If you’ve landed here the chances are you are considering PCI compliance. At present the scheme is running against v3.2.1. In March 2022, the PCI Council released the long-anticipated v4.0.
The Council stated that the changes represent their determination to “continue to meet the security needs of the payment industry, promote security as a continuous process, add flexibility for different methodologies, and enhance validation methods”.
In contrast to earlier iterations, v4.0 offers two avenues for achieving compliance:
- Defined Approach
- Customised Approach
With Version 4.0, businesses gain the flexibility to define and deploy personalized security measures aligned with their specific cardholder data environment (CDE) setup. The innovative Customised Approach empowers well-established organisations to intricately specify their existing security controls to fulfil the objectives for each requirement. Additionally, they are required to have a formalised risk assessment in place to substantiate and validate their customised approach to the chosen requirements. Justification must be documented within the newly added Appendix E (Customized Approach Template).
Implementation timeline:
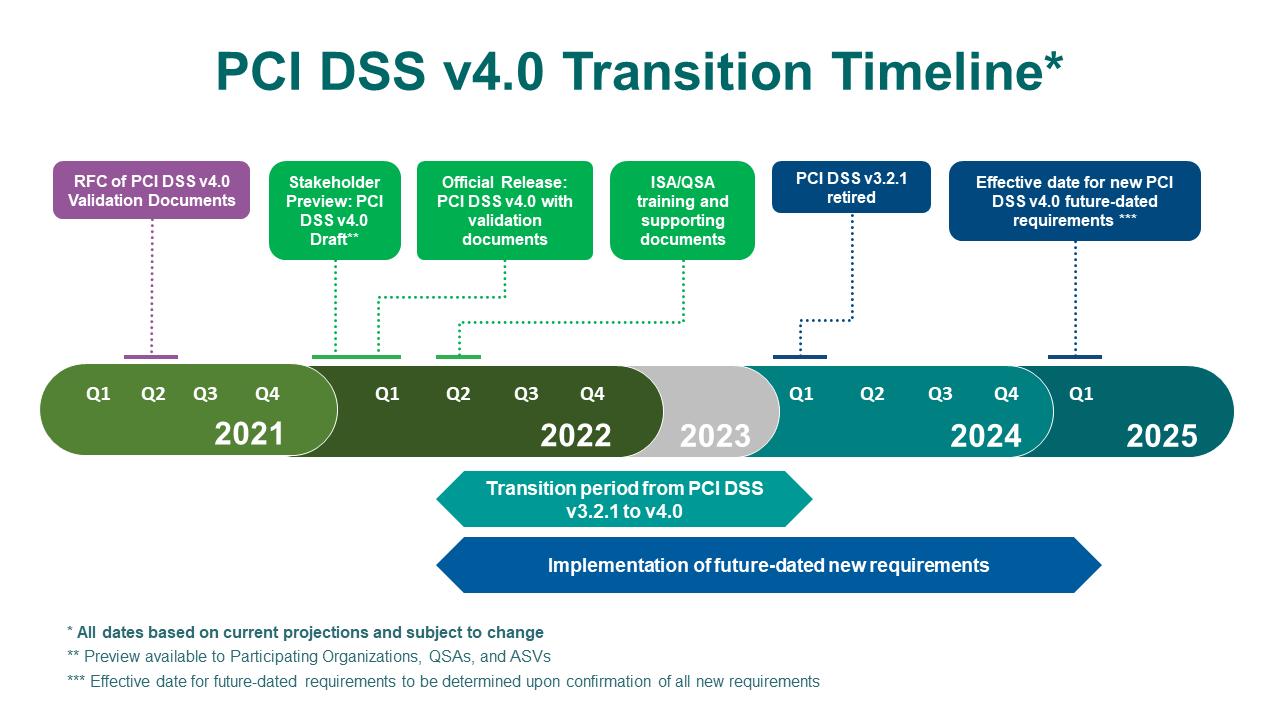
Image credit: https://blog.pcisecuritystandards.org/updated-pci-dss-v4.0-timeline
PCI v4.0 has retained the standard 12 high-level requirement categories, however many new requirements have been added into those sections:
- Install and Maintain Network Security Controls
- Apply Secure Configurations to All System Components
- Protect Stored Account Data
- Protect Cardholder Data with Strong Cryptography During Transmission Over Open, Public Networks
- Protect All Systems and Networks From Malicious Software
- Develop and Maintain Secure Systems and Software
- Restrict Access to System Components and Cardholder Data by Business Need to Know
- Identify Users and Authenticate Access to System Components
- Restrict Physical Access to Cardholder Data
- Log and Monitor All Access to System Components and Cardholder Data
- Test Security of Systems and Networks Regularly
- Support Information Security with Organizational Policies and Programs
Organisations operating complex cardholder data environments (CDEs) may find that certain new requirements could exert a substantial influence on their security initiatives. The new requirements and associated security controls that need to be implemented include 64 changes that effect all entities and some specific to service providers only. Some come into effect immediately for all v4.0 audits and others come into effect on the 31st March 2025.
