So you think no one would ever sneak into your business? Think Again.
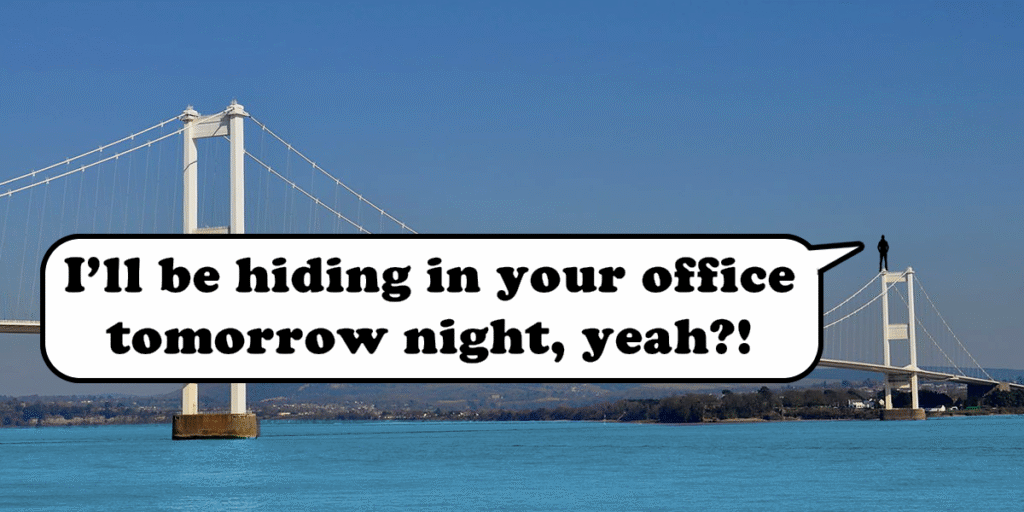
The man who climbed the Severn Bridge and broke into the Big Brother house seems to have method to his madness. Here’s why.
When I describe Social Engineering to some I get a common response: “Yeah, but who would ever do that in real life?” To them the idea of someone countering security to make their way into an office, worksite, sports venue or similar would be anathema to them. It violates the social norms they expect from polite and conforming society.
The idea that someone would not only do these things but then post them on social media might even shock the people who do this for a living. I wasn’t taken aback by the attempt but by the sheer disregard for anonymity that would normally accompany something like this. Posting “I have done something illegal, here it is!” seems mildly… stupid?
Not so stupid after all
It turns out that they’re not that foolish. They follow social engineering approaches and footprinting techniques. They appear to have good knowledge of the targets and they do their reconnaissance. They have noted blind spots and weaknesses in perimeter security and then exploited them.
They also have followers. And those followers even appear to supply them with insider knowledge and “wanted” posters.
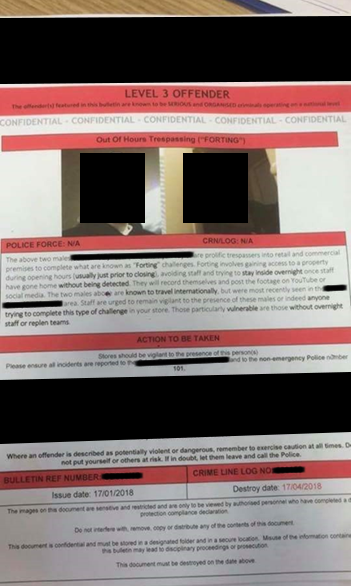
This picture posted on Facebook appears to be of confidential information, showing two suspected people- redacted.
Forting
Note the use of the word “Forting”. This is defined as gaining access to a property during opening hours (usually just prior to closing), avoiding staff and trying to stay inside overnight once staff have gone home without being detected.
These challenges appear to be set for the suspects by members of the public in what I’d described as Live Social Engineering.
Their method is similar to commercial social engineering approaches. Enter the building, remain undetected, do something the firm would not expect, mimic what real threat actors do without causing damage or raising alarms, record everything and then supply recommendations for improvement.
They go on to show videos of them (requires Facebook login) entering shops such as IKEA and comments suggesting collusion between staff and the attackers, these are some comments:
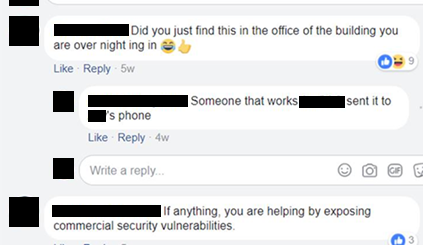
Source: https://www.facebook.com/AllyALaw/
Not helping
That last comment “If anything you are helping…” needs taking to task. This is categorically NOT HELPING. Social Engineering engagements are controlled and have clearly scoped permissions. What these people are doing is trespassing without prior consent. So, kudos for his approaches, but a huge facepalm for doing it without permission.
Technically, aspects of what they do are not illegal under the current laws of Trespass in the UK. Also Civil Trespass is not a criminal offence (it can however be an arrestable offence if signage and warnings have been ignored) .
This explanation is taken from an Urban Exploration site:
“Civil Trespass: Civil trespass, also known as ‘simple’ trespass, is not a criminal offence in the UK. You cannot be arrested for civil trespass, though police may attend if there’s a possibility that another offence has been committed or will be committed. In England and Wales, you can be sued by the landowner in a civil court for trespass, in Scotland you can only be sued if actual damage was caused. Repeat trespass could be prevented if a landowner takes out an injunction.”
Takeaways
This is an important point for owners of offices and tenants of shared/public buildings. It is up to you to secure YOUR perimeters and ensure that people who enter it are verified and authorised and then have left when they are supposed to.
But the next time you are deciding if you need to assess your physical perimeter, get a test done, before someone else tests it for you and posts it on social media, just for fun.