I don’t claim to be an amazing speaker; I’m still in awe of great infosec speakers such as Mikko Hypponen, Charlie Miller, Mudge and many others.
However, I do keep being invited back to speak at events, so I guess I’m doing something right. Sometimes it’s a minor slot at a big event, but the following year an invitation to keynote turns up.
I speak in public at events 2-3 times per week, though the record was four separate conferences on one hectic day in London.
Why do I do it?
- I enjoy the challenge of public speaking
- It’s a good reason to do vanilla security research with my colleagues
- Just sometimes, I make people laugh. That alone makes it all worthwhile
Be Memorable (for the right reasons)
Why would someone be interested in what you have to say? What made you decide to apply to speak? What speaker did you see that motivated you to speak in public?
Why did you remember them? What was it about them that stuck in your mind? Answer those questions and you’ll be most of the way to being a great speaker.
I used to refuse to speak at security events such as BSides, OWASP, Defcon etc. I was paranoid that someone would call me out on a technical mistake I had made. Then I saw Charlie Miller speak at DC21. He and Chris Valasek were funny, entertaining and informative, yet little of their talk was about technical detail – it was about the consequences, with a peppering of how-to. There was some cool CAN hacking in there, but most of the talk was about the comedy story of hacking a Toyota Prius. How they accidentally drove it in to a wall, how they bricked it and returned it to the car dealer with the dashboard missing, how they hijacked the steering and nearly killed themselves.
Tell a story about the funny things that happened to you along the way. The ‘eureka’ moment, the blind alleys you went up for days, the frustrations.
I realised watching Charlie and Chris: few people would ever call you out, most had respect for you being brave enough to stand up in front of an informed audience.
Since then I’ve spoken at DC, BH, BSides, OWASP and many other technical conferences.
I’ve never been called out.
One important note though: always credit others if you use or quote their research. There is nothing wrong with standing on the shoulders of giants, so long as you give them a shout out in your talk.
Be Memorable (for the wrong reasons)
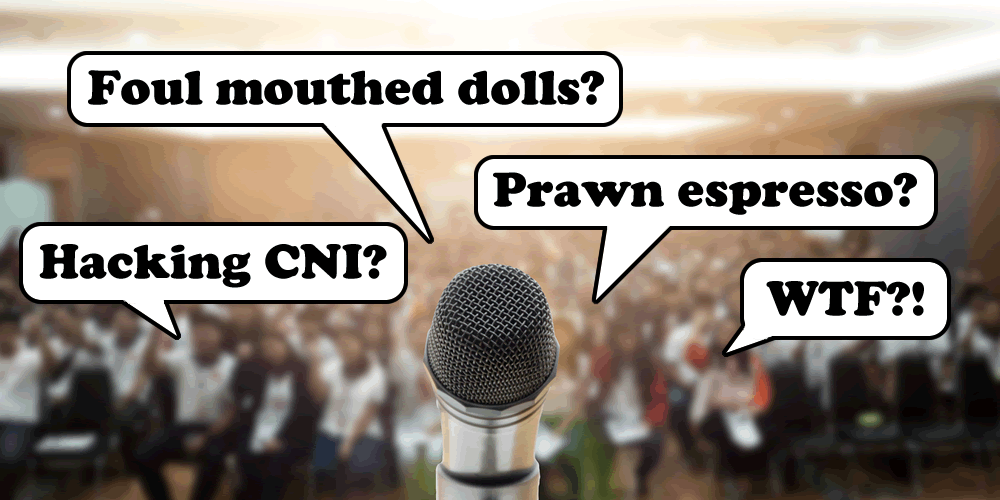
I’m known for speaking in public about IoT security, among many subjects. Sometimes the material writes itself. Learn from Miller & Valasek:
For example; a colleague found an interactive kids doll. We managed to get the innocent little thing swearing to order. The story was one of reverse engineering Android apps, static encryption keys and missing Bluetooth PINs, but the result was a comedy cussing toy that one could make phone calls on.
You’ll also know about my smart kettle. Again, a simple story of reverse engineering and exploiting 40-year old AT commands. It helped that it caught fire whilst I was giving a talk at BlackHat! That was unexpected & memorable, it also led to a long series of talks and blogs about boiling water remotely…
A few years ago, a colleague who will remain nameless flagged a smart vibrator to me. This set off a chain of events that led to some memorable research and perhaps the funniest / most privacy-invading talk we’ve ever given.
Practice and seek feedback
I don’t mean read through the slide deck in your head. I mean stand up, connect your laptop to a large screen (your TV?) and PRESENT it, even if it’s to a brick wall.
Hopefully you have some buddies who will be prepared to listen to you present it a couple of times. It’ll be clunky first time round, but you will get better. Get their feedback, but don’t just accept ‘you were great’ from them. Ask them pointed questions about where they switched off (they will, no matter how good friends they are!) and if they have any ideas for jokes or comedic moments
It might feel weird presenting to friends or family, but not half as weird as standing up in front of 2,500 people at a big conference.
Another option would be to video yourself. Get someone to video you presenting your whole talk. Standing up, in front of a screen. Then watch it all, however cringe-worthy it feels. Critique yourself, learn from yourself. Then watch some videos of some conference greats and contrast. What do they do that’s different to you?