Key PCI DSS 4.0 Requirement Updates
This section is an introduction to key new requirement changes in PCI DSS 4.0. Whilst this list in not exhaustive it highlights the most pressing changes being introduced. (A full list of those changes can be found here):
Section 1
No significant changes in this section.
Section 2
No significant changes in this section.
Section 3
Sensitive authentication data must now be encrypted or protected if stored before authorization. Furthermore, technological solutions must be in place to prevent the copy and relocation of PAN data. Disk level encryption is no longer permitted for protection unless it is a form of removeable media (e.g., USB, external SSD). Hashing has also changed, organisations will need to use a keyed cryptographic hash method which is different from most common hash algorithms in use (HMAC, CMAC, GMAC and a strength of at least 128-bits).
Section 4
New requirements call for detailed documentation, tracking, and inventory of SSL and TLS certificates used for sensitive data transmission across public networks.
Section 5
Scanning of removable media used in the Cardholder Data Environment (CDE) is now required. There is also now a requirement to have automatic process mechanisms in place to detect and protect personnel against email phishing.
Section 6
A requirement coming into force in March 2025 is that organisations will need to have a web application firewall in place for any web applications exposed to the internet. There is also a requirement to prevent malicious scripts being run on payment pages. Organisations will need an inventory of all known scripts used within these pages and it must be documented and tracked.
Section 7
Not much has changed in this section. Roles and responsibilities are now to be defined as is review of all user account and privileges.
Section 8
Password strength requirements have increased, moving from a minimum of 7 to 12 alpha and numeric characters. If using just passwords for authentication, service providers must change customer passwords every 90 days. MFA will now be required for all access into the CDE, not just external locations. Furthermore, success of all factors included in authentication must happen before authentication itself. The process cannot divulge which part of the journey has failed. This means no more ‘your password is incorrect’. Both factors will have to be presented and entered without revealing any information about which factor is incorrect if authentication fails.
Section 9
No significant changes in this section. There is a new requirement for roles and responsibilities to now be defined.
Section 10
Manual log reviews are no longer permitted; automated methods are now required. Detection and alerting capabilities must be in place to address failures of critical security control systems. This requirement has extended from service providers only to everyone.
Section 11
Internal vulnerability scanning must now be authenticated, a necessary addition for e-commerce. IDS/IPS solutions must detect and alert on any covert malware communications being used such as DNS tunnelling. A further new requirement has been born, a change and tamper detection mechanism for payment pages is now mandated. This is to reduce and prevent the risk of skimming attacks.
Section 12
Annual scoping of your card data environment has been made a trackable requirement effective immediately for version 4.0. A documented scoping exercise will have to be done by merchants annually, or after any significant changes to the in-scope environment (e.g., people, systems, processes). For service providers, this exercise must be carried out at least every six months and after any organisational changes.
A formal security awareness training program has been introduced where before you could meet the requirement with some basic security training. This program must be reviewed and updated every 12 months to encompass any new threats that could adversely impact the security of their CDE. This training program should now discuss specific threats and vulnerabilities to your environment. Incident response procedures will need to be invoked if PAN is detected anywhere unexpected. Review of this process should be undertaken periodically to meet this requirement.
