A few weeks back I spotted that two guitar amplifier manufacturers were introducing some smart features, controllable via Bluetooth and Wi-Fi.
First I found what has to be the most ridiculous ‘vulnerability’ in a Fender Mustang GT 100 amp: it acts as a Bluetooth audio device. There is no pairing security, so anyone at the gig you’re playing at can stream arbitrary audio to it and hijack your amp output.
Yes, seriously. It was so ridiculous that I made a video of one of my colleagues rick rolling me:
This is nuts. This is marketed as a gigging amp!
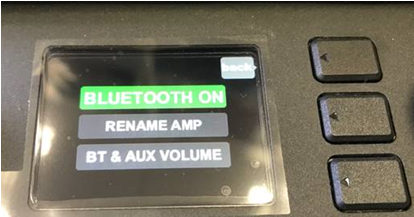
The Bluetooth ID is ‘Mustang GT’, though anyone using this amp to play live would be well advised to turn Bluetooth off as below. Of course, that then stops you using the smart features that are the key to this amp. More on those in a moment…
Now, after picking ourselves up after laughing at the stupidity of the rick roll feature, we moved on to more involved hacks
Ruining a gig
If you really want to ruin a guitarists gig, it’s possible to interfere with the sound presets that the amp offers. The mobile app interacts with the amp over BLE (separately to the Bluetooth audio feature) and allows you to download sound presets from other famous guitarists. A nice idea!
You can also create and name your own presets. It’s even possible to create a complete set list, with presets for each song on that list.
So, did Fender include any permissions based security for the sound preset feature?
Guess what: no authentication or permissions around pushing a new sound preset to the amp.
Here’s a video showing it:
Method 1: simply push a new sound preset to the amp over BLE. In the video I’ve pushed it to ‘Purple Fuzz’ to screw up the sound of the guitar, but I could do a lot worse.
Method 2: mute the app by turning the ‘tuning’ function on. No-one wants to listen to people tuning their guitar, so the amp auto-mutes. That’s your gig over!
A bit more silliness to finish off
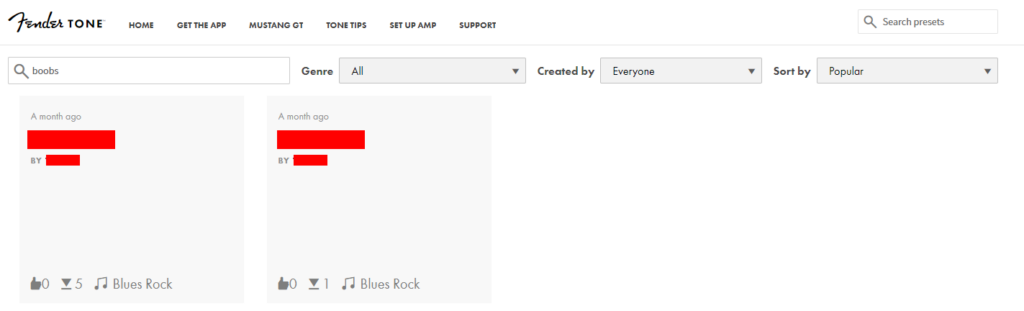
The mobile app allows you to name new sound presets and upload them to the Fender Tone website for anyone else to use.
The app filters out offensive names:
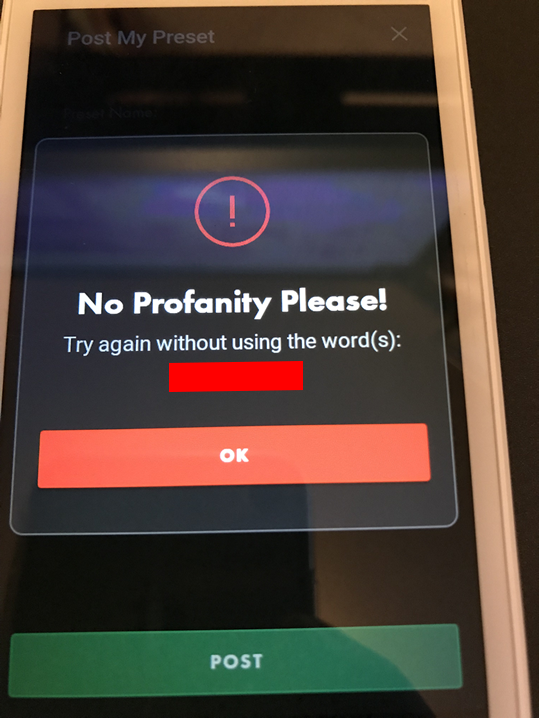
The list of filtered words was a bit pathetic, though we did laugh at it. I’ve never heard of a donkeyribber!
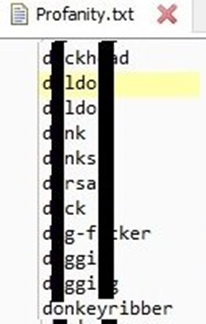
BUT all the swear-filtering is done client-side so it’s trivial to bypass, like this:
Marshall smart amp
I had a quick look over the Marshall’s Code 50 amp which has similar features. However, I found it to be pretty good security-wise by comparison. Whilst I could modify the sound presets, I had to pair with the amp first. After the paired device was disconnected, Bluetooth and BLE were automatically switched off. Much more secure.
Disclosure
We don’t consider any of the above to be security flaws. They’re features that could be abused, though they could really mess up someone’s set at a gig.
Advice
Guitarists: Turn Bluetooth off when you’re not using it.
Fender: come on – implement some simple pairing security. Even a button press on the amp to put it in pairing mode for a short period would be a step in the right direction.
And for you lovers of hacking and live music, please let us know if you see ‘Mustang GT’ on the list of available Bluetooth devices at the next gig you go to. No rick rolling though!
Further BLE reading
For more on BLE my colleague Dave’s how-to on manipulating BLE with Frida is really useful.














