In our last toy related post we mentioned My Friend Cayla, here we’ll lift the lid on what we found.
Cayla is effectively a bluetooth headset, dressed up as a doll. Yes, you can actually make phone calls by holding her to your ear.
The real fun starts with the mobile app that she interfaces with. It’s available on iOS and Android, but for this task we looked at the Android version, as it’s generally easier to intercept, decompile, and modify the code.
The mobile app contains a database of common questions and answers, laced with some obvious product placement to keep retailers happy e.g. if you ask Cayla “Have you been to Toys R Us?” she will reply:
“I’ve been to Toys R Us. Hasn’t everyone? (giggle) I love it there because I get to look at all the new toys. I wish I could work there some day and play with all the cool toys all day long. That sounds like a fun job.”
If Cayla doesn’t have a stock answer stored in the local database she will use the Wikipedia API.
She also has a local database of around 1,500 “badword”s. If these are asked for by the child, or are contained in a repsonse from Wikipedia, Cayla will give a generic santised response, “I don’t want to talk about that”. We are sad to see that “gay marriage” is listed as a badword.
There are four main attacks that we’ve identified so far:
- Sibling stalker- modifies database contents on the child’s phone
- MitM attack- between the phone abd the internet modifying requests/responses in transit
- Backdooring of Cayla herself
- Random pairing- when her master device goes out of range an attacker’s device can be paired with one acceptance tap
In this post we’ll look at the first of these attacks.
So, CAN WE MAKE CAYLA SWEAR?
First we need local access to the mobile device. This is likely to be easy as a simple matter of knowing the PIN- typically most children’s devices will have either a simple PIN or no PIN at all.
Next we enable adb via Developer Options on the device, plug it in to a computer running Linux via a micro USB and access the adb direct from there. The data dictionary file we’re looking to modify is /data/data/com.toyquest.Cayla.en_uk/databases/cayla.cd.
Here’s the process:
su
cd /data/data/com.toyquest.Cayla.en_uk/databases
cp cayla.cd /sdcard/cayla.cd
exit
exit
adb pull /scard/cayla.cd
Load cayla.cd into a SQlite client (I used DBeaver) and edit the questions table. These examples show our modified response to “hello”, which is “I could be feeding hacker filth straight to your children. Does that worry you”. It also shows a freshly created question “who is dave lodge”:
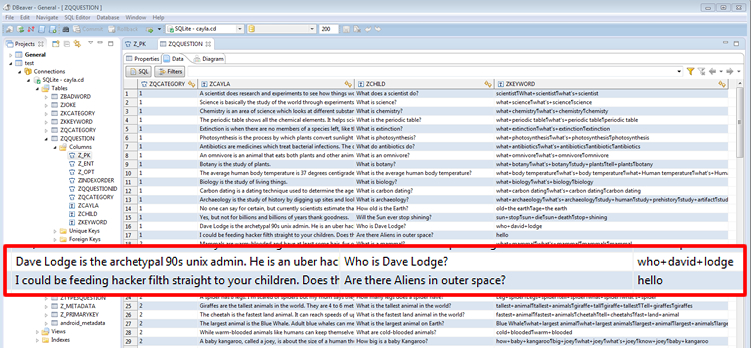
…then upload it back to the app:
adb shell
su
cp /sdcard/cayla.cd/data/data/com.toyquest.Cayla.en_uk/databases/cayla.cd
Now, with our modified data dictionary file we can get Cayla to swear like a docker, a very sweary docker at that.