Hackers love your marketing department. Fact!
Your marketing department love telling the world what happens in your company, then they attach images to the posts, often of staff at work. They ensure the subject is central and the image tells a story. The problem is often they tell hackers a different story.
Image analysis has been around since cameras were invented. Using images that your marketing departments publish online attackers can glean useful information about the company and the technology in use.
Really looking at images
One of the problems when we see images is we initially see what the photographer wants us to see, they frame it to draw the eye to the subject. We need to look further. Take the below image courtesy of Pixabay. Our eye is drawn instantly to the lady in focus right in the centre. It looks like office staff in a meeting.

But what else is visible. The dress of the subjects suggest the image was taken when it was colder or that the office is airconditioned – which is the more likely scenario. But there are other things that an attacker can infer.

This laptop appears to be 17in given the extended full size keyboard, the sticker below the keyboard and the branding on the panel suggests an older Dell Inspiron 17 laptop with an Intel processor, from around 2013. Something a little like this.
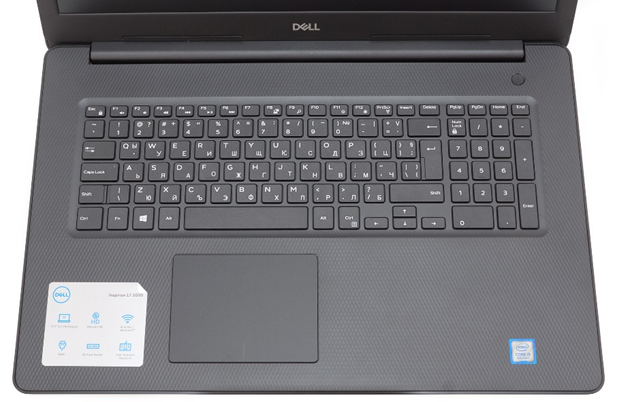
The laptop is also not plugged in to a network, suggesting the office has WiFi. Using tools like Wigle and a company address from the website we could work out the WiFi networks in place.
Also in the image is a printed document, its not completely clear but it possibly resembles a printed email from Outlook.

These two remotes appear to be from a TV and a projector. When doing image analysis commonly you need to make educated guesses and draw on experience and in the case of the remotes we need to so that too.

The black remote looks fairly similar to this Bush plasma remote, although Samsung remotes are similar.
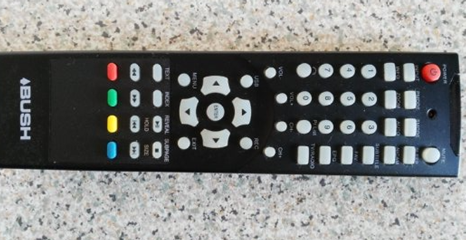
Plasma TV’s were popular a few years ago, when considering the laptop is quite thick, has a full size RJ45 port and is from around 2013, the TV is possibly going to be an older Plasma style TV. The other remote is fairly generic, but could be from a Panasonic projector.

There appears to be what looks like a corner of a smartphone. This allows us to date the image a little more, touchscreen smartphones were only really a thing from 2008, flatter edged phones like this really from the early 2010’s.

The white flat edge of the phone suggests it is an iPhone 5c, With the iPhone 5C being released in 2013 we can assume this photo was taken after that time.

