An awesome researcher contacted us on the back of our recent Tapplock pwnage. We had been looking at the local BLE unlock mechanism, however he focussed instead on the mobile app API.
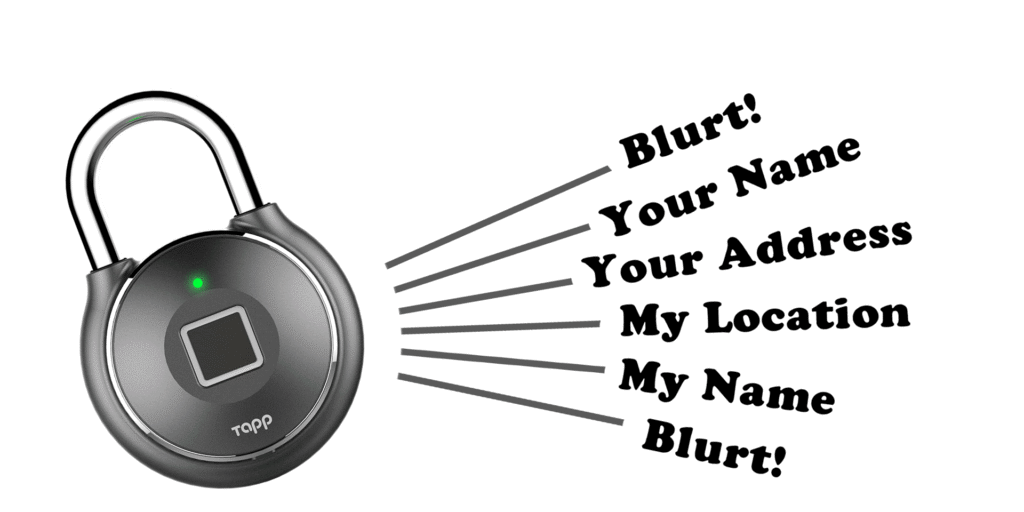
Vangelis Stykas (@evstykas) has found a way to unlock any lock, plus scrape users PII and home addresses.
Read his blog before you go further.
All we did was verify his work and help with the disclosure process, so do read his work and follow him.
Hijacking Tapplocks the API way
There’s a Direct Access Object issue in the API. Create user B and one can access user A’s details.
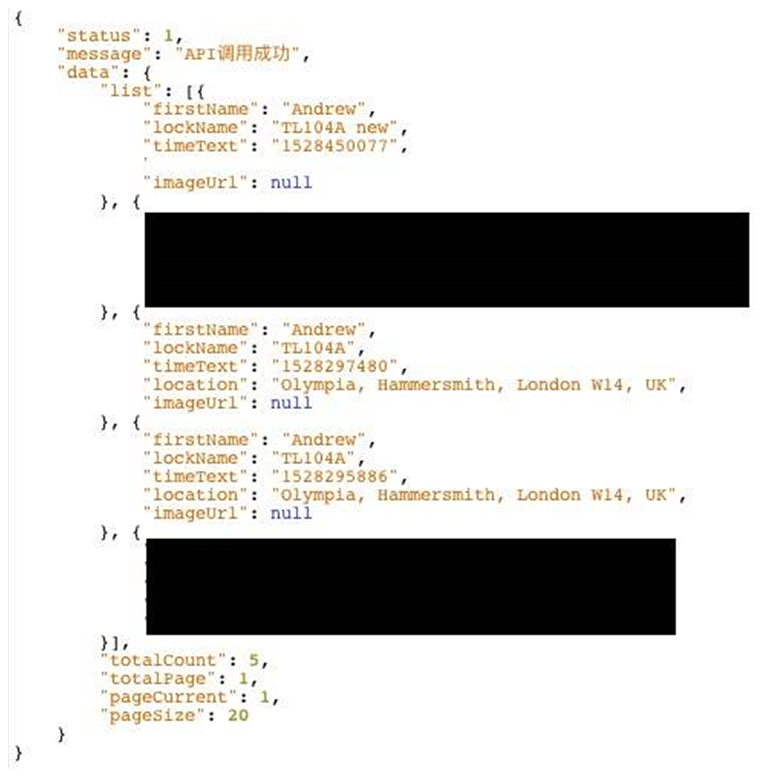
Andrew (@cybergibbons) gave Vangelis permission to view his account as a proof of concept.
Simply iterate incremental IDs (yes, really) and you get user name, lock name and unlock locations. The redacted areas in the image below are Andrew’s home address, where the locks were.
We tested the BLE issue at the Infosecurity Europe show, hence ‘Olympia’ is displayed, as that’s where we also took the locks.
One can also ‘share’ any lock permanently with any other account. This means one can hijack any lock, geolocate it and unlock it. FFS!
OMFG. Disclosure
Clearly there is potential for a significant data breach in a product that is getting a lot of attention from security researchers and less ethical actors.
We discussed this with Vangelis and agreed that the only option was to insist that Tapplock took down the API.
In fairness, after a bit of prompting, their response was very quick: they’ve agreed to take the API down and fix it. Vangelis published the flaw only after the API was taken down
Conclusion
This is mind blowing. We thought we had a killer hack with the BLE flaw, but it goes to show that further time often leads to more awesome findings.
We’ve since had contact from three more researchers who are well on the way to making further fascinating discoveries with the Tapplock.
I’ve spent years trying understand what leads vendors to release vulnerable IoT product, and published my experiences, thoughts, and advice here.