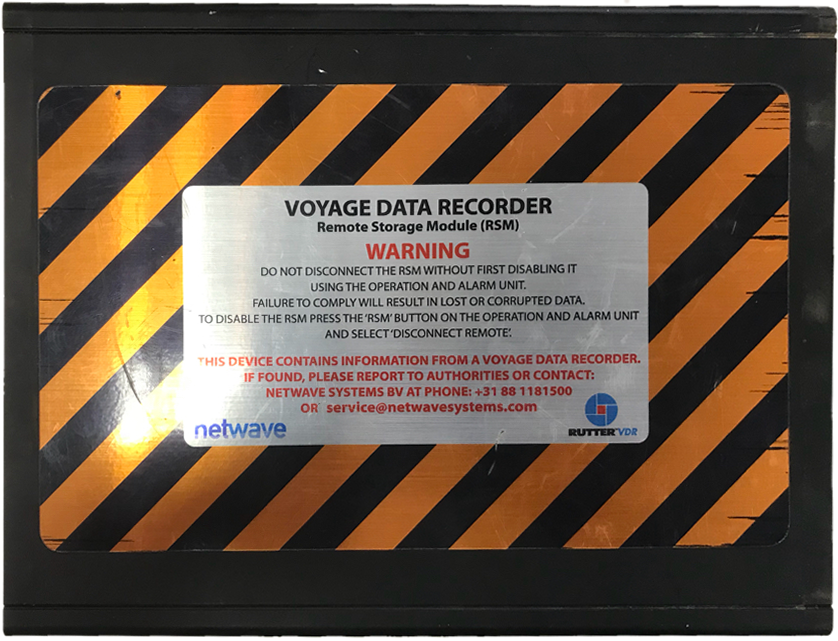
Whilst attempting to reverse engineer a Remote Storage Module (RSM) for a ship’s Voyage Data Recorder (VDR), we pulled some of the historic data. It was from a maritime salvage yard in India, but despite the disc having been wiped, forensic tools quickly recovered lots of interesting data:
Some of the entries in one of the logs caught my attention, led me down a rabbit hole and resulted in an interesting route to hack ship systems:
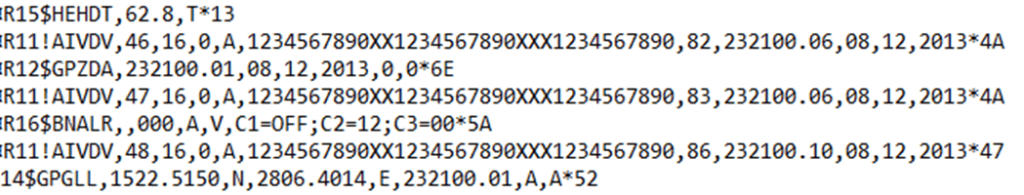
Now, most of the above are simply GPS NMEA sentences. There are some good reference sources online if you haven’t come across these before, for example Dale DePriest’s Navigation and GPS Articles.
Decoding NMEA GPS sentences
$GPGLL,1522.5150,N,2806.4014,E,232100.01,A,A*52
Decodes as ‘Geographic Position, 15 degrees 22 minutes 0.5150 seconds North, 28 degrees 6 minutes 0.4014 seconds East. Fix taken at 23:21:00 UTC, Data Active’ then the message checksum, which is a 2 byte XOR sum of the data.
So what, so you know where the ship was 5 years ago
Well, the other sentences are where it gets interesting:
HEHDT refers to True Heading.
GPZDA is the GPS time.
BNALR refers to a bridge navigational watch & alarm (BNWAS).
The alarm message above shows that the alarm dormant period has been exceeded and has not been acknowledged. Not good!
AIVDV refers to AIS data. I’ll come back to this, as it’s a subject all by itself.
…all clearly of interest to a Voyage Data Recorder, which acts as a ‘black box’ for ships, not that different to an aviation black box recorder.
A VDR will record, depending on vessel type and size, date and time, position, speed, heading, bridge audio, radio audio, radar data and ECDIS data.
More advanced models can also record engine RPM, an engine room dead mans switch, depth, bridge navigational watch alarms, rudder position, hull stress and more.
All very interesting to the hacker!
There’s more to NMEA than just GPS
NMEA GPS sentences are used to link navigational systems on board. Different brands of GPS can communicate with each other and pass position data and much more to the autopilot and ECDIS (that’s an electronic chart plotter / moving map).
However, NMEA messaging is also used to control multiple systems on board: RS485 serial connections control ballast pumps, propulsion, steering and plenty more.
But first you have to bridge on to the serial network
Any point on the serial network which touches the IP network is likely to have some connectivity to the satellite communications system. Updates to devices are often pulled over satcoms. Sometimes we see no segregation on the vessel network at all.
Read our earlier blogs about compromising satcom units – it really doesn’t take much to get on to a ships network.
Serial to IP convertors are often REALLY vulnerable, presenting web interfaces with default / blank creds or trivial authentication bypass. GPS terminals usually offer both ethernet and serial interfaces. Yet another opportunity to bridge on to the serial network.
Now we are talking serial. Now we can start to manipulate data.
Crashing ships without jamming or spoofing GPS
NMEA sentences are plain text and have no message authentication. It would be trivial to intercept the message data at either the GPS receiver, autopilot controller or elsewhere on the network and modify the vessel course.
$GPAPA and $GPAPB messages can be used to control the autopilot, so here’s how to use them:
$GPAPA,A,A,0.10,R,N,V,V,011,M,DEST,011,M*82
The critical components are the letter ‘R’ – that is the direction for the autopilot to steer, then also ‘011,M’ – that’s the magnetic heading to steer. Simply change R to L and the autopilot may steer the wrong way. A few degrees the wrong way for a few seconds at the wrong time in a congested area such as a separation scheme and a collision could happen.
Don’t forget the checksum at the end of the message though.
You might see $GPAPB messaging instead, but the format is essentially the same. The above message examples are taken from a great resource by Eric S. Raymond.
There are plenty of other insidious ways to affect GPS data, such as changing the GPS datum, maybe $GPGBS to suggest satellite data errors or perhaps $GPHSC to send a heading steering command to the helm.
Conclusion
We’ve just scratched the surface of NMEA messaging and Voyage Data Recorders here. In our next blog we will look at tampering with ballast pump controls using similar methods, plus the other ships systems that could be manipulated using serial communications.
In the meantime, refer to our Top 10 tactical advice blog about securing ships systems quickly.
Remind your officers of the watch to be vigilant and always look out of the bridge windows at the world outside. Don’t trust your ECDIS and other navigational systems to always be accurate.