In conclusion, reading the new v4.0 standard will aid you in getting familiar with the bigger changes that could impact your organisation. Understanding which type of SAQ or ROC assessment you’re subject to will allow you determine which controls are applicable to you.
How to choose an SAQ for your organisation:
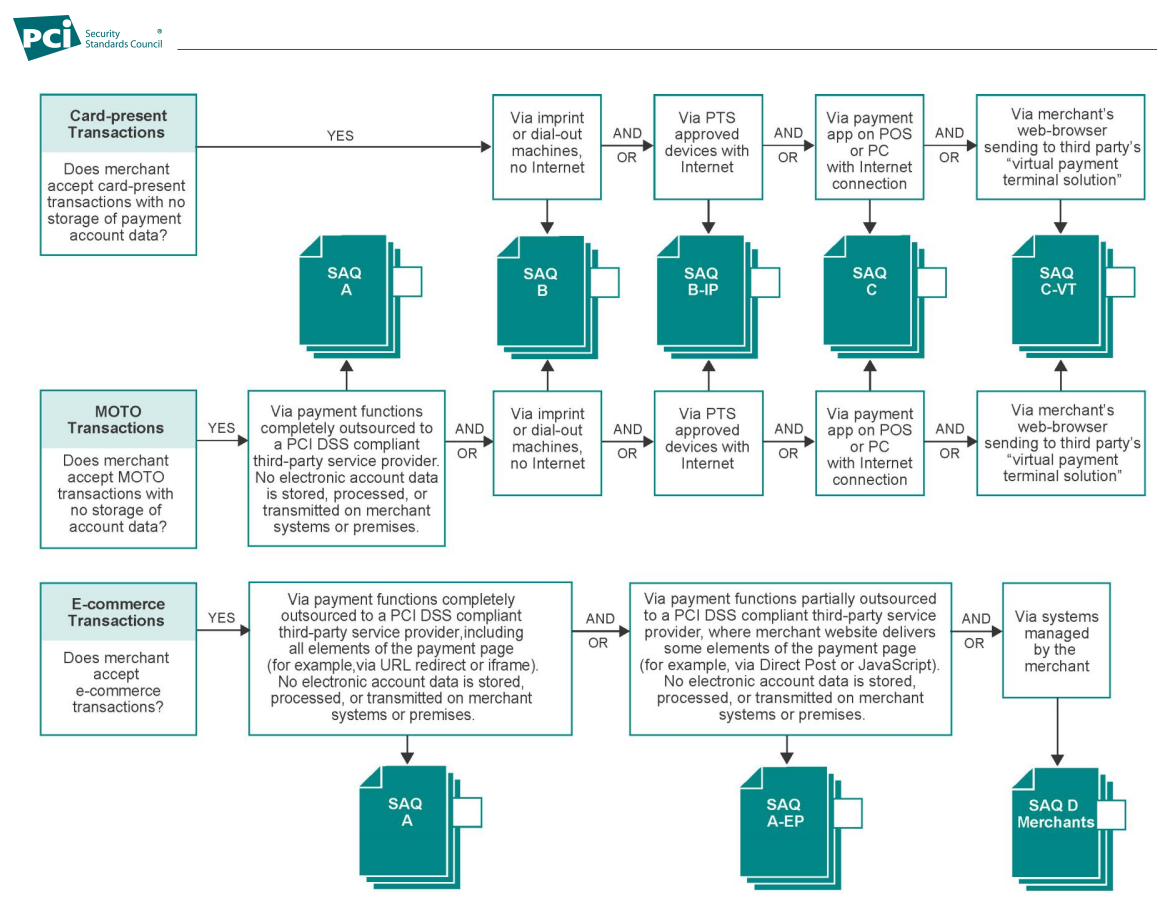
Image credit: https://docs-prv.pcisecuritystandards.org/SAQ%20(Assessment)/Instructions%20%26%20Guidance/SAQ-Instructions-Guidelines-PCI-DSS-v4-0.pdf
References:
https://listings.pcisecuritystandards.org/documents/PCI-DSS-v3-2-1-to-v4-0-Summary-of-Changes-r1.pdf
https://listings.pcisecuritystandards.org/assessors_and_solutions/qualified_security_assessors