We’ve been looking at the security of smart ghost hunting tech. The results were a bit… spooky.
TL;DR
We bought three devices online. One was a camera for taking photos of ghosts, another was a smart teddy bear for helping ghosts of children apparate, the last a ghost hunting tank camera:
- In some cases, the price was up to 5x the cost of the non-ghostly product they were based on
- Claims about ghost detection were made, yet we showed that some of the hardware wasn’t up to detecting anything, let alone the paranormal
- The smart products could expose the security of the ghost hunter
- If tech-savvy ghosts do exist, we will show how spooks could exploit the insecure hunting devices and cover their traces.
So, however often you’re out there hunting ghosts, remember that threats might come from the tools you’re using and the people you buy products from- in addition to the ghosts you’re hunting. Please, stay safe out there.
Lots of smart technology is available for aiding ghost hunters. We reverse engineered several devices and found some surprising results. In the words of Ghostbuster’s Peter Venkman “Generally you don’t see that kind of behaviour in a major appliance”.
Ghost Pro

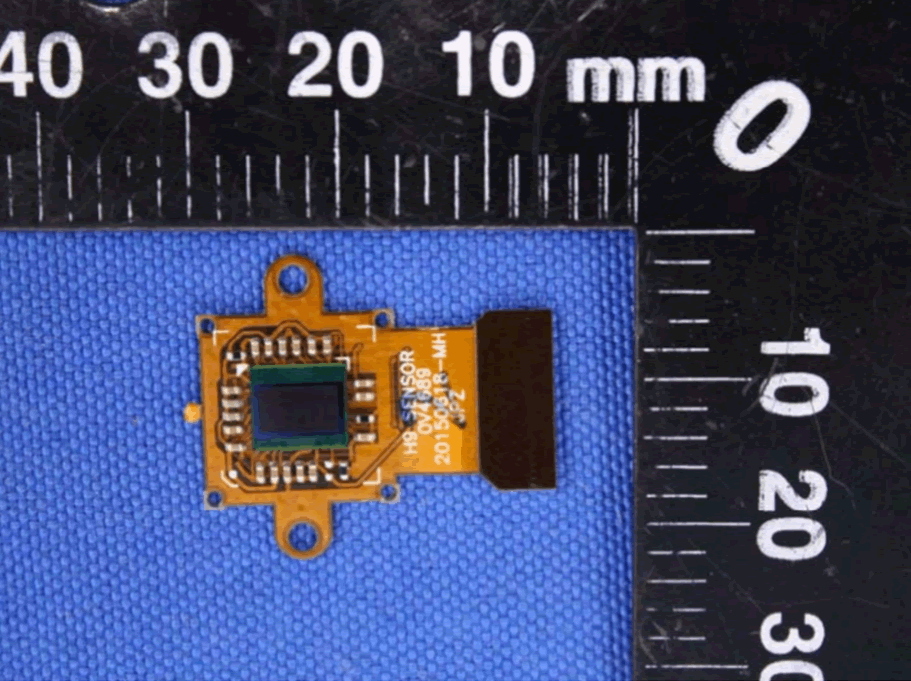
The Ghost Pro is said to be a full spectrum camera used to film “infrared, visible, and ultraviolet light spectrums.”
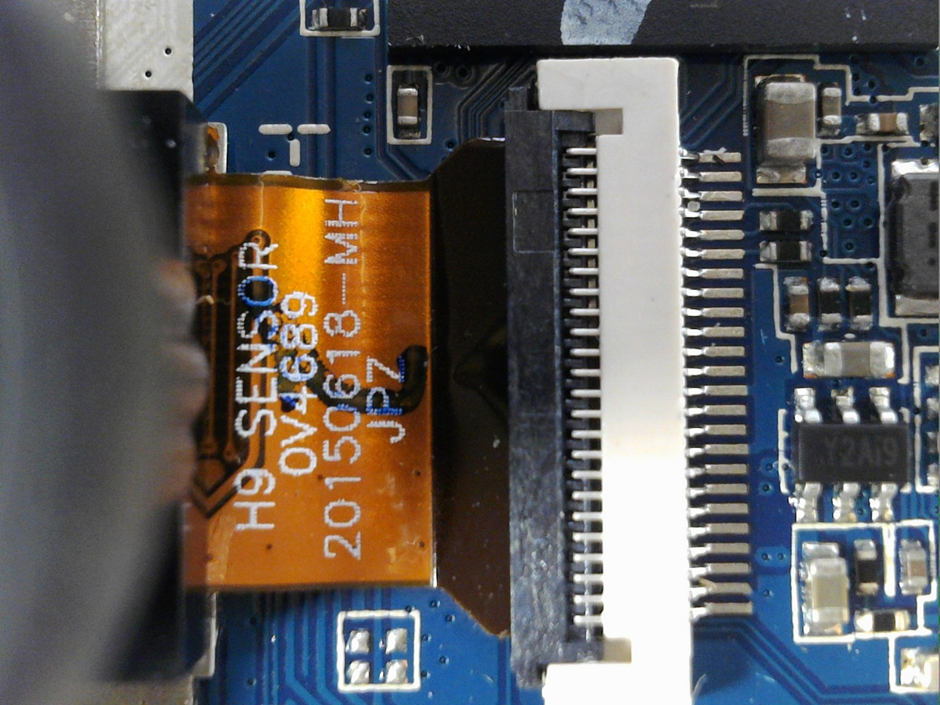
Very similar in design to Eken’s H9 camera, the Ghost Pro has near identical internals. It says is has a ‘full spectrum sensor’ but it has the same physical sensor as the H9.
The security of this camera is quite concerning: First off the Wi-Fi PSK is hard-coded: “1234567890” – you can’t change it. Once attached there’s also an FTP service you can connect to, then either download all the video files or just delete them. Technically competent ghosts could simply delete all your footage. MWA-HA-HA.
If that’s not your bag then you could view streaming files or send a malformed packet to crash the device.
Here’s the full teardown and security review: Ghost Pro
Boo Buddy

The “Boo Buddy” is sold as a “trigger object” to attract the spirits of children. It’s supposed to have a wide range of internal functionality such as EMF, motion and temperature detection. Inside its fluffy body lies the PCB. Here it is released from its 3D printed plastic case:
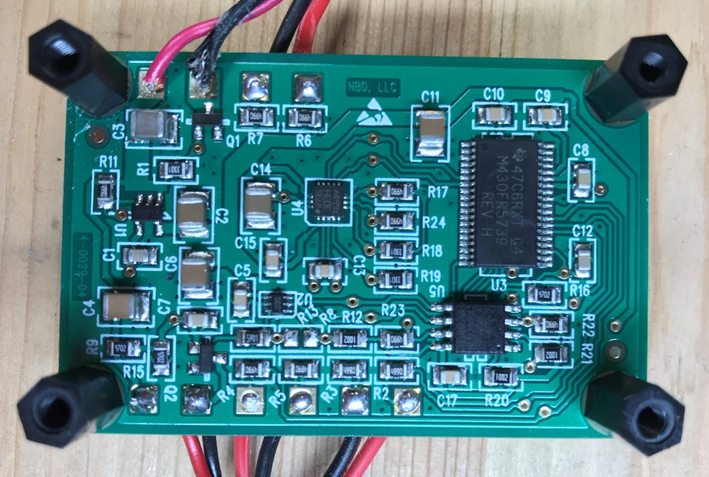
I estimate that it costs about $30 to manufacture the whole thing, so with an RRP of $299.95 that’s quite a mark-up. Even with a discounted sale price it’s still about $160. So, what does all that money buy?
Let’s see how it actually performs for detecting EMF. I built a test “ghost” – a very basic electromagnet powered by a 9V battery.

Our ghost simulator
It’s just an electromagnet, but it’s generating some EMF fields. We can make sure it’s working using an actual EMF detector.

Yes, that’s working. If a ghost rubs up right against the detector, we ride into the “danger zone”!
Now, let’s see how the bear board reacts.

We’d expect the LEDs to light up. But there’s no response at all. Nothing, not a peep, no EMF detection whatsoever. Maybe it detects something else, but we couldn’t work out what…
There’s not much to see from a security perspective as it’s a stand-alone device with no app or network connectivity.
So, for $299.95 you can have something that doesn’t seem to do what it’s supposed to. Spooky, right?
If you’re as confused as we are, here’s the full review: Boo Buddy
Ghost Rover

As with the Ghost Pro camera this device is a lot like its non-ghost busting stable mates.
We did a review of an app-enabled camera tank three years ago, this device is not that different. Drive it around using the mobile app and view the feed from the (IR) camera. Interestingly it looks like the IR functionality is introduced in the same way that it is on the Ghost Pro, by removal of the IR filter between the lens and sensor. For that reason $200 seems pricey, considering you can get a normal tank for less than $80.
IR aside, let’s look at the security. Using Telnet you can use the hard-coded password to get root access to the OS:
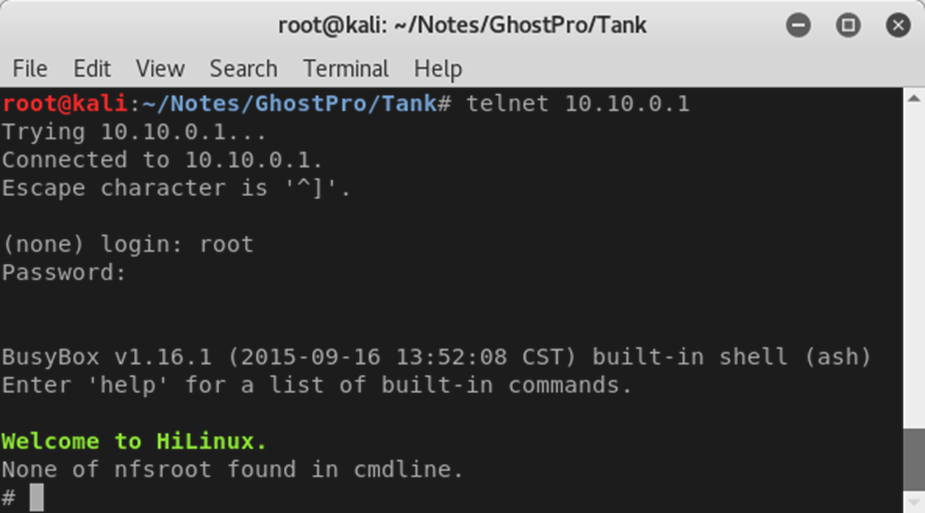
So anyone with access to the user’s local network or to the tank’s own Wi-Fi AP can get a root shell on the device. Further the Wi-Fi AP password is a weak/simple “12345678”. To round things off I found that you can change the tank password to whatever you want, once you’re either on the tank AP or on the local Wi-Fi network.
There’s basically no security preventing hostile takeover of the tank.
Full details here: Ghost Rover
Conclusion
If you’re thinking of buying and using any kind of ghost hunting hardware, know the risks! Make sure you only use professional gear, hardened against tampering or interception from ghouls or other malicious spirits.














