Any IoT vendor is no doubt aware that if their device has RF emissions and is to be sold in the USA, they must get FCC approval.
So, if their ‘thing’ is Wi-Fi, Bluetooth, Zigbee or whatever enabled, there is likely to be lots of useful information right here:
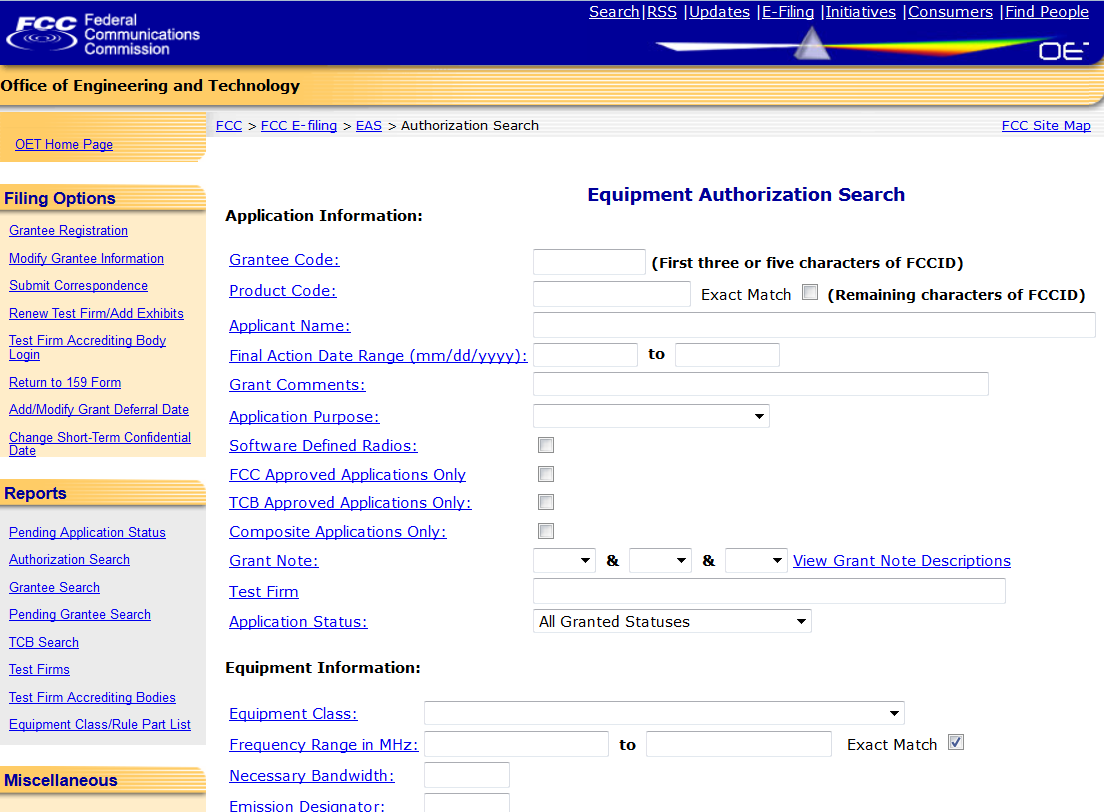
This is an ideal resource if you fancy looking for a device to research the security of. Our work on the smart thermostat started here, as we wanted to look for particular chipsets in thermostats before committing to buying some.
Standard information to be found there includes standards compliance, testing, RF exposure etc. Of interest to us are the internal and external photos of the device. Here’s one of the innards of a CloudPet, for example:

We can see the PCB layout, test pads, and types of chip, indicating how easy it will be to carry out hardware attacks such as firmware recovery, ready to extract the firmware and more.
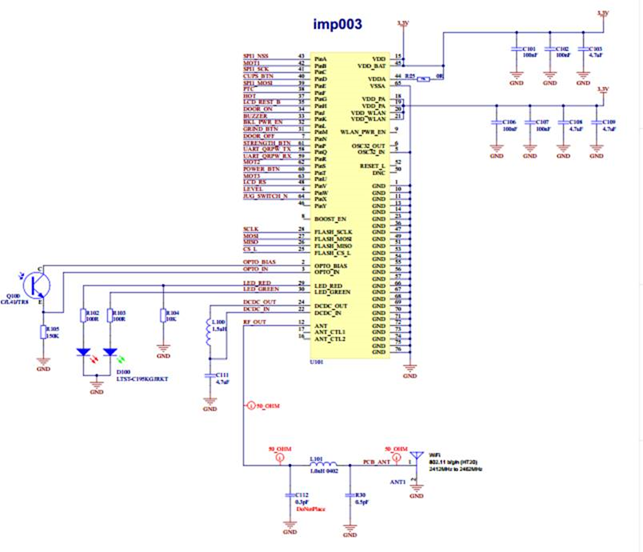
However, just occasionally, the vendor makes a mistake
The FCC are respectful of intellectual property, so the vendor usually asks for schematics to be kept confidential. It’s not ideal if IP is published on a publicly accessible web site, but the vendor has to actually ask for confidentiality!
Around one in ten of all FCC filings from IoT devices leave schematics in public view. One very recent filing drew our attention this week as it was from our favourite IoT product: the Wi-Fi kettle from Smarter Applications!
iKettle 2.0 was a big step forward in security from the first version, though still had issues.
An iKettle 3.0 hasn’t been launched yet, but it seems imminent, so imagine our surprise when we discovered that the Technical Description document wasn’t private:
Note that direct links to the FCC don’t always work, so to find the offending document, here’s how:
Start at the FCC EAS advanced search form here: https://apps.fcc.gov/oetcf/eas/reports/GenericSearch.cfm
Enter the ‘Applicant Name’ as the vendor you’re interested in, in this case ‘Smarter Applications LTD’
Select ‘detail’ from the first entry, then ‘Circuit Diagram’ from the exhibits list.
Bingo!
Google can find public circuit diagrams for you too, e.g. https://www.google.co.uk/search?q=site:https://fccid.io+circuit+diagram
What a fail!
I’m looking forward to getting hold of the Kettle 3.0, but the good news is that they’ve chosen an Electric Imp module. That’s a really good choice for security, so hopefully we won’t find much.
Advice
When filing FCC documentation for RF approval, ASK FOR CONFIDENTIALITY
Don’t leave your valuable intellectual property open to others to plagiarise, or to make hacking of your device easier
Obscurity is a useful extra layer of defence when it comes to hardware security. So take full advantage of it, don’t give away your secrets that easily.
Don’t get me wrong though; obscurity is no substitute for good hardware security, but desoldering and reballing ball grid arrays to find pinouts can be painful. Particularly if you don’t need to, as the pinout is published on the FCC web site!