I saw a really nice demo on the BBC this morning, where my old friend Cayla the swearing doll was used to control a door lock using voice commands. As she has no Bluetooth pairing PIN, one can easily have her speak audio commands in the victims house that a listening device will hear
The lock in the demo was probably a Yale Keyless Connected which integrates with Samsung Smart Things over Z-Wave, which there is an Alexa/Echo ‘skill’ for. That’s probably how the voice control was done.
That got us thinking about how this attack could be made a whole lot better. This ‘hack’ is limited by the following:
Cayla isn’t always on, as she is battery powered
If she is already paired with another Bluetooth device (i.e. the child’s smartphone) then de-auth’ing over Bluetooth can be very difficult. She will only communicate with one Bluetooth device at a time.
It’s hard to locate Cayla dolls, as they only use Bluetooth.
How to make it better? Use Google Chromecast, not a child’s doll!
Why?
Chromecast is always on, as it’s attached to mains powered devices. Chromecast can also turn the TV on over HDMI if it’s already switched off.
It is a Wi-Fi device, so we can locate it using https://wigle.net – Wi-Fi also has much better range than the short-range Bluetooth device in Cayla
It’s generally connected to a decent TV or audio system; so far better sound quality than Cayla’s speaker. Much more likely that Alexa will recognise the command
Chromecast has some interesting security issues that we can exploit.
We’ve blogged these issues previously but here’s how you use them:
The Chromecast (CC) has an open Wi-Fi network that is used to initially set up the device and to allow guests to connect. If ‘guest’ access is disabled, the CC is only a wireless client to the home Wi-Fi network. That’s not much use to us, as we would need to crack the PSK first and also geo-location of Wi-Fi clients is much harder
But…
After setup, we noticed that if the CC can’t connect to the home network, it falls back to setup mode and the open access point is started again. We tested this by sending a de-authentication packet to the device and the open guest AP popped up.
So, you de-auth the Chromecast, and you can access the open AP again…
After connecting to this open AP it was possible to send a factory reset command to permanently put the CC in setup mode. The CC could then be connected to the attackers AP and arbitrary content streamed directly from an attackers phone.
However, there’s an easier attack than that. Given ‘guest’ mode is usually available (disabling requires an ‘uncheck’ in the setup) then one simply connects a device to the open guest AP. Only YouTube content can be streamed, but that’s fine. We simply create a YouTube video containing the audio commands we want the Chromecast to play!
To play audio, you simply “cast” whatever is playing on your phone to the Chromecast or command it to stream from YouTube.
Alexa hears the TV play the audio content you want it to hear, and takes action on it. Door unlocked, or any other recipe the user has implemented.
The fix
…er. there isn’t one.
It would be wise to ensure ‘guest’ mode is disabled in your Chromecast, but be aware that it’s possible for an attacker to re-enable this mode by de-authenticating the CC from the home access point
Finding Chromecasts
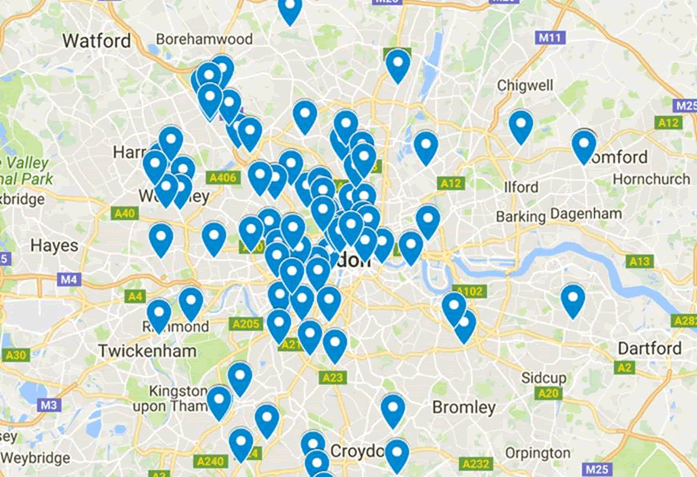
Off to https://wigle.net and search for ‘Chromecast’ – the SSID generally has a space and four trailing alphanumeric characters, e.g. Chromecast 6488. Here are a few in London:
Voice control gets more serious
The example in the NCSC demo showed Cayla repeating a command. They didn’t even need Cayla to do the hack though – we could have simply shouted the command through a window!
However, we found some rather more concerning voice recipes in Alexa. A couple of voice activated house alarms, which our Chromecast attack can be used to disable!
“Thanks to the Myfox Security Skill, you’re now able to control you Myfox Home Alarm and Myfox Security Camera using your voice.
With it, you can : arm and disarm the alarm, enable and disable the night mode, open and close your Myfox Security Camera shutter, have a quick summary of the daily events or the weekly events.
Everything is secured with the passcode you have to set ; there’s no risk of your child disarming the Alarm!”
“abode is the first professional-grade, self-installable home security solution with no contracts that also allows you to control locks, lights, thermostats, and other popular connected devices.
- “Alexa Tell abode that I am leaving”
- “Alexa Tell abode to standby”
- “Alexa tell abode to lock all my doors”
But of course the most important thing you could say to Alexa would be ‘order 10 My Friend Caylas’














