On the last day of IFSEC 2018 I was considering just how bad the security of some alarm products is. So, two years on from this post, has this sector’s security improved?…
PIR jamming
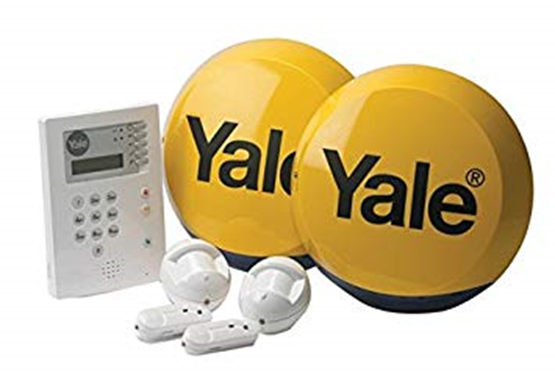
First up is Yale Security with their trivially jammable wireless alarm system. You can replay disarm codes, and the PIN is sent in the clear. We can even brute force the PIN code over RF.
Many wireless alarms are as easy to jam. The might have jamming detection, but if you let the status messages get through and jam the alarm messages… the siren doesn’t go off.
Rubbish encryption
Next up, RISCO Group with their laughable Lightsys encryption. The encryption only has 256 keys, defaults to “2”, suffers from known plaintext, is malleable and has no authentication… so completely broken. More on this issue here – links to a post from 2015, still relevant.

Their configuration software also stored passwords encrypted with a hardcoded key. Why they weren’t hashed I don’t know (link to post from 2015- still relevant).
Backdoor accounts
Then Visonic with their hardcoded backdoor root account (another still-relevant 3 year old post) on all of the PowerLink 2 modules….

This isn’t great is it? Let’s go on.
“Military Grade Encryption”
Then we have Videofied’s system, which uses “military grade” encryption and AES. Shame the key was derived from the serial number that was transmitted in plaintext. More on this issue in a 3 year old post here.

Conclusion
If you are planning on buying any alarms, IP cameras, VMS, access control systems, smart locks… just remember that what the vendor says about security may or may not be true.
Their assessment of risk may be way off the mark – their view of an attacker may only be a tracksuit-wearing crook throwing a brick through your window. The actual attacker might be a nation state attacker looking to pivot onto your network.
So ask them: Have you had your solution properly tested by a third party?
Most sales people will avoid the question entirely, and state that they comply with standards. Possibly the most rigorous standards. Standards they don’t even need to comply with.
The standards for electronic security are terrible. They are out of date before they are released, set by people who want them to be the lowest common denominator because their products would fail otherwise.
Worse still, large parts of the alarm security standards are “self-certified”. Do you use AES-128 or above? YES SIR we do! That their implementation of AES-128 is trivially defeated is not validated.
Sadly, none of the large test houses that accredit alarms possess a good penetration testing capability; it’s not in their interests to go beyond the standard as they then won’t win the accreditation work from their customers, if they set a higher standard!
Some of your competitors have made great progress with their security.
Do you want to be left behind? …and end up like this https://www.google.co.uk/search?q=tapplock&tbm=nws














