Oh look, it’s yet another blog post about the Heartbleed vulnerability, yeah we know it’s bad and we should patch stuff as soon as possible. Well, not exactly, what I thought I’d demonstrate is a real world exploit of the vulnerability that I came across.
The bug itself is a simple example of memory leakage through an overflow: i.e. bits of memory in 64 kilobyte chunks may be extracted from the process’s memory. This could give us anything, including encryption keys, bits of traffic, credentials or session keys.
So, anyway, let’s have some wavy lines, as we move back to 19:30, after work had been done and the kids were in bed. I turned to my computer for some opportunities to shoot some zombies and de-stress.
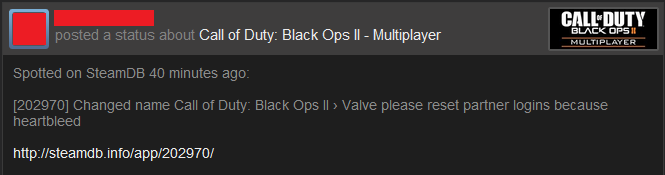
So, there I was casting an eye over Steam’s activity feed and I saw this from one of my Steam friends, (name and avatar redacted: you know the score):
Hmmm… This is interesting, let’s have a look at CoD: BOII multiplayer (these aren’t my images, as I don’t actually own the game):
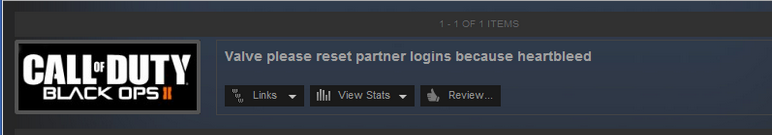
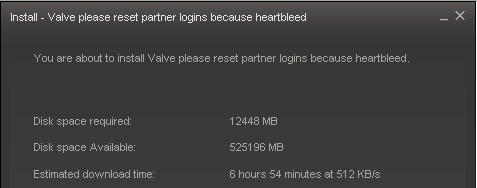
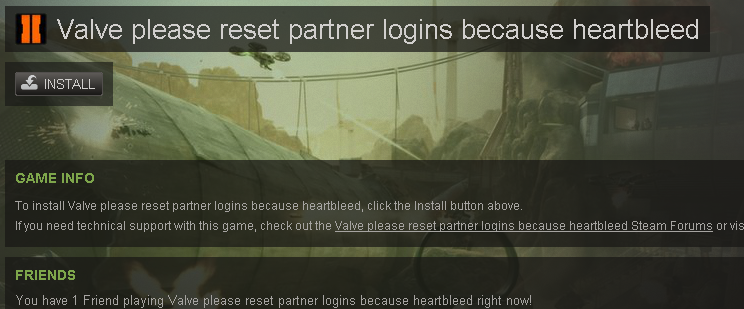
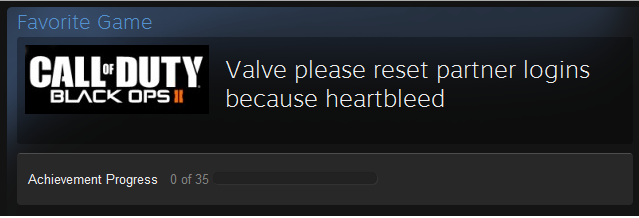
So what we can surmise is that the CoD developer had connect to the Steam developer portal and either their session ID or, even worse, credentials had been stolen.
Fortunately whoever did this just decided to make it obvious; but imagine the damage that could have been caused by a malicious user? This is a prime game played (by looking at Steam stats) by about 10,000 people a day.
We could mess around with achievements, or even push a dodgy patch to cause a compromise of the all the players of the game!
Editors note:
These were the findings that were reported by The Register on 10th April 2014.