From this one image an attacker can deduce the image was taken post 2013, but the technology is possibly older than that and is unlikely to have been taken much after 2019 as corporate laptop support cycles tend to be a maximum of around 6 years.
We can also deduce that the company likely:
- Uses Dell laptops and therefore probably has a support contract with Dell.
- Has a wireless set up in the office.
- Uses Microsoft Office.
- Used Window 7 at the time the image was taken, Windows 10 wasn’t released until 2015.
- Use Bush or Samsung TVs and use a projector from Panasonic.
That’s from one stock image, many marketing departments think nothing of publishing images of staff wearing ID badges, displaying images of office set ups, applications in use, even sensitive information.
Leaking more serious info
Take the below image. We can clearly see an ID badge with a somewhat dubious colleague photographed…
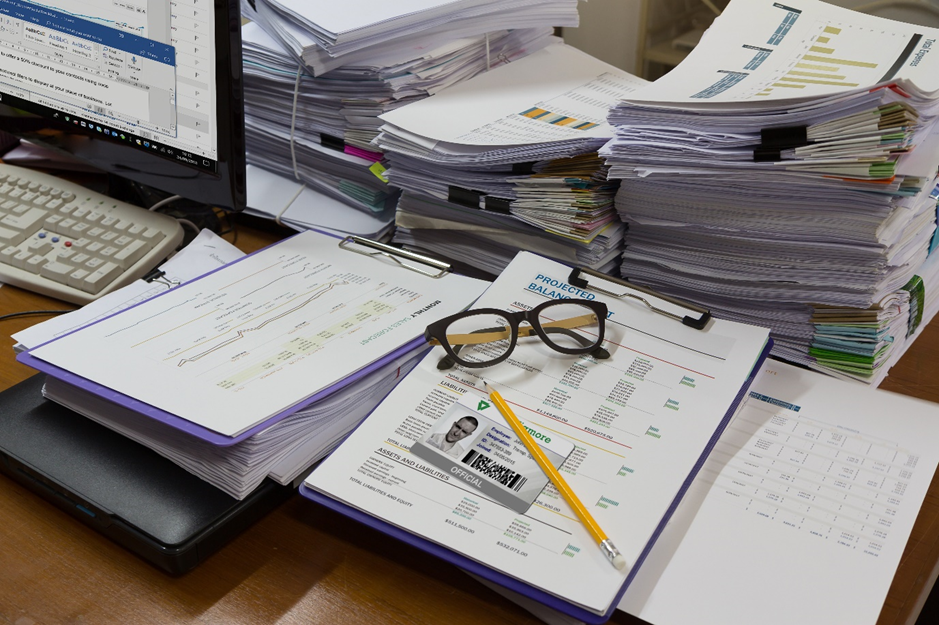
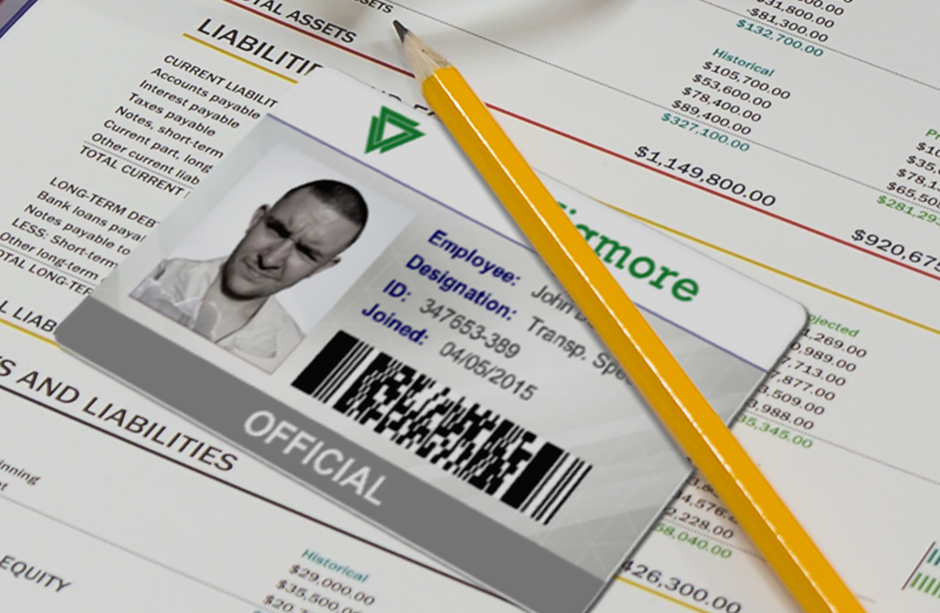
Zooming in we can see a partial company name, employee name and job role, staff ID number, start date, a PDF417 barcode (which is just 1234567890). Additionally, this can easily be used to mock-up a fake version of the card.
Alongside the badge, you can clearly make out financial information. Then looking at the computer we can start to understand what technology is in use on the system.
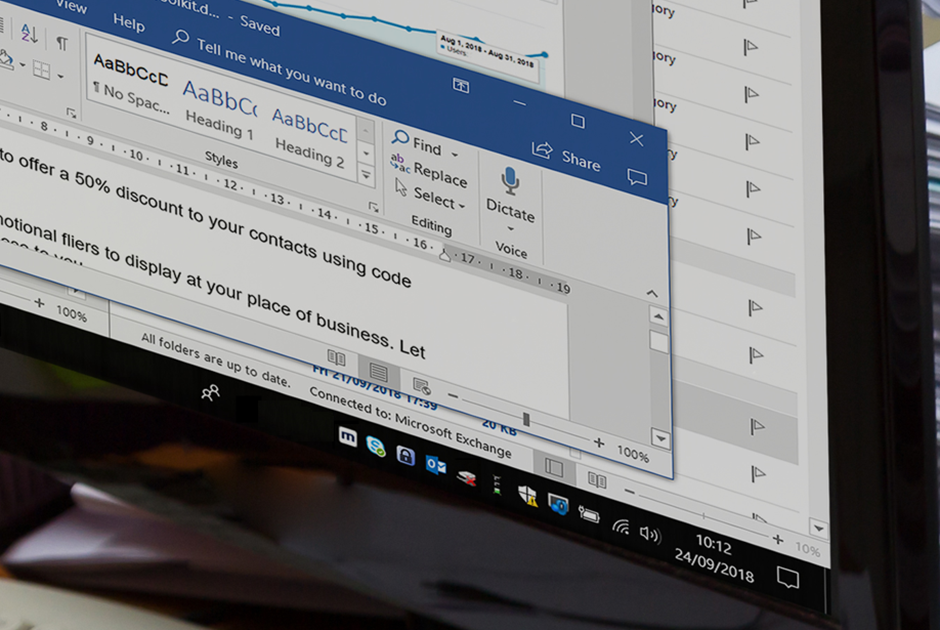
- Windows 10
- Microsoft Office and Outlook
- Microsoft Exchange
- Mimecast
- Microsoft Defender
- Skype for Business
- KeePass
- Google Analytics (could this be a screenshot from the marketing department?)
This allows attackers to customise their attacks to the type of environment they will encounter.
I’ve found multiple images of staff parties held in the office with highly detailed high resolution images of staff ID badges that would be trivial to mock up a clone of, images that leak phone numbers, email addresses, detailed images of the technology in place, even payroll information on one occasion.
However, it’s not just images, HR will often record a ‘day in the life’ videos and upload them to the corporate YouTube channel. These videos usually capture, in high resolution; technology in use, applications, locations, ID badges, office layouts and much, much more.
Taking it further
So really looking at images can reveal sensitive information, but about other artifacts within images.
Within each image file is metadata, typically the big social media services strip that data as it can be highly revealing, giving away; technology, names, locations and a multitude of other information. However, not all do. Services such as Flickr do not strip the metadata. Your marketing teams are also unlikely to strip metadata from images they upload to the corporate website.
This can be easily viewed with online metadata viewers such as https://www.metadata2go.com/, however, I like to use the brilliant Exiftool.
Taking this image I took on my iPhone and using Exiftool we can see the exact location I took the photo.

