A while back we demonstrated a bunch of concerns about the Smarter Coffee machine and iKettle 2.0 security.
I hadn’t re-visited the piece for some time, but the consequence was that it wasn’t hard to take control of a coffee machine over Wi-Fi, force it to make coffee then leave it to go cold. Empty water reservoir, empty coffee bean hopper. Cold coffee. Bad day. Worse, it can be forced in to a firmware update loop, turning it into a large, pointless appliance-shaped brick.
A little annoying if the sole purpose of your coffee machine is to make coffee to order.
Now, it’s one thing cracking home users Wi-Fi keys to do this, and hard work just to annoy the owner.
However, we keep finding these coffee machines and kettles on wigle.net in an unconfigured state. From here, it’s trivially easy to carry out the attack.
The SSID format is ‘Smarter Coffee:aa’ where aa is a hex value. So search wigle.net and we get this lot:

What I’m most interested in is those that have been- and will likely be unconfigured. Simply delta the ‘first seen’ and ‘most recently’ values and we get a list of those that have been left unconfigured for longest:
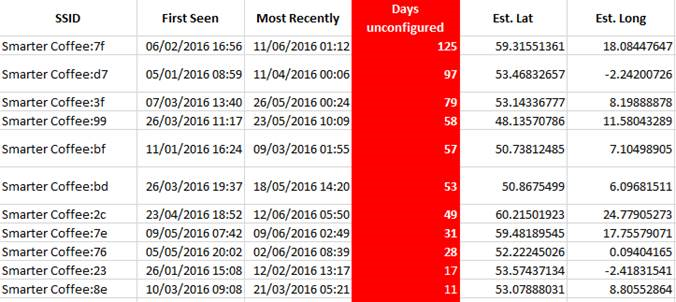
If the owner hasn’t configured it say 30+ days after buying it, it’s likely they’re just using it manually, i.e. not using the Wi-Fi function, so has no intention of configuring it.
And here’s one of the worst offenders, right in the middle of Manchester. The exact lat/long are in the table above in the row starting ‘Smarter Coffee:d7’

We can do exactly the same attack against an unconfigured iKettle 2.0
SSID format: ‘iKettle 2.0:aa’
Here’s one that’s been unconfigured for nearly a year, roughly the last time we posted about the iKettle 2.0.
The SSID is ‘Smarter Coffee 2.0:55’

One could boil their kettle to order, steam their house out. The kettle can also be forced in to the same firmware update loop. Brick!
Don’t leave unconfigured wireless devices enabled in your house! Set them up properly, or turn them off.














