trivial to find these open coffee machines, the BLE ID is ‘Prodigio_<MAC address>:
So if anyone was wise enough to pre-load it with a capsule the night before, they’re going to have cold coffee ready for them in the morning.
But, of course we reversed the app. A little…
Earlier versions of the Android app featured the ‘call_phone’ permission. Silent calls from the app. Nice!
We also noticed that a low capsule stock threshold could be set in the app. If your stock runs low, it could auto re-order more. A cool feature.
Only problem was that, if one could modify the minimum stock threshold (to its maximum of 65535 capsules) or make the app think that the machine had operated more times than reality, then you’re going to get a LOT of alerts to buy new capsules.
Jura E8
Capsules don’t really do it for me long-term. Bean-to-cup is the way forward for hung over pen testers. So we spanked a shed load of money on this:

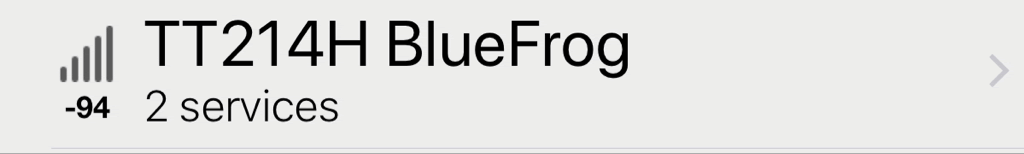
Chosen purely because it also has a Bluetooth interface. Guess what: no connection security.
So, look out for the following Bluetooth ID and you can make the machine guzzle beans and fill up the large drip tray:
More amusingly, if someone is making coffee at the machine, you can stop coffee making in progress over BLE. You can even mess up the coffee strength – making a strong brew come out weak and vice versa.
It is possible to set a PIN in the app to prevent others interfering with the coffee machine, but I can’t see anyone doing that…
Conclusion
All amusing issues. Hardly huge security flaws, but they do highlight the glaring lack of connection security for many Bluetooth enabled IoT devices.
A simple method to address this would be to have a key press to force the coffee makers in to connection mode. Only then can one connect an app and take control.