$ exiftool -a 20201116_124900404_iOS.jpg | grep “GPS Position”
GPS Position : 52 deg 3′ 39.16″ N, 1 deg 18′ 25.84″ W
(No, that’s not my location I changed it to protect my own OpSec!)
One of the things you can get your marketing team to do is strip the metadata from the content they upload to social media and your website. Stripping metadata is easy with exiftool:
exiftool -all= <imagefile>
Beyond Google
There are 4 main search engines for images and depending on what you want to search for they can have differing results:
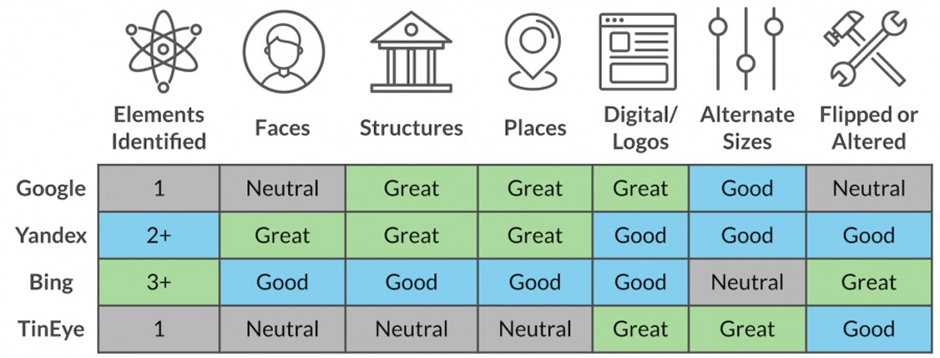
Image credit: DomainTools
I find Yandex is one of the best image searching tools available, one of the very cool features is its ability to selectively search for elements of an image.
Whereas Google is great at finding images of places and so geolocating places like my colleague explained, it’s pretty poor at finding people.
Using the same initial image we can search for just the people and find visually similar images or sites where people have used a cropped version of the image
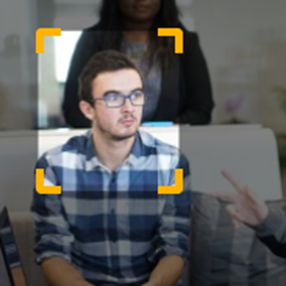
This could reveal other websites to investigate which could lead to websites who are masquerading as your business or even sites that host your staff generated marketing content. Maybe Marketing have stood up a new site or service and have not got it checked for security weaknesses.
There is a pretty useful Google Chrome plugin you can install that can really help with searching images, allowing you to right click an image and search in the four main engines. https://chrome.google.com/webstore/detail/reveye-reverse-image-sear/keaaclcjhehbbapnphnmpiklalfhelgf
In summary
It’s important to remember that tools are not everything, having a technique and a process for discovering what you are leaking is critical and many organisations forget how much is displayed in images just by really looking at them.
Your marketing team will understandably want to keep sharing content, however, its important to talk to your marketing department, make sure they are removing exif or meta data from their files before posting them on the website.
Also take the oppourtunity to train them on how to really look at images to ensure they are not leaking information publicly. This could be a great oppourtunity to create a challenge to help with security awareness. Create an image with some key concerns in it and challenge staff to identify the risks, perhaps rewarding them with a prize if they can demonstrate why the things they found are a risk to the business. Gamification of security awareness is a great motivator and helps engage all departments in security education.
Understanding how you can find other images is really key and knowing what tool to use will really save you wasting time trying to find other images on search engines not optimised for the thing you are searching for.
A thorough assessment of your OpSec will help you to understand what your marketing teams are leaking to the internet.
Read more about OpSec in Red Teaming here.
If you’d like any help, do reach out, I’d happily give you some pointers: @_tonygee_.