The story today that TalkTalk suffered a serious breach yesterday is big news, and rightly so. With some people saying that it’s a matter of national security and many customers still unsure of the impact on their lives Ken talked to BBC News today about the incident, [updated 24/10/2015] and explained an SQL injection attack to the BBC World Service’s Tech Tent.
Speed of news
TalkTalk went public with the news very quickly, maybe before fully assessing the breach themselves.
This rush to warn customers might damage their brand more than needed, so what other factors might be at play?
The information posted on Pastebin by the supposed attackers could suggest to some that TalkTalk were being blackmailed or extorted, or just as likely that simply the hackers wanted to embarrass them. By going public so quickly with the disclosure they would have put paid to that.
DDoS?
There is also talk of a DDoS. Those in the know understand that this type of attack doesn’t necessarily mean data extraction is the goal, in fact that is pretty unlikely. What is much more likely is that a DDoS is used as a diversionary tactic, to distract the security team while other attacks are attempted. If this was the case then security professionals should know to manage that attack AND look for other types- the ones that lead to illicit data extraction.
They say that they fixed problem quickly, which is great, but it begs the question, was this breach a result of the exploitation of a simple vulnerability? If it was due to a simple vulnerability like a missing patch then why had it gone unchecked before?
Databases
Another factor to consider here is the exported list of databases also posted on Pastebin, here’s a snippet:
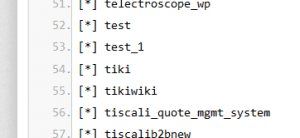
If the list is true and accurate then there are concerns about whether these sorts or databases should be running on the same box at all. Having things like tikiwiki and test and live databases unsegregated is a bad idea.
Conclusion
Unfortunately for their customers it looks like TalkTalk have been caught with their pants down. A “simple” breach shouldn’t be as devastating as this, and if it was due to a DDoS then it hasn’t been going on over a long period of time.
People can’t stop every breach, but they should at least be able to detect when it’s happening and react accordingly with their incident response plan.
CREST has a comprehensive guide to Cyber Security Incident Response here.