Then try it all over again. Make another video. Don’t edit it, do it in one take. Don’t stop, just keep going however many slip-ups you make. That video may come in handy for post-talk material too.
Genuine practice will make you a great speaker.
Know Your Audience
Most conference and event organisers will want a conference call first. They want to know that you’re not going to do a sales pitch etc. Their fears can be allayed in moments.
What you need to know is about the audience. Who are they? What level of seniority are they? Are they hands on devs or project managers? Are they IoT entrepreneurs or crisis PR agencies? Are they Fortune 500 exec board members or junior staffers? You may need to change your talk somewhat depending on the audience; the level of technical detail may go over their heads.
That said, it’s a real skill to be able to take highly technical content to a non-tech audience. Can you explain it in steps that your own parents could understand? I remember overhearing a CEO explaining my kettle hack to another board member fairly accurately; security was now accessible to him, rather than being the usual ‘no, you can’t do that’ answer that comes from so many IT departments when asked about security.
Find out what subjects have been covered before. Check if any other security speakers have presented to the same audience before. If so, who? What went down well? Have similar subjects to yours been covered? If so, you’re going to look like a complete spanner if you cover the same damn topic.
Check out the agenda on the event web site. Review the bios of the other speakers & see what subjects they’re covering.
Entertain
How many talks have watched where you drifted off? Started looking at your phone. The speaker had lost you.
I’ve sat through so many talks where the subject was fascinating, but the speaker just read their slides. I switched off. I came to see the speaker to gain more than I could from just reading the slide deck online later. If you’re going to stand up and present, make sure you add something extra. Entertain your audience, get feedback from your peers and practice
Be funny. Or ironic
I had been speaking in public for a couple of years, perhaps once every couple of months. Then, at an event in London in 2007 (I still remember it clearly) – I got my first laugh. I hadn’t intended it, the joke was an accident. The audience was suddenly in the palm of my hand. I tried another infosec gag, they laughed at that too. I was enjoying myself even more than usual.
After the talk I had two more invites to speak.
Entertain your audience and they’ll love you. They will remember that your talk was funny long after they’ve forgotten the technical content.
However, don’t try to be a stand up comedian unless you’ve done it elsewhere. It’s very easy to misjudge humour and lose your audience. Besides, the audience is there to learn about infosec.
Be Punchy
If you can do the talk in 20 minutes, don’t stretch it to 40. Big cons usually have more slots available for short talks, so your chance of acceptance is higher.
I bet you can get 90% of your content across to an audience in 15 minutes or less. If you can’t, reconsider your content.
Have you ever watched a TED talk? If you haven’t, do. They’re a maximum of 18 minutes and I bet you will be riveted to it for the whole talk.
Some of the best talks I’ve given have been on a first outing to a new conference. They reluctantly found 20 minutes for me in the schedule, so I had to be fast-paced and concise. Make the points that matter, tell the funny stories that work best. I had 300 developers laughing almost continuously at a series of IoT coding screw-ups; the organiser had emailed to invite me back to their next event before I had even left the stage.
That organiser offered me a 40 minute slot at the next conference. I turned it down in favour of 20 minutes again.
If the audience like your talk, they can go read supporting material on your blog later. Don’t pad your talk; be punchy
Be Animated
If you’re doing a live demo, you’re going to need to be at your laptop keyboard for some of your talk. Don’t use that as an excuse to hide behind the lectern.
Make sure you have a lapel mike so you can get out there on stage. Move around the stage, talk to individuals in the audience, not over their heads. Make eye contact.
I always ask to speak in the ‘graveyard’ slot: that’s the one just after lunch where everyone is a bit sleepy after some food. No-one else wants to speak then and it gives me setup time on stage to prep demos and make sure everything is working.
Get out there and MAKE SOME NOISE. Vary the pace that you speak at. Pause. Speak quickly, change your tone, slow down. Use props. Ham it up a bit too. Don’t be monotonous: it’s boring.
Change where the audience are looking – keep moving around, don’t let them stare at the screen continuously. Screen. You. Prop. Walk to the other side of the stage. Lecturn. Screen. Keep it moving.
By the time I’m finished, the stage I’ve presented on is often a bombsite of props. There is stuff everywhere. I accidentally left a smart ‘adult’ toy at the lectern once. The next speaker struggled to compose himself when he walked on to speak. I had a guilty laugh inside…
Don’t read your slides
YAWN!
Is there anything worse than a speaker that reads their slides out?
However, too many speakers put up an image and talk around it. Here’s the problem: if someone wants to read your slides at another date, there’s no text for them to read.
If the talk was recorded, no problem, but so often the slides are meaningless without the presenter.
Consider adding enough brief key points that the reader can figure it out. A small amount of text can also help audience members understand your talk if they’re not fluent in the language you’re presenting in.
Diagrams RULE!
Don’t be afraid
Good conference speakers don’t just happen, they practice lots. They may look awesome on stage, but they all had to give a very first talk once
Some conferences offer speaking coaches and rookie tracks. Take advantage of them!
I’ve recently had the help of a speaking coach – I’ve been speaking publicly for years, but we can always learn.
If you’re stuck, drop me a line. I’ll help if I can.
But, don’t be afraid. Give it a go. Share your expertise and HAVE FUN!