Short Video
Pet Microchip Scams and Data Leaks in the UK

Short Video
Technical debt exposed by ship connectivity
Short Video
Making smart heat pumps safer for the grid
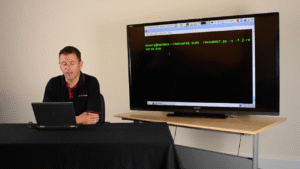
Hack Demo Video
Hacking with Chromecast and Alexa

Hack Demo Video
The Tapplock Bluetooth unlock attack

Hack Demo Video
Z-Wave Z-Shave downgrade attack
Hack Demo Video
A smart coffee machine
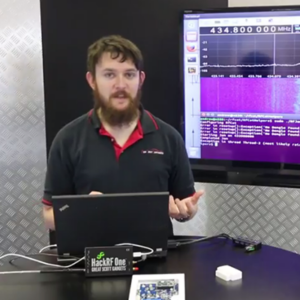
Hack Demo Video
Disabling Wireless Alarms 1 – Simple Jamming

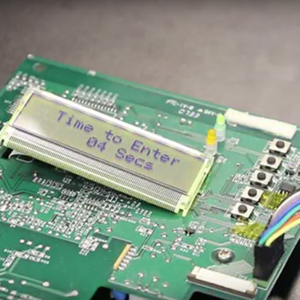
Hack Demo Video
Disabling Wireless Alarms 3 – PIN Brute Force

Hack Demo Video
Disabling Wireless Alarms 2 – Replay Attacks

Hack Demo Video
Disabling Wireless Alarms 4 – Attacking A Brand New Alarm
Hack Demo Video
Wireless Alarms – What To Look For In An Alarm

Hack Demo Video
Hacking the Mitsubishi Outlander PHEV SUV

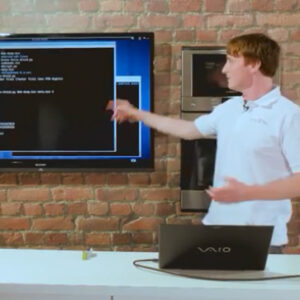
Hack Demo Video
Android PIN Patterns: A how-to video

Hack Demo Video
Exfiltrating data in ping packet padding: Video demo
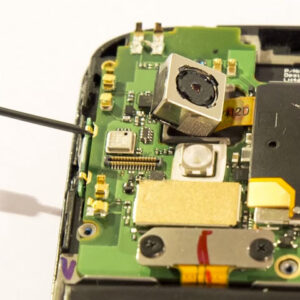
Hack Demo Video
Scraping Memory From Android Phones With JTAG: A how-to video
Hack Demo Video
How to bruteforce the PIN on Android: Nexus 4 video demo

Hack Demo Video
iPhone PIN Cracking: A video demonstration

Hack Demo Video
FireWire Memory Attack: A how-to video

Hack Demo Video
Hacking Android Through Accessibility Events: A how-to video
Hack Demo Video
ADB PIN Crack
Hack Demo Video
How to hack Tesco’s Android Hudl

Hack Demo Video
Teensy USB Connect Back Hack Video
Hack Demo Video
RFID Cloning With Proxmark
Hack Demo Video
Bypassing Antivirus To Deliver Malware With Code Packers
Hack Demo Video
Getting a divorce with iOS – Siri Bypass
Hack Demo Video
iOS PIN Cracking Video
Hack Demo Video
Keylogger Keyboard Hardware
Hack Demo Video
Wireless Probe Snooping
Hack Demo Video
Email Connect Back
Hack Demo Video