I’m sure you will have all seen the news of the latest ‘critical’ vulnerability VENOM.
The marketing department must have been working on overdrive to come up with all the FUD (Fear Uncertainty & Doubt) to generate the amount of headlines.
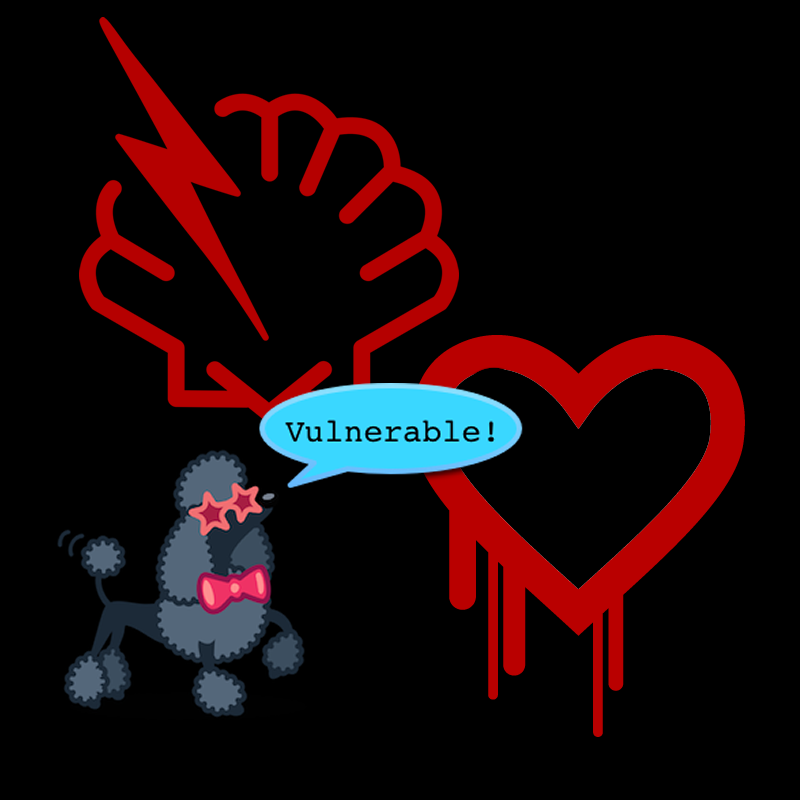
Much like Heartbleed, POODLE and Shellshock before there was a fancy logo and a slick website. VENOM even had a secret press briefing ahead of the notification to ensure maximum coverage.
I understand the desire of these companies to use their findings to promote their business and I’m not at all wishing to detract from the very good research done by the identifiers of these vulnerabilities, but why do they need a fancy name, a website and a secret press briefing. It’s just unnecessary and, as in the case of VENOM, totally distracted from the actual vulnerability.
Let’s look at VENOM
VENOM is an interesting find and is a viable exploit (in the right conditions), with significant potential to affect a number of organisations and hosting service providers. What I have issue with here is that the press unsurprisingly lapped up the slick PR briefing. Hence VENOM got lots of coverage. That sounds great, doesn’t it: everyone gets lots of warning about the issue. Board rooms wake up and take interest.
However, this has two contentious consequences for me:
First, the profile of the vulnerability is influenced by the ability of the researcher to promote their findings, not necessarily its criticality. So, decisions about remediation are more likely to be based more on PR than risk.
Second, exec boards are likely to become tired of these issues in time. We already see ‘breach fatigue’ emerging with Joe Public. Too many big breaches making the press, ‘what hope have I got’ they say. How long before we see ‘vulnerability fatigue’ at board level – too many security bugs making the press?
We have seen hard evidence of that most recently with a test we performed for an organisation where we noticed that the website was not vulnerable to POODLE due to the admins disabling SSLv3, however, they completely neglected to disable SSLv2 as well as other unnecessary and vulnerable services.
Counterproductive?
As pen testers we seek out every vulnerability irrespective of name, logo or website, but as an information security manager who has so much to focus on day-to-day, having their boss come and tell them they need to fix this “Insert silly name here” vulnerability immediately because the press said that millions are affected is counter-productive. Remediation of vulnerabilities should be performed in a controlled, methodical manner. Importantly, they need to be risk assessed, and it’s very hard to do that when there is so much hype over something that is, in a lot of cases, something you are not vulnerable to.
Back in 2008 MS08-067 was announced by Microsoft and as we all know was then used by Conficker to infect many computers. The vulnerability was probably as bad as it gets, full remote code execution as SYSTEM, but there was no fancy website, no fancy name and no marketing program. Even now every month new remotely executable vulnerabilities are found and fixed, most recently MS15-034, a vulnerability for which there is publicly available proof of concept code to exploit and crash a Windows webserver. If you hunt around some of the darker parts of the web you’ll even find full remote exploit code to take over the server.
Look before you leap
Perhaps it’s time to turn away from the hype, look at the facts and methodically assess the risk of each vulnerability to your estate, before you panic over for the latest vulnerability in the press.