The other day my Xiong Mai demo DVR broke, just refused to boot. Annoying but it did prompt me to go and buy some more. Sadly the device I originally bought is no longer available so I set about buying some other Xiong Mai DVRs.
Why Xiong Mai? We have shown previously how a number of Mirai vulnerable DVRs are linked back to a company called Xiong Mai based out of Shenzhen, China. They write the software that runs on the HiSilicon chipsets used by millions of Mirai vulnerable DVRs .
I got a KKMoon branded Xiong Mai DVR from Amazon and set it up.

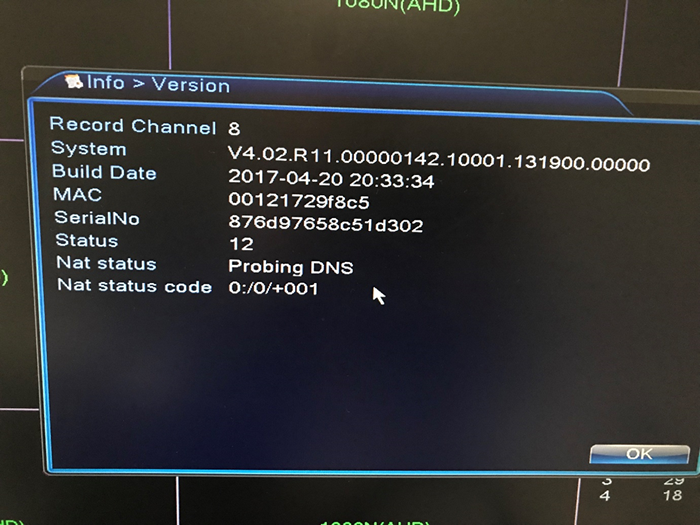
A quick check of the version screen and I can see it is running firmware from April of last year:
Hmm, so they have updated it, makes sense as this is a new looking device. Let’s portscan:
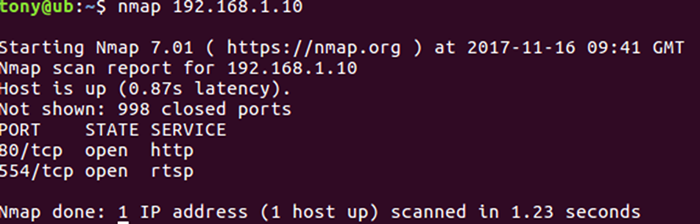
Hang on a second, no Sofia application shell, no telnet, no dodgy high ports. Just port 80 and 554. That’s an improvement.
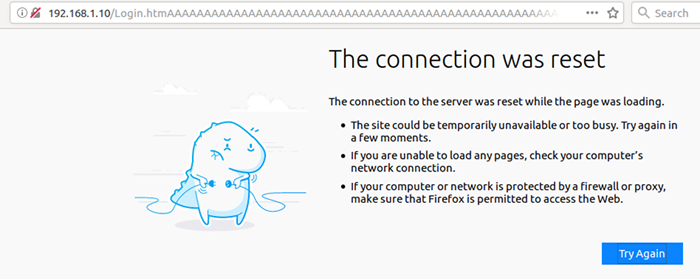
The web interface still used HTTP, rather than HTTPS, but what about the buffer overflow in the web server we discovered. Well passing the same test string appears to cause the buffer overflow on the face of it, but when refreshing the web page we can see it hasn’t caused the application to crash.
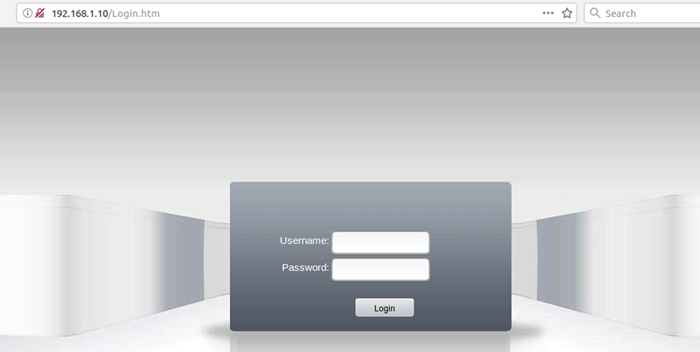
Also the device doesn’t crash and reboot when viewed directly not through the web interface.
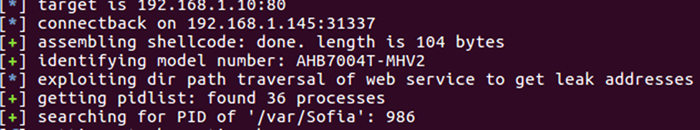
Interestingly the directory traversal does still seem to be present. The POC from Securiteam does collect the Sofia application process ID, but can’t execute the overflow.
It’s not clear at this stage if the fix has been performed by Xiong Mai or an upstream provider, nor how they have fixed it, but either way this is good for consumers and does show that Xiong Mai are listening to researchers, even if they don’t respond.
It be would ideal if they fixed all of the issues, but this particular attack seems to be on the face of it fixed. Certainly the attack surface of the device is greatly reduced by the removal of Telnet and the Sofia shell.